
Threat Analysis On Cerber 5.0 Ransomware
Being a disastrous malware infection, Cerber 5.0 Ransomware has been recognized as one another big leap for the cerber virus family. The presumptions are high that this threat is being operated from long time by cyber hackers but yet not has been widespread and active. The appearance of this ransomware infection very clearly states that the developer of this threat are undoubtedly willing to take everything from this success. Now though the initial appearance at the new version of the afore mentioned infection do not reveal much about the modification that has been took place (as the virus still utilizes the .cerber extension regarding indication of the encrypted files), but still it can get presumed that definitely it has not been degraded in it's system's ruining potential.
According to researchers, chances are high that either the hackers have removed some of the potential malware vulnerabilities or have enhanced the efficiency of the ransom collection. We here malware experts at Remove Malware Virus ensures you of keeping updated about Cerber 5.0 Ransomware as soon as some new insignificant discovery emerges. But as for now, we can only recommend several PC users to initialize taking steps towards system security in a case if have not done it yet. Moreover PC users should also always install authentic security tool in their PC so as to face all this infection's attack and remove them permanently from the PC.
Likewise various other stubborn ransomware infections, Cerber 5.0 Ransomware has also been developed by online crooks for the sole purpose of earning more and more illicit profit from novice PC users. This infection has been labeled highly compatible with all the latest updated version of Windows OS. It lurks secretly inside the PC without taking the user's permission and then furthermore, following that conducts a series of disastrous activities in it. Initially takes complete control over the PC and scans it deeply in seek of the files it can harm. This malware threat has been proven capable of corrupting a wide range of file format.
Furthermore proceeding the scanning process, it performs the operation of file encryption on the files being detected compatible to it's corruption. Later on after the completion of the encryption procedure, generates a random note on the screen. The main reason behind displaying this note on the comprmised screen is to inform users that their file has been encrypted via using a strong encryption algorithm and thus now victims need to make payment of certain amount of ransom money in order to decrypt or regain the encrypted files. Now although such note appears authentic but yet it is advised not to trust them and to make payment to them as in reality it is just a scam designed to lurk users for gaining illicit profit from them.
Invasion Of Cerber 5.0 Ransomware
- Together with the attachment of spam emails.
- Along with the installation of freeware as well as shareware programs.
- Peer to peer file sharing Infectious USB drives
Therefore, regarding prevention of such unfortunate file encryption scenario as well as to operate PC in a healthy environment, it is very essential to remove Cerber 5.0 Ransomware quickly from the system.
Free Scan your Windows PC to detect Cerber 5.0 Ransomware
How To Remove Cerber 5.0 Ransomware Virus Manually
Step 1 : Restart your computer in safe with networking
- Restart your computer and keep pressing F8 key continuously.

- You will find the Advance Boot Option on your computer screen.

- Select Safe Mode With Networking Option by using arrow keys.
- Login your computer with Administrator account.
Step 2 : Step all Cerber 5.0 Ransomware related process
- Press the Windows+R buttons together to open Run Box.

- Type “taskmgr” and Click OK or Hit Enter button.

- Now go to the Process tab and find out Cerber 5.0 Ransomware related process.

- Click on End Process button to stop that running process.
Step 3 : Restore Your Windows PC To Factory Settings
System Restore Windows XP
- Log on to Windows as Administrator.
- Click Start > All Programs > Accessories.

- Find System Tools and click System Restore.
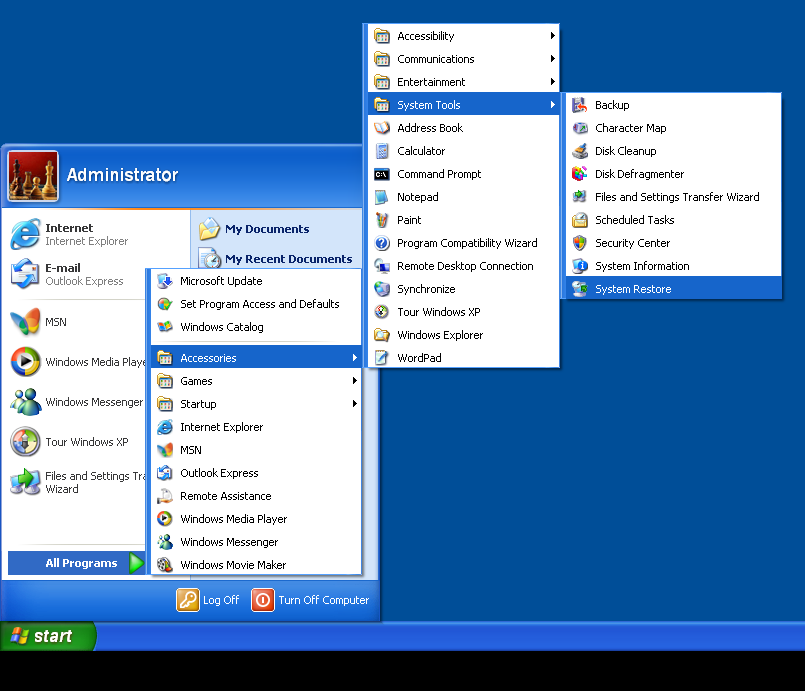
- Select Restore my computer to an earlier time and click Next.
- Choose a restore point when system was not infected and click Next.
System Restore Windows 7/Vista
- Go to Start menu and find Restore in the Search box.

- Now select the System Restore option from search results.
- From the System Restore window, click the Next button.
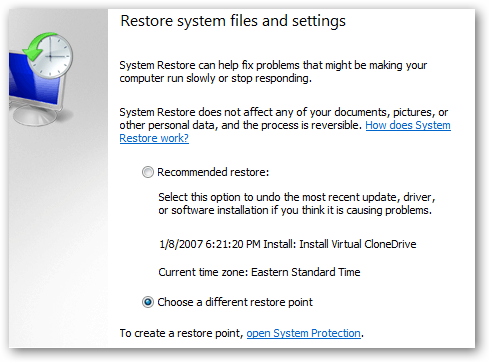
- Now select a restore points when your PC was not infected.
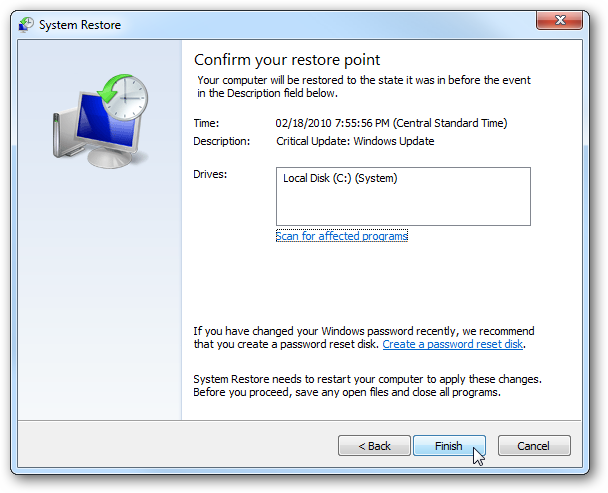
- Click Next and follow the instructions.
System Restore Windows 8
- Go to the search box and type Control Panel.

- Select Control Panel and open Recovery Option.

- Now Select Open System Restore option.

- Find out any recent restore point when your PC was not infected.

- Click Next and follow the instructions.
System Restore Windows 10
- Right click the Start menu and select Control Panel.
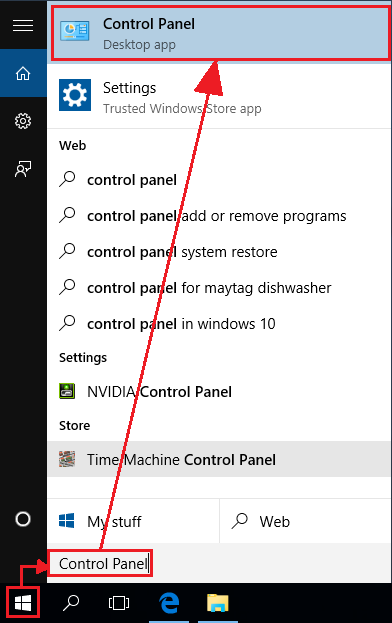
- Open Control Panel and Find out the Recovery option.

- Select Recovery > Open System Restore > Next.

- Choose a restore point before infection Next > Finish.

Hope these manual steps help you successfully remove the Cerber 5.0 Ransomware infection from your computer. If you have performed all the above manual steps and still can’t access your files or cannot remove this nasty ransomware infection from your computer then you should choose a powerful malware removal tool. You can easily remove this harmful virus from your computer by using third party tool. It is the best and the most easy way to get rid of this infection.
If you have any further question regarding this threat or its removal then you can directly ask your question from our experts. A panel of highly experienced and qualified tech support experts are waiting to help you.




