August Stealer : Malware That Collects User Crucial Data
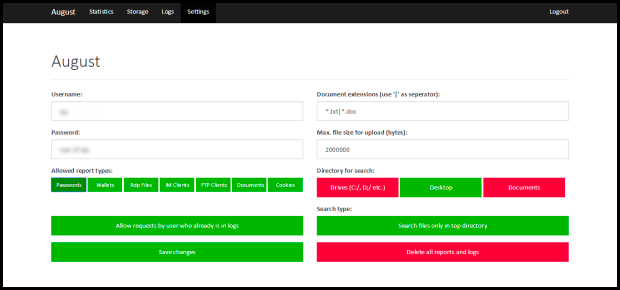
August Stealer is a piece of notorious malware belongs to the Trojan community. First of all it was offered for sale in October 2016 and reported for gathering users crucial data. According to the security analysts, it is too much specialized for obtaining data from the storage, protected passwords, email management applications, several FTP clients, Bitcoin wallets, IM clients, Remote desktop connection files and other file formats. Such a malware is promoted by its developer as a suite of tools that enable third-parties to gather wide range of users detail from the compromised Computers. Being created by Proof-point company researchers, it is another info-stealer malware that primarily leaked data. In short, August Stealer is primarily used for the reconnaissance purposes.
See How The Interface of August Stealer Looks Like
Know How August Stealer Is Spread
August Stealer is mainly associated with TA530 group of cyber hackers. These cyber hackers often employs the social engineering tactics by spreading phishing emails to user accounts so that users opened such a message and it automatically execute. The fake spam emails usually revolve around complaints topic that made by customers. When System users opened such a message, hackers dropped its payload. Therefore, it is strictly advised by victims that System users should not open any spam message. Besides spam campaigns, it also attacks Windows PC via so-called bundling method, torrent downloads, P2P file sharing site, contaminated devices, infected game servers and much more. Apart from these, it can be easily downloaded to PCs that are contaminated with other Trojan infections.
Malicious Activities That Performed By August Stealer
August Stealer often executed via hidden folder under AppData directory and inject the malicious code into legitimate procedure to hide itself deep inside the PC. According to the researchers, this malware is mainly known for recording cookies from web browsers and interfere with the online banking operations. It is mainly documented to extract users sensitive detail including login details of social media, email services, social security number, remote desktop accounts, notes, office documents and much more that saved on local disks. It extracts data from various classes of the software such as FTP clients, Web browsers, Email clients and much more. It often locks users incoming and outgoing network transmissions and makes it too much harder. In other words, August Stealer is very notorious and harmful for PC which doesn't only ruin user System experiences but also endangers their privacy. Therefore, the deletion of August Stealer is highly recommended from compromised machine.
>>Free Download August Stealer Scanner<<
Steps to Remove August Stealer
Step 1>> How to Boot Windows in Safe Mode to isolate August Stealer
Step 2>> How to View Hidden Files created by August Stealer
for Windows XP
- Exit all Program and Go to Desktop
- Select My Computer icon and Double Click to Open it
- Click on the Tools Menu and now select and Click on Folder Options.
- Select on View Tab that appears in New Window.
- Check mark on the box next to Dispaly the Contents of System Folders
- Now Check the box in order to Show Hidden Files and Folders
- Now press on Apply and OK to close the Window.
- As soon as these steps are performed, you can view the files and folders that were created by August Stealer and hidden till now.

for Windows Vista
- Minimize all Window and Go to Desktop
- Click on the Start Button which can be found in lower lef Corner having Windows Logo
- Click on the Control Panel on the Menu and Open it
- Control Panel can be opened in Classic View or Control Panel Home View.
- If you have Selected Classic View, follow this
- Double Click on the Folder icon to open it
- Now select the view tab
- Click on Option to Show Hidden Files or Folders
- If you have Selected Control Panel Home View, follow this
- Appearance and Personalization link is to be Clicked
- Select on Show Hidden Files or Folders
- Press Apply Option and then Click on OK.

This will Show all the Folders including those created by August Stealer
Know how to view Hidden Folders on Windows 7, Win 8 and Windows 10
(Following the above steps are necessary to view all the files created by August Stealer and that is known to exist on Compromised PC.)
- Open the Run Box by holding together the Start Key and R.

- Now Type and input appwiz.cpl and press on OK
- This will take you to the Control Panel, Now Search for Suspicious programs or any entries related to August Stealer. Unistall it once if you happen to find it. However be sure not to Uninstall any other program from the list.
- In the Search Field, Type msconfig and press on Enter, this will pop-up a Window

In the Startup Menu, Uncheck all the August Stealer related entries or which are Unknown as Manufacturer.
Step 3>> Open the Run Box by Pressing Start Key and R in Combination
- Copy + Paste the following Command as
- notepad %windir%/system32/Drivers/etc/hosts and press on OK
- This will Open a new file. If your system has been hacked by August Stealer, certain IP’s will be displayed which can be found in the bottom of the screen.
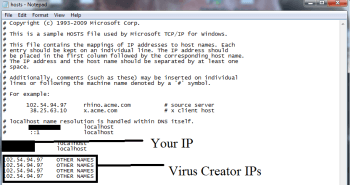
Look for the suspicious IP that is present in your Localhost
Step 4>> How to Terminate August Stealer Running Processes
- Go the Processes Tab by pressing on CTRL+SHIFT+ESC Keys Together.
- Look for the August Stealer Running Processes.
- Right Click on August Stealer and End the Process.

Step 5>> How to Remove August Stealer Related Registry Entries
- Open Registry by Typing Regedit in the Run box and Hit Enter Key
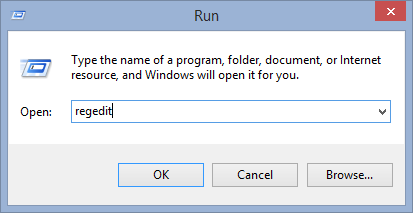
- This will open all the list of entries.
- Now Find and search the entries created by August Stealer and cautiously delete it.
- Alternatively, you can manually search for it in the list to delete August Stealer Manually.
Unfortunately, if you are unable to remove August Stealer, Scan your PC Now
Also submit question and let us know in case you are having some doubt. Our Experts will definitely respond with some positive suggestions for the same. Thanks!




