CryptON CryptoLocker Description
CryptON CryptoLocker is ransomware-type trojan horse that targets PC running Microsoft Windows. This week, the ransomware was discovered by Jakub Kroustek. He submitted some evidences against the ransomware and warned computer users to be cautious. Actually, the ransomware encodes files using a custom cipher generated by combining RSA-2048 and AES-256 encryption standards. When file encryption is completed, you see files in the most commonly used data containers are changes as “[original-file-name].ID-[victim-ID][email protected]_”. For instance, ‘Index.php’ file will be transcoded as ‘Index.php.id-278349735_steaveiwalker@indiacom_’. Moreover, CryptON CryptoLocker also replaces your desktop wallpaper and drops a text file named ‘COMO_ABRIR_ARQUIVOS.txt’ inside each folder containing encrypted files. Primarily, this ransomware encrypts certain types of files saved on local and mounted network drives using custom cipher with private key stored only on the ransomware’s C&C servers.
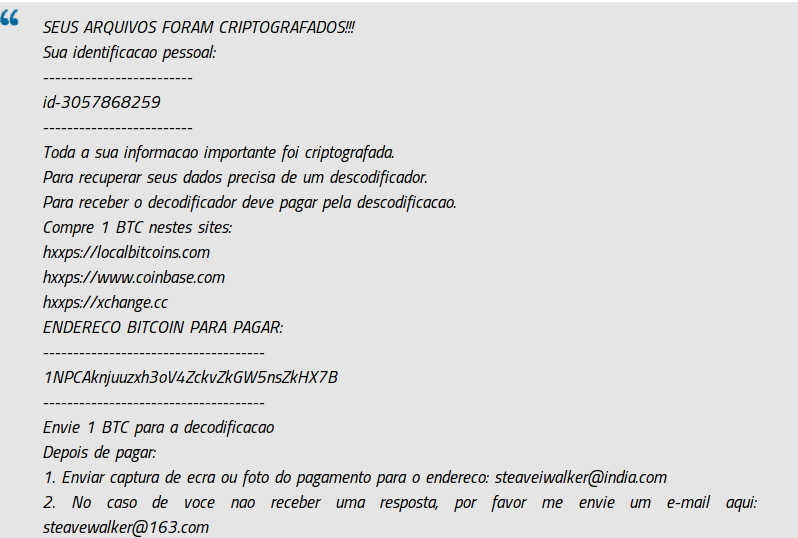
CryptON CryptoLocker then displays a message which offers to decipher the data if a ransom payment of 1 BTC (equivalent to $1,000) is made within given time via Bitcoin account. It also threatens to delete the private key permanently if the deadline of 48 hours pass. Researchers from many online security firm say that ransom should not be paid. They offer victims to make use of Data Recovery Software or System Restore Point or Backup Drives in order to recover data. Since, CryptON CryptoLocker is latest, investigation on it is undergoing, soon enough they might release a free decryption tool as well. Though, either you can utilize Alternative Options or wait for Free Decryption Tool but you should not pay off ransom. Because, if you do financial transaction using the infected computer, there is a high possibility that your online banking credentials will be stolen and used against your will.
CryptON CryptoLocker Attacks – Prevention Ideas
First, if you keep efficient Antivirus software installed, updated and activated then infection like CryptON CryptoLocker can’t infiltrate your computer. As you may have heard that Antivirus Software should be up-to-date always because each day hundreds of threats are being unleashed. Regular updates allows Antivirus to protect your computer from latest viruses like CryptON CryptoLocker and Ramsomeer Ransomware.
Additionally, you have to pay attention while installing software updates or Windows updates off the Internet. Even, you should never execute spam emails attachments and also never click embedded links. As of now, you have enough information. You can proceed CryptON CryptoLocker removal process.
Video – Get Rid of CryptON CryptoLocker (Removal Guide)
Free Scan your Windows PC to detect CryptON CryptoLocker
Free Scan your Windows PC to detect CryptON CryptoLocker
A: How To Remove CryptON CryptoLocker From Your PC
Step: 1 How to Reboot Windows in Safe Mode with Networking.
- Click on Restart button to restart your computer
- Press and hold down the F8 key during the restart process.
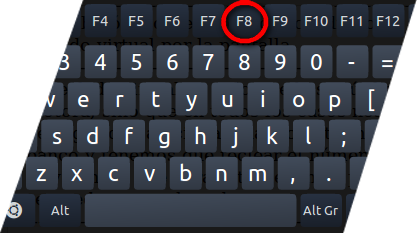
- From the boot menu, select Safe Mode with Networking using the arrow keys.
Step: 2 How to Kill CryptON CryptoLocker Related Process From Task Manager
- Press Ctrl+Alt+Del together on your keyboard

- It will Open Task manager on Windows
- Go to Process tab, find the CryptON CryptoLocker related Process.
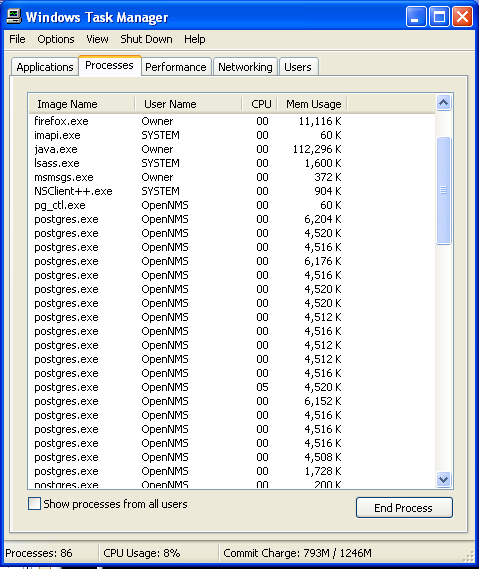
- Now click on on End Process button to close that task.
Step: 3 Uninstall CryptON CryptoLocker From Windows Control Panel
- Visit the Start menu to open the Control Panel.
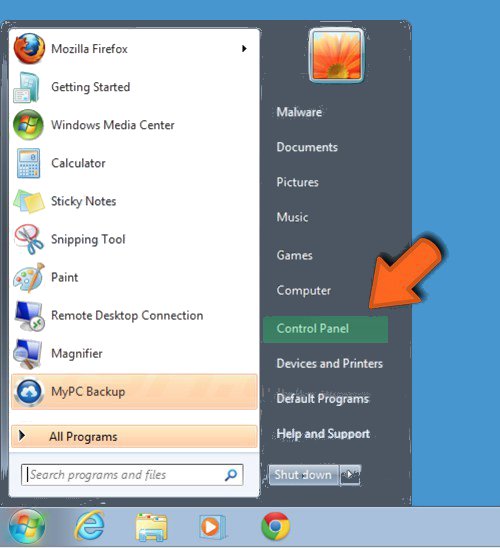
- Select Uninstall a Program option from Program category.
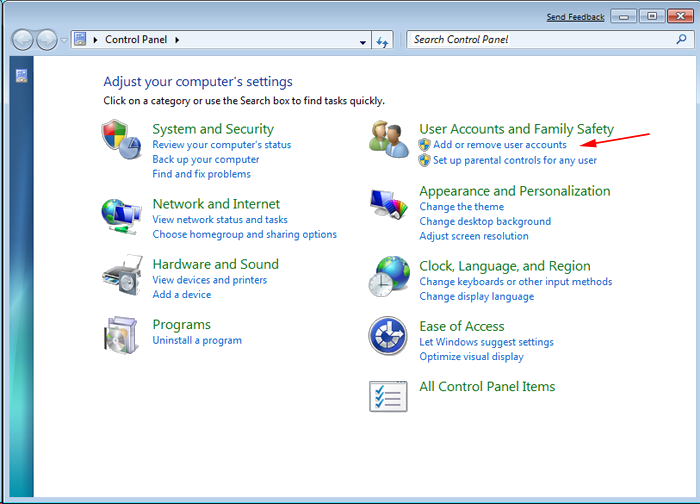
- Choose and remove all CryptON CryptoLocker related items from list.

B: How to Restore CryptON CryptoLocker Encrypted Files
Method: 1 By Using ShadowExplorer
After removing CryptON CryptoLocker from PC, it is important that users should restore encrypted files. Since, ransomware encrypts almost all the stored files except the shadow copies, one should attempt to restore original files and folders using shadow copies. This is where ShadowExplorer can prove to be handy.
Download ShadowExplorer Now
- Once downloaded, install ShadowExplorer in your PC
- Double Click to open it and now select C: drive from left panel
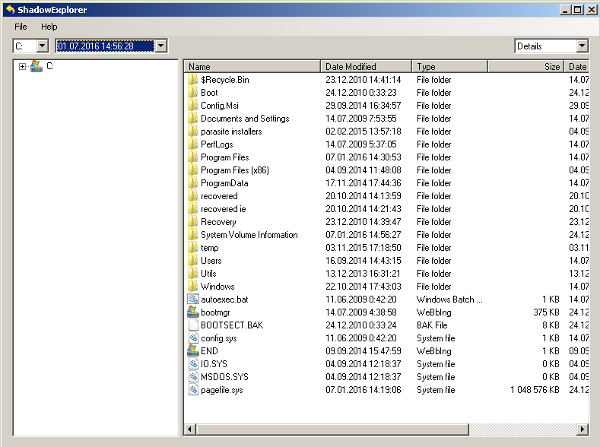
- In the date filed, users are recommended to select time frame of atleast a month ago
- Select and browse to the folder having encrypted data
- Right Click on the encrypted data and files
- Choose Export option and select a specific destination for restoring the original files
View the Following Video Guide to Terminate CryptON CryptoLocker from PC
Method:2 Restore Windows PC to Default Factory Settings
Following the above mentioned steps will help in removing CryptON CryptoLocker from PC. However, if still infection persists, users are advised to restore their Windows PC to its Default Factory Settings.
System Restore in Windows XP
- Log on to Windows as Administrator.
- Click Start > All Programs > Accessories.

- Find System Tools and click System Restore
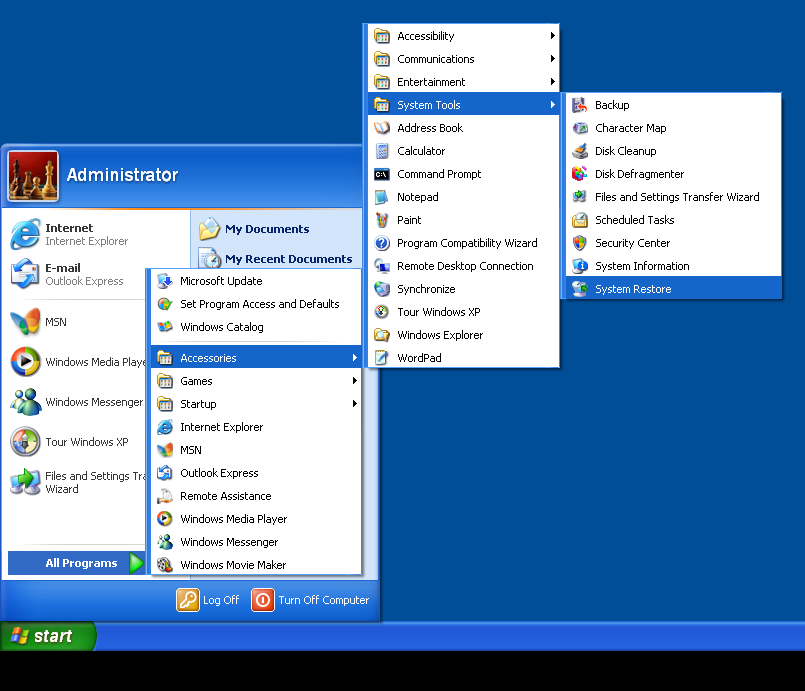
- Select Restore my computer to an earlier time and click Next.
- Choose a restore point when system was not infected and click Next.
System Restore Windows 7/Vista
- Go to Start menu and find Restore in the Search box.

- Now select the System Restore option from search results
- From the System Restore window, click the Next button.

- Now select a restore points when your PC was not infected.

- Click Next and follow the instructions.
System Restore Windows 8
- Go to the search box and type Control Panel

- Select Control Panel and open Recovery Option.

- Now Select Open System Restore option

- Find out any recent restore point when your PC was not infected.

- Click Next and follow the instructions.
System Restore Windows 10
- Right click the Start menu and select Control Panel.

- Open Control Panel and Find out the Recovery option.

- Select Recovery > Open System Restore > Next.

- Choose a restore point before infection Next > Finish.

Method:3 Using Data Recovery Software
Restore your files encrypted by CryptON CryptoLocker with help of Data Recovery Software
We understand how important is data for you. Incase the encrypted data cannot be restored using the above methods, users are advised to restore and recover original data using data recovery software.



