
Cerber 4.1.1 Ransomware – What's New?
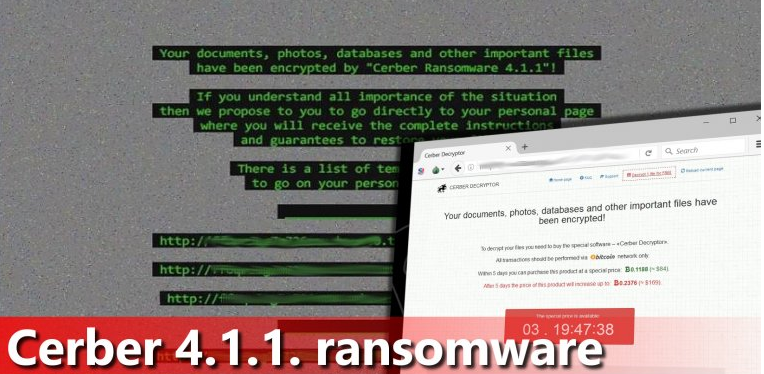
Creators of 'Cerber virus' family has recently unleashed Cerber 4.1.1 Ransomware right after the release of decryption tool of Cerber 4.1.0 by TrendMicro (a security researcher company). Seems like malicious creators are stubborn as much as security experts and AV vendors. This new variant of Cerber Virus set a customized wallpaper in order to help victims to find out that whether their PC has been compromised by v4.1.0 or v4.1.1. It does work absolutely smartly. Once it is activated, it starts looking for target files starting from system folders to external drive folder including mapped network drive. Distribution of the ransomware includes Spam emails, P2P Networks, Unsecured wireless network, USBs, Spamming websites etc.
Encryption process of Cerber 4.1.1 Ransomware
Afterwards, it combines RSA and AES ciphers to generate unique private key and public for the victim's PC and corrupt their files using Public key and then store private key (decryption key) on the hacker's extremely secured C&C server. You might ransom note on your desktop and inside each folders having corrupted files as well. So that, you might not notice nothing suspicious, however, the only thing that might raise your suspicion is a degraded PC’s performance during the encryption.
During encryption stage, this new variant generates and suffix certain file extension to encoded files – names of targeted files become marked with unique 4-digit symbols extension. For example, .dov9 or .j90t etc. Once Cerber 4.1.1 encodes targeted files, it finishes the malicious procedure by dropping ransom note named 'README.HTA' on your desktop. It also opens a .VBS file that plays an audio message informing about the infection, and then replaces the desktop wallpaper with following image:
Dealing with Cerber 4.1.1 Ransomware
Similar as previous variant of this Cerber ransomware, v4.1.1 asks to select language as well, then convince you complete a short “confirm-you-are-human” task and afterwards, this ransomware reveals information on “how to purchase a decryptor?”. During analysis we found an interesting fact that Cerber 4.1.1 demands a lower payment of ransom than its previous versions. It force you to pay 0.1188 BTC (84 USD) within 5 days of infection or the payment of ransom will be increased to 0.2376 Bitcoin (around $169) after the 5 days.
Therefore, security experts do not suggest to make any payment to the Ransomware Authors because there is no guarantee that after taking ransom they will give a working private key. Even worse, they might track down your financial account details like numbers, login details, credentials etc in order to hack your accounts. Hence, it is strongly recommended to remove Cerber 4.1.1 Ransomware and start restoring your files using the following instruction:
Free Scan your Windows PC to detect Cerber 4.1.1 Ransomware
Free Scan your Windows PC to detect Cerber 4.1.1 Ransomware
A: How To Remove Cerber 4.1.1 Ransomware From Your PC
Step: 1 How to Reboot Windows in Safe Mode with Networking.
- Click on Restart button to restart your computer
- Press and hold down the F8 key during the restart process.
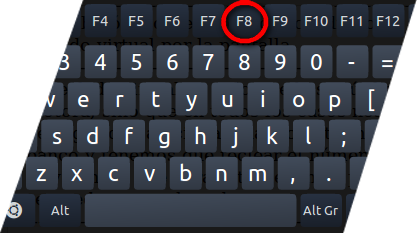
- From the boot menu, select Safe Mode with Networking using the arrow keys.
Step: 2 How to Kill Cerber 4.1.1 Ransomware Related Process From Task Manager
- Press Ctrl+Alt+Del together on your keyboard

- It will Open Task manager on Windows
- Go to Process tab, find the Cerber 4.1.1 Ransomware related Process.
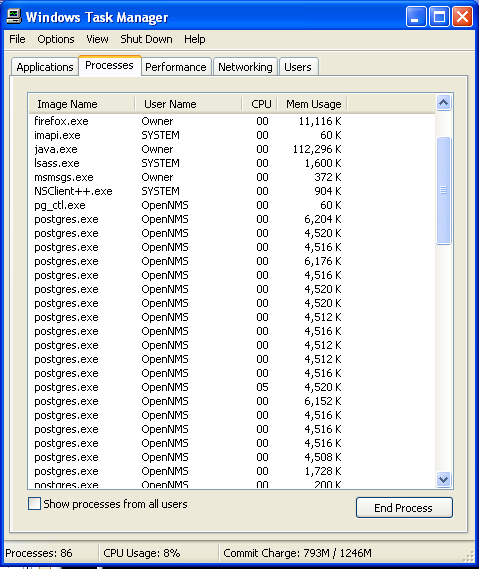
- Now click on on End Process button to close that task.
Step: 3 Uninstall Cerber 4.1.1 Ransomware From Windows Control Panel
- Visit the Start menu to open the Control Panel.
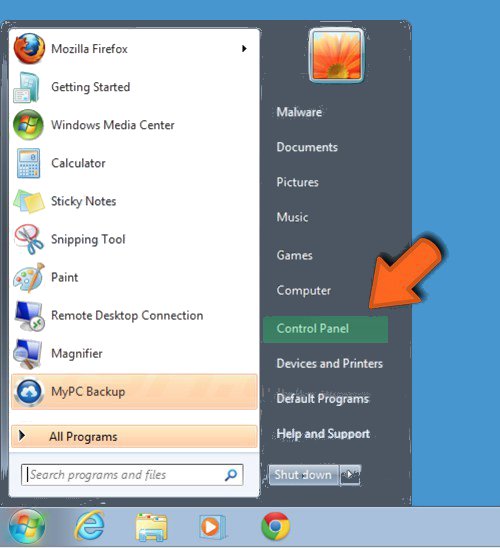
- Select Uninstall a Program option from Program category.
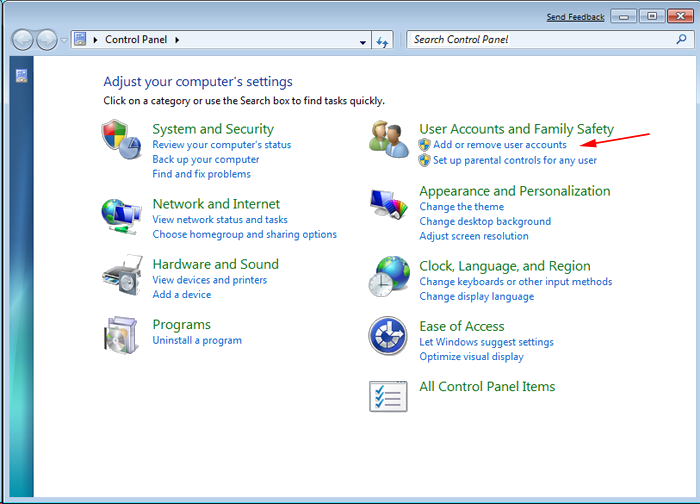
- Choose and remove all Cerber 4.1.1 Ransomware related items from list.

B: How to Restore Cerber 4.1.1 Ransomware Encrypted Files
Method: 1 By Using ShadowExplorer
After removing Cerber 4.1.1 Ransomware from PC, it is important that users should restore encrypted files. Since, ransomware encrypts almost all the stored files except the shadow copies, one should attempt to restore original files and folders using shadow copies. This is where ShadowExplorer can prove to be handy.
Download ShadowExplorer Now
- Once downloaded, install ShadowExplorer in your PC
- Double Click to open it and now select C: drive from left panel
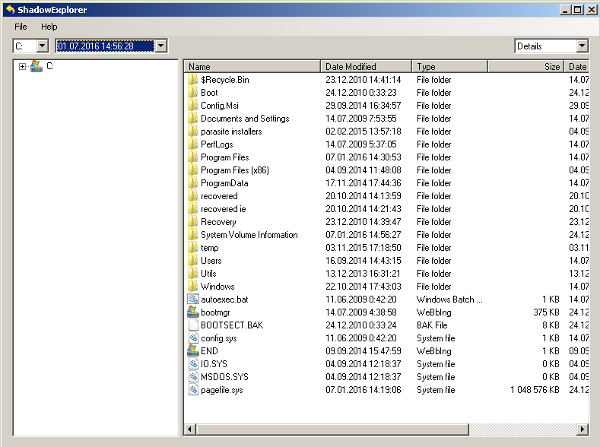
- In the date filed, users are recommended to select time frame of atleast a month ago
- Select and browse to the folder having encrypted data
- Right Click on the encrypted data and files
- Choose Export option and select a specific destination for restoring the original files
Method:2 Restore Windows PC to Default Factory Settings
Following the above mentioned steps will help in removing Cerber 4.1.1 Ransomware from PC. However, if still infection persists, users are advised to restore their Windows PC to its Default Factory Settings.
System Restore in Windows XP
- Log on to Windows as Administrator.
- Click Start > All Programs > Accessories.

- Find System Tools and click System Restore
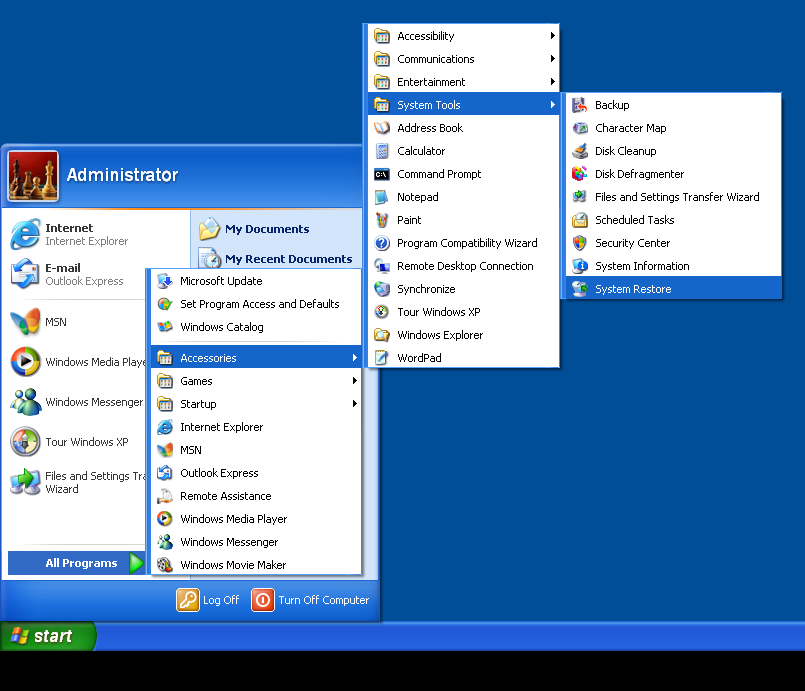
- Select Restore my computer to an earlier time and click Next.
- Choose a restore point when system was not infected and click Next.
System Restore Windows 7/Vista
- Go to Start menu and find Restore in the Search box.

- Now select the System Restore option from search results
- From the System Restore window, click the Next button.

- Now select a restore points when your PC was not infected.

- Click Next and follow the instructions.
System Restore Windows 8
- Go to the search box and type Control Panel

- Select Control Panel and open Recovery Option.

- Now Select Open System Restore option

- Find out any recent restore point when your PC was not infected.

- Click Next and follow the instructions.
System Restore Windows 10
- Right click the Start menu and select Control Panel.

- Open Control Panel and Find out the Recovery option.

- Select Recovery > Open System Restore > Next.

- Choose a restore point before infection Next > Finish.

Method:3 Using Data Recovery Software
Restore your files encrypted by Cerber 4.1.1 Ransomware with help of Data Recovery Software
We understand how important is data for you. Incase the encrypted data cannot be restored using the above methods, users are advised to restore and recover original data using data recovery software.



