Brief Details on [email protected] Ransomware
Cyber security analysts recently discovered a new file-encrypting virus named [email protected] Ransomware which was distributed onto the user's machine through a massive spam email campaign. In order to see if the anti-virus programs are able to detect the malicious codes of this threat and block the malware, the creators uploaded a copy of this ransomware to an online security platform. Luckily, the security investigators able to obtained a sample of this virus and managed to create a threat signature for the ransomware.

However, you should never try to let your guard down, because it may be possible that [email protected] Ransomware arrive in your mailbox as a bogus DOCX or PDF file with double extension. The racketeers behind this ransomware might use the macro-enabled documents in order to bypass the detection from installed anti-virus tools and then lure the innocent computer users into downloading and installing the malware hide behind the legitimate looking doc file. It may suggest the inexperienced system users to enable the functionality of macro file onto the corrupt document.
Anti-virus Vendors Also Detect [email protected] Ransomware as:
- Trojan.Win32.Generic!BT
- MSIL/Filecoder.IH
- malicious_confidence_100% (W)
- TrojWare.Win32.Filecoder
- Win32:Malware-gen
- Trojan[Ransom]/Win32.AGeneric
- Trojan.MSIL.Krypt.4
[email protected] Ransomware : Working Principles
Research report revealed that the malware is especially programmed by the team of cyber extortionists which follow the example of other notorious threat like EyLamo and Kryptonite. At the time [email protected] Ransomware attack occurs, it encrypts the files stored on local disks and removable data storage device connected to the affected machine. Besides, one of the most negative properties of this ransomware is that it deletes the Shadow Volume copies of the encrypted data in order to prevent the PC users from recovering the files using other methods.
After encrypting the computer files, the malware display a ransom note as a small program window, which consists all the details related to data encryption. Usually, it targets eBooks, presentations, spreadsheets, audio, photos, video, text, PDFs, spreadsheets and the databases. Unfortunately, the cyber security experts are to able to discover its decryption tool, so the victimized system users will not be able to restore their valuable files. In case, if you have the backups and archived copies of encoded files, then you may have the chance to restore your computer files without paying ransom money. However, before go for the data recovery procedure, you need to delete [email protected] Ransomware completely from your PC.
Free Scan your Windows PC to detect [email protected]
How To Remove [email protected] From Your PC
Start Windows in Safe Mode with Networking.
- Click on Restart button to restart your computer
- Press and hold down the F8 key during the restart process.

- From the boot menu, select Safe Mode with Networking using the arrow keys.
- Now your computer will get started in Safe Mode with Networking.
End [email protected] Related Process From Task Manager
- Press Ctrl+Alt+Del together on your keyboard.

- Task manager Windows will get opened on your computer screen.
- Go to Precess tab, find the [email protected] related Process.
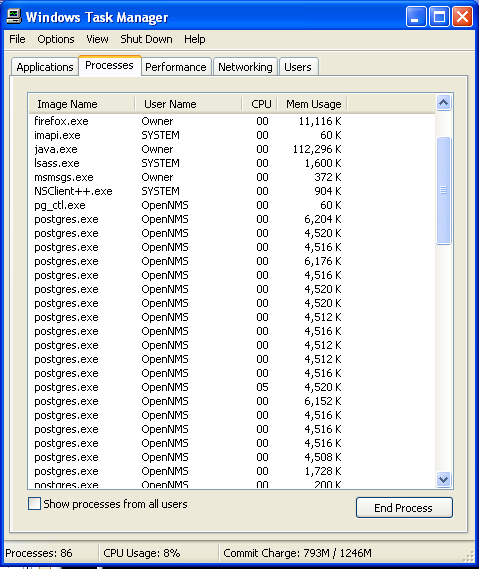
- Now click on on End Process button to close that task.
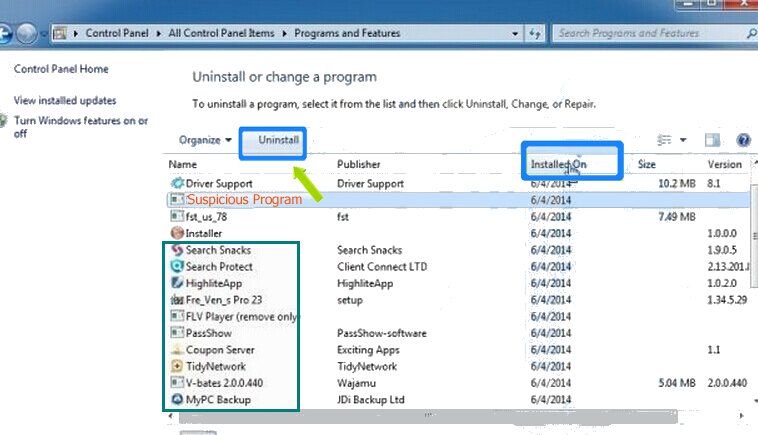
Uninstall [email protected] From Windows 7 Control Panel
- Visit the Start menu to open the Control Panel.
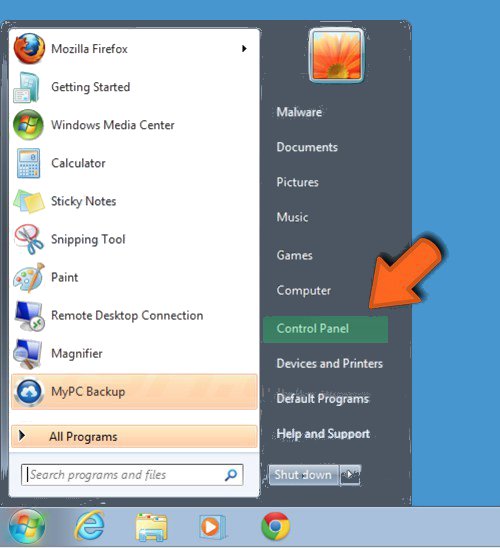
- Select Uninstall a Program option from Program category.
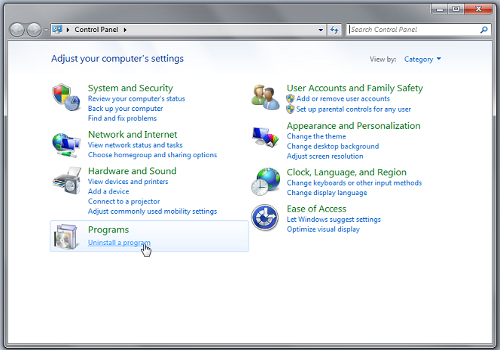
- Choose and remove all [email protected] related items from list.
Uninstall [email protected] From Windows 8 Control Panel
- On right edge of screen, Click on Search button and type “Control Panel”.

- Now choose the Uninstall a Program option from Programs category.
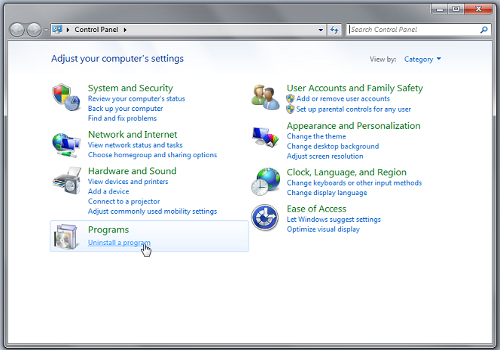
- Find and delete [email protected] related items from the programs list.

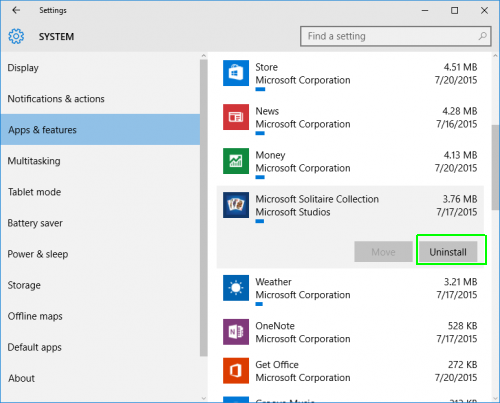
Delete [email protected] From Windows 10 Control Panel
- Click on Start button and search Control Panel from Search Box.

- Got to Programs and select the Uninstall a Program option.

- Select and Remove all [email protected] related programs.
Remove [email protected] Related Registry Entries
- Press Windows+R buttons together to open Run Box

- Type “regedit” and click OK button.

- Select and remove all [email protected] related entries.
Remove [email protected] Infection From msconfig
- Open Run Box by pressing Windows+R buttons together.

- Now type “msconfig” in the Run Box and press Enter.

- Open Startup tab and uncheck all entries from unknown manufacturer.

Hope the above process has helped you in removing the [email protected] virus completely from your computer. If you still have this nasty ransomware left in your PC then you should opt for a malware removal tool. It is the most easy way to remove this harmful computer virus from your computer. Download the Free [email protected] Scanner on your system and scan your computer. It can easily find and remove this pesky ransomware threat from your PC.
If you have any questions regarding the removal of this virus then you can ask your question from your PC security experts. They will feel happy to solve your problem.