Complete Details on CTB Locker (Critoni) Ransomware
CTB Locker (Critoni) Ransomware is also known as a Curve-Tor-Bitcoin Locker or CTB-Locker file encryptor Trojan which uses the Tor browser in order to obfuscate its network activity with its C&C (Command & Control) servers. While the threat's technical innovations are noteworthy, for the victims, this ransomware endangers their system files in much the same ways as other noxious ransomware does, with a demanded ransom money payment for the file restoration. Although, proper data and file backup strategies can mitigate the effects of such malware attack. Also, an anti-malware tool should be used to remove this hazardous ransomware and its all related threats, as quickly as possible.
How Does CTB Locker (Critoni) Ransomware Works?
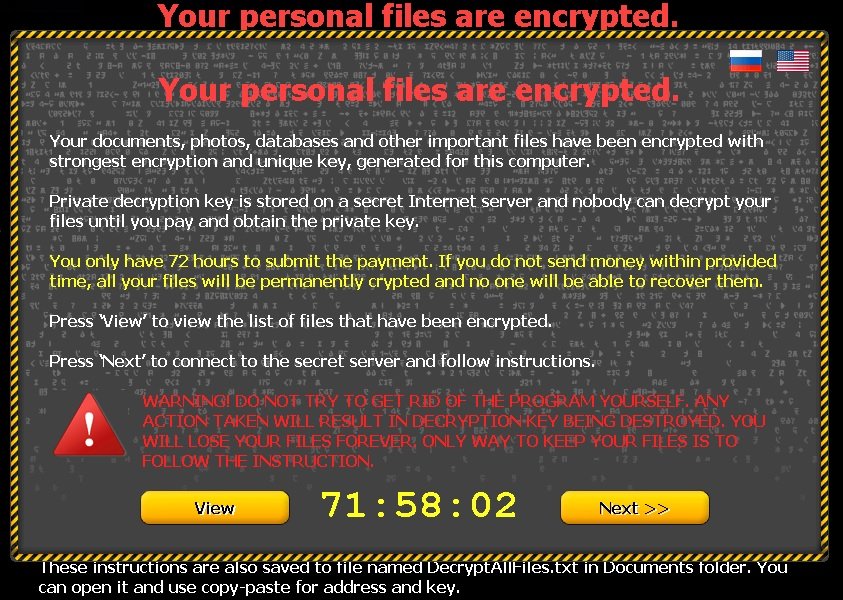
It is one of the various file encryption ransomware virus that may install itself through the network vulnerabilities leveraged in attacks which tend to be implemented by the web-based threats like Angler Exploit Kit. Just like the ransomware's installation rarely requires any permission from its victims, its malicious attacks also takes place automatically by targeting and encrypting specific vital file types on your machine. Images, audio files and documents all may be made unreadable, due to CTB Locker (Critoni) Ransomware which shows the warning TXT files onto the system screen. Along with asking its victims for the Tor-based payment plan in order to return their important files to them, the threat also initiates communications with the Command & Control server.
Such functionality could let this ransomware receive the instructions for other nasty attacks or transmit the information. The CTB Locker (Critoni) Ransomware virus implements this feature in a semi-innovative fashion by using the Tor browser in order to prove anonymity to the Command & Control servers, as well. Other notorious threats have pioneered this technique, including the banking trojans, but the security experts have yet to see any other file encrypting trojan viruses using Critoni Ransomware's anonymity methodology. In addition, this anonymity could make it more and more difficult for the malware researchers to disrupt its server infrastructure or assist the law enforcement with apprehending the threat developers.
Furthermore, the CTB Locker (Critoni) Ransomware publishers are not necessarily the same individuals as its coders, the malware has been seen being sold to the third parties on the suspicious forums for sums of $3000. While this ransomware does boast of an exceptionally strong encryption method that would make the decryption quite difficult and there are other means of preserving your system files from the file encryptor Trojan's attacks. For this kind of reasons, the system security researchers always recommend that computer users with irreplaceable data, use the remote file backups in conjunction with the removable hard drives, cloud services and other similar storage options.
Note: The infection rates for CTB Locker (Critoni) Ransomware are increasing at alarming rates. Thus, we have found where the method of its encrypting files will ultimately make those files inaccessible and they cannot be decrypted by using any method, even by paying the ransom money through the offered payment through the ransomware lock screen.
Free Scan your Windows PC to detect CTB Locker (Critoni) Ransomware
Remove CTB Locker (Critoni) Ransomware From Your PC
Step 1: Remove CTB Locker (Critoni) Ransomware in Safe Mode with Command Prompt
- First of all disconnect your PC with network connection.
- Click restart button and keep pressing F8 key regularly while system restart.

- You will see “Windows Advanced Options Menu” on your computer screen.
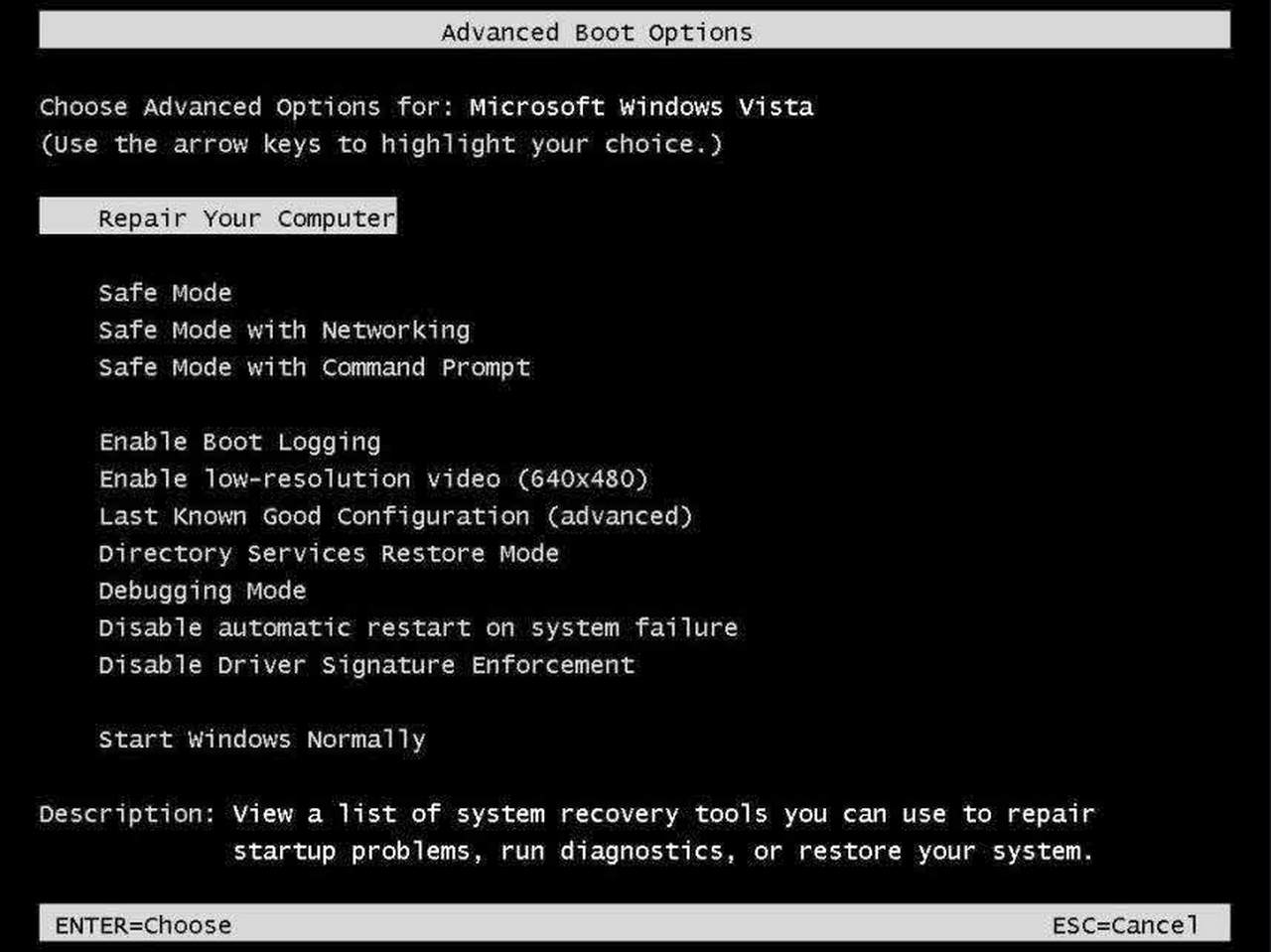
- Select “Safe Mode with Command Prompt” and press Enter key.
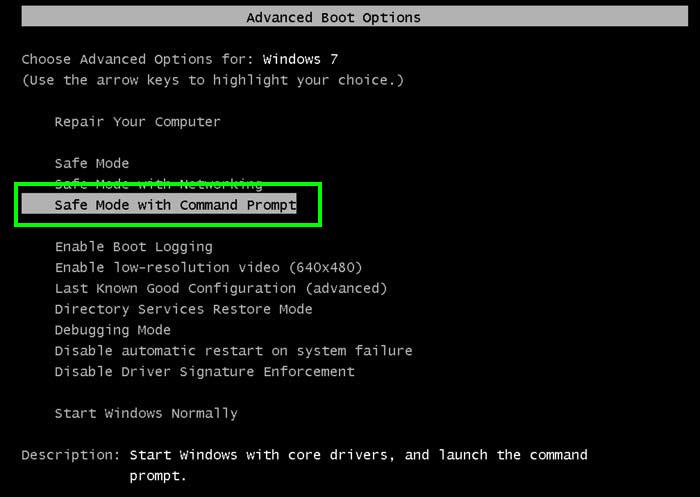
- You must login your computer with Administrator account for full privilege.

- Once the Command Prompt appears then type rstrui.exe and press Enter
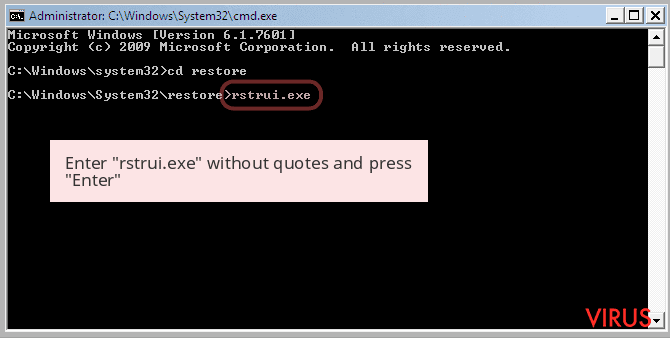
- Now follow the prompts on your screen to complete system restore.
Step 2: Remove CTB Locker (Critoni) Ransomware using MSConfig in Safe Mode:
- Power off your computer and restart again.
- While booting press the “F8 key” continuously to open “Windows Advanced Options Menu”.

- Use the arrow keys to select “Safe Mode” option and press Enter key.

- Once system get started go to Start menu. Type “msconfig” in the search box and launch the application.

- Go to the Startup tab and look for files from %AppData% or %Temp% folders using rundll32.exe. See an example below:
C:\Windows\System32\rundll32.exe C:\Users\username\appdata\local\temp\regepqzf.dll,H1N1
- Disable all the malicious entries and save the changes.
- Now restart your computer normally.
Step 3 : Kill Malicious Process Related To CTB Locker (Critoni) Ransomware
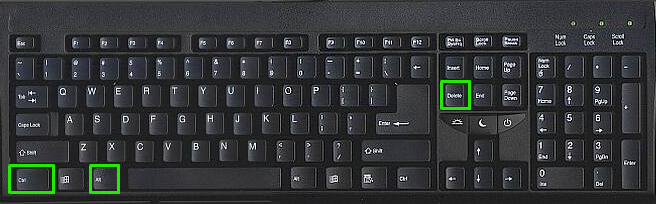
- Press Alt+Ctrl+Del buttons together.
- It will open the Task manager on your screen.
- Go to Process Tab and find CTB Locker (Critoni) Ransomware related process.
- Click the End Process Now button to stop the running process.
Step 4 : Remove CTB Locker (Critoni) Ransomware Virus From Registry Entry
- Press “Windows + R” key together to open Run Box.

- Type “regedit” and click OK button.

- Find and remove CTB Locker (Critoni) Ransomware related entries.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnceEx
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunServices
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunServicesOnce
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Runonce
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunServices
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunServicesOnce
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run
Now hopefully you have completely removed the CTB Locker (Critoni) Ransomware virus from your computer. If you are still get ransom message from the threat or unable to access your files, then it means that virus still remain into your computer. In such situation you don’t have any other option except removing this virus using any powerful malware removal tool.
A Video Guide To Get Rid of CTB Locker (Critoni) Ransomware
Whereas if you have any backup of your infected or encrypted files, then you can also reinstall your Windows OS. This will erase all your files and data as along with the CTB Locker (Critoni) Ransomware infection. You will get a completely empty computer system with no files. Now you can use your backup to get your files. If you don’t have any backup then using malware removal tool is a better option for you.
If you have any query or question regarding your computer, then you can easily ask your problem to our experts. Go to the Ask Any Question page and get the answer for your query directly from out experts.




