Ocelot Locker Ransomware – What’s the scam behind it?
On 9th January, Ocelot Locker Ransomware is discovered by the security experts from Emsisoft. The ransomware pretends to encrypt files but the truth is it doesn’t encrypt any file. Instead, it locks affected PC’s screen and display scary ransom note and ask to pay ransom 0.3 Bitcoin (270.82 USD). Apparently, Ocelot Locker Ransomware is a screen locker Trojan horse, not designed to infect files saved on the local disk or removable device. Thus, we can say that the ransomware is identical to Freedom Ransomware and CryptoWall Ransomware. They use social engineering tactics and scare victims to lure them into paying off ransom. This money extorting technique is called scam created by cyber extortionists.

Ocelot Locker Ransomware ransom note displays the given ransom note:
“-All your personal documents, videos, mp3 files, images,
or any other files have been encrypted with a military
grade encryption key. The key has been stored on our
server. For you to get this key you will have to pay 00.3
BTC (25 USD) and the key will be given to you’ The Small Ransom Payment is Intended to Serve as an Incentive for Users to Pay-”
Since, Ocelot Locker Ransomware doesn’t encipher any files, there is no need to use decryption tool or data recovery software. Once, you remove the ransomware from your computer, you will be able to access your files and system settings as well. So that keep calm and gather necessary information about this cryptomalware. It might help you to prevent such infection in future.
Ocelot Locker Ransomware – Infiltration Tactics
In most cases, the ransomware infiltrates computer via spam emails containing exploit kit or embedded code or Script as attachment. When you double click such attachment, it gets activated and downloads components of Ocelot Locker Ransomware without your awareness. It is also spread through Trojan droppers that are designed to intrude into Windows and after connecting to a malicious server starts downloading package of Ocelot Locker Ransomware. Moreover, by installing fabricated updates and trojanized software or pirated software copy may also bring up the ransomware infection. You may have noticed that while installing pirated games or software, antivirus throws infected files alert and blocks the installation process. But some users, disable Antivirus shield and forcefully install pirated software, later on they find vulnerabilities and infections on the computers.
Therefore, in order to keep your computer safe and clean, you must keep an Antivirus software installed and up-to-date on your each computer. Remember, your system firewall should be turned on always. As of now, follow the given Ocelot Locker Ransomware removal guide and unlock your PC screen.
Free Scan your Windows PC to detect Ocelot Locker Ransomware
Free Scan your Windows PC to detect Ocelot Locker Ransomware
A: How To Remove Ocelot Locker Ransomware From Your PC
Step: 1 How to Reboot Windows in Safe Mode with Networking.
- Click on Restart button to restart your computer
- Press and hold down the F8 key during the restart process.
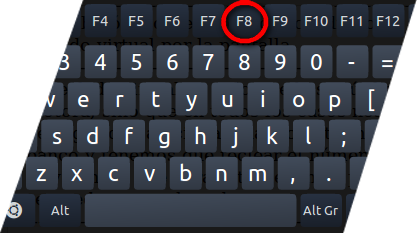
- From the boot menu, select Safe Mode with Networking using the arrow keys.
Step: 2 How to Kill Ocelot Locker Ransomware Related Process From Task Manager
- Press Ctrl+Alt+Del together on your keyboard

- It will Open Task manager on Windows
- Go to Process tab, find the Ocelot Locker Ransomware related Process.
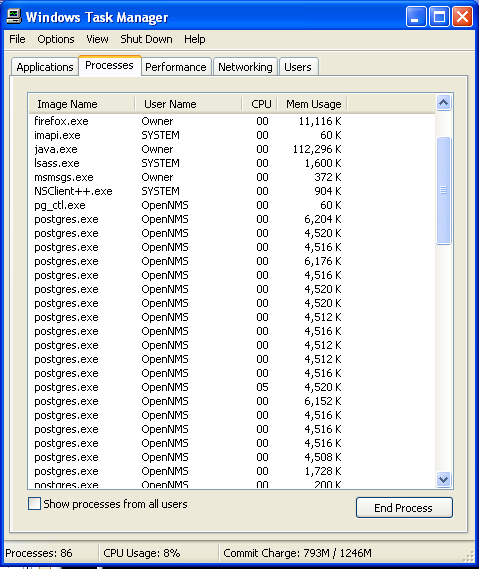
- Now click on on End Process button to close that task.
Step: 3 Uninstall Ocelot Locker Ransomware From Windows Control Panel
- Visit the Start menu to open the Control Panel.
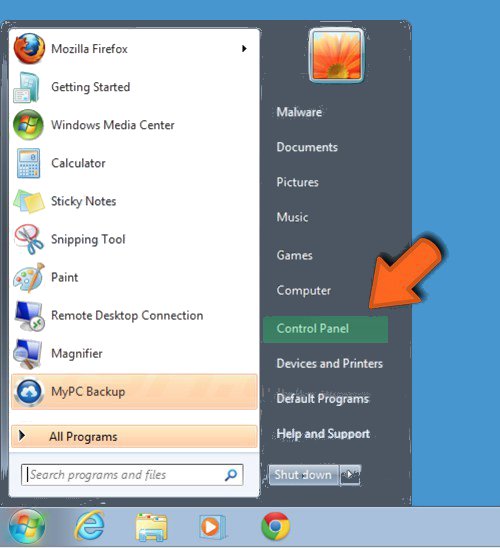
- Select Uninstall a Program option from Program category.
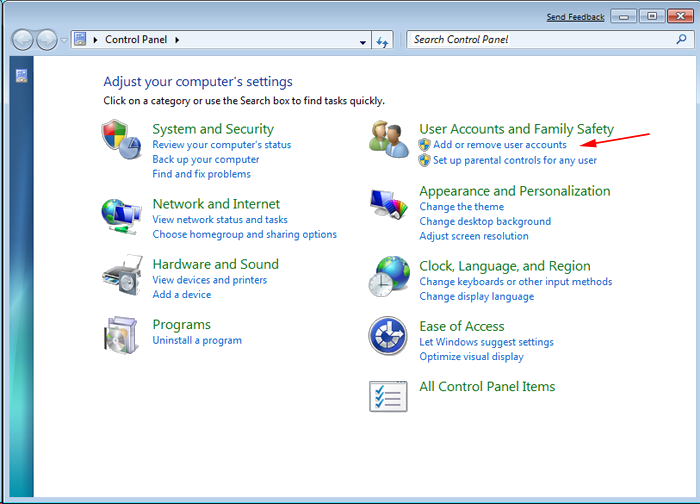
- Choose and remove all Ocelot Locker Ransomware related items from list.

B: How to Restore Ocelot Locker Ransomware Encrypted Files
Best Tutorial Guide To Remove Ocelot Locker Ransomware
Method: 1 By Using ShadowExplorer
After removing Ocelot Locker Ransomware from PC, it is important that users should restore encrypted files. Since, ransomware encrypts almost all the stored files except the shadow copies, one should attempt to restore original files and folders using shadow copies. This is where ShadowExplorer can prove to be handy.
Download ShadowExplorer Now
- Once downloaded, install ShadowExplorer in your PC
- Double Click to open it and now select C: drive from left panel
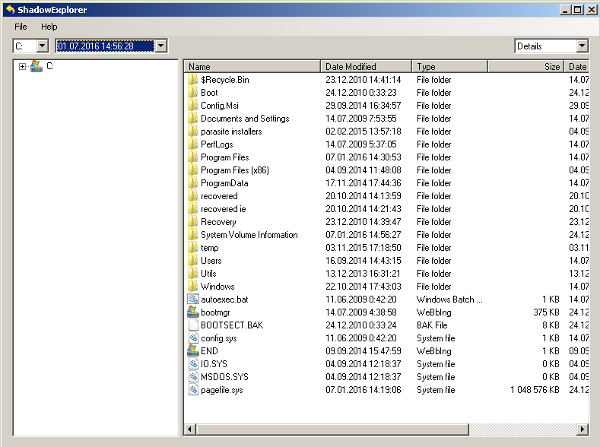
- In the date filed, users are recommended to select time frame of atleast a month ago
- Select and browse to the folder having encrypted data
- Right Click on the encrypted data and files
- Choose Export option and select a specific destination for restoring the original files
Method:2 Restore Windows PC to Default Factory Settings
Following the above mentioned steps will help in removing Ocelot Locker Ransomware from PC. However, if still infection persists, users are advised to restore their Windows PC to its Default Factory Settings.
System Restore in Windows XP
- Log on to Windows as Administrator.
- Click Start > All Programs > Accessories.

- Find System Tools and click System Restore
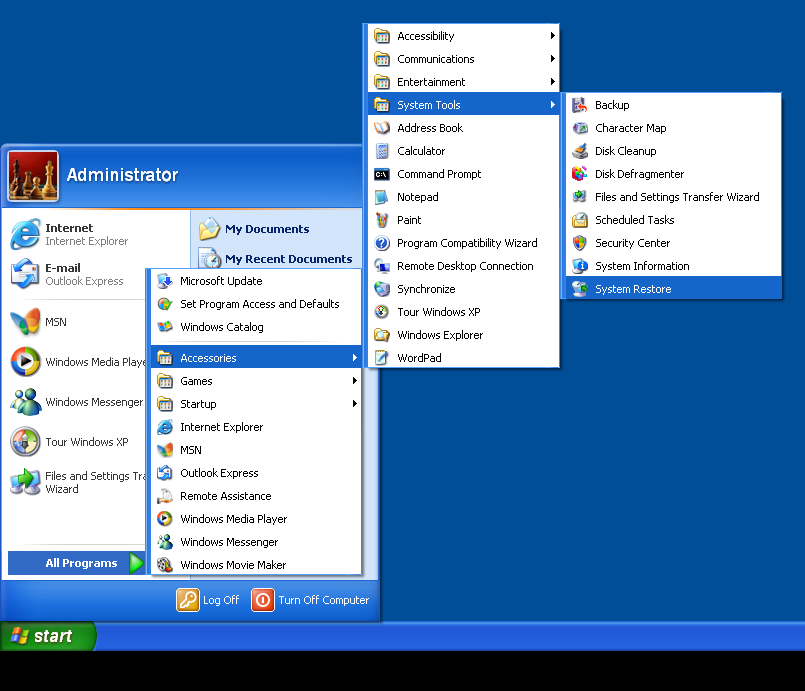
- Select Restore my computer to an earlier time and click Next.
- Choose a restore point when system was not infected and click Next.
System Restore Windows 7/Vista
- Go to Start menu and find Restore in the Search box.

- Now select the System Restore option from search results
- From the System Restore window, click the Next button.

- Now select a restore points when your PC was not infected.

- Click Next and follow the instructions.
System Restore Windows 8
- Go to the search box and type Control Panel

- Select Control Panel and open Recovery Option.

- Now Select Open System Restore option

- Find out any recent restore point when your PC was not infected.

- Click Next and follow the instructions.
System Restore Windows 10
- Right click the Start menu and select Control Panel.

- Open Control Panel and Find out the Recovery option.

- Select Recovery > Open System Restore > Next.

- Choose a restore point before infection Next > Finish.

Method:3 Using Data Recovery Software
Restore your files encrypted by Ocelot Locker Ransomware with help of Data Recovery Software
We understand how important is data for you. Incase the encrypted data cannot be restored using the above methods, users are advised to restore and recover original data using data recovery software.



