| Warning, many anti-virus scanner have detected CURATOR Ransomware as threat to your computer | ||
| CURATOR Ransomware is flagged by these Anti Virus Scanner | ||
| Anti Virus Software | Version | Detection |
| SentinelOne (Static ML) | 2018.5.4402 | General |
| Cyren | 5.2.459815 | Trj.Win64.CURATOR Ransomware.CC |
| AutoShun | 8.122222 | Variant of Win32/Trojan.CURATOR Ransomware.A |
| Webutation | 3.6.501 | MySuperSpy, MalWarrior 2007 |
| Suggestion: Uninstall CURATOR Ransomware Completely – Free Download | ||
CURATOR Ransomware may have entered your pc through these software. If you have not installed them , then get rid of them Audacity 2.1.0.0 , Youda Sushi Chef 2.0 , CDRViewer 1.2 , ProVideoPlayer 2.0.2 , PrintMe 1.0.1 , iStudiez Pro 1.3 , Retrospect Client 12.0.2.116 , Activity & Expense Tracker Plus 1.9.6 , PrefEdit 3.5 , TorChat 1.0.6 , GForce The Oddity v1.3.2 , Chococons 1.0 , Nebraska Huskers Football Schedule Widget 5.0 , iWapper 2.0 , YouView 0.5 , NetCloak TagBuilder 1.0 , Calculator 3.0 , BSClient/BattleshipServer 1.01 |
|
Introduction To CURATOR Ransomware
CURATOR Ransomware is a variant of its Ransomware family. It has affected several countries and infected many PCs till now. It introduces the multi language support and display the ransom note as HTA application Window. It’s main purpose is to lock your files for solving the wrong intention. It makes you victim.
How Does CURATOR Ransomware Enter Into The Computers
CURATOR Ransomware enters via spoofed email attachments, peer to per to peer file transfer network, social media, visiting low quality website, clicking on unknown link etc.
What Are The Encryption Method Which Is Used By CURATOR Ransomware
CURATOR Ransomware uses ciphers to lock your files. It changes the file name in this process by adding an extension. It is used as suffix at the end of every file name. Files which are generally encrypted by this ransomware are documents, spreadsheets, images, audio, video etc. The file formats which get encrypted by this ransomware are .jpg, .jpeg, .xls, .doc, .png, .txt, .ppt etc.
How Does CURATOR Ransomware Provide Hazardous Environment To Your Computer
CURATOR Ransomware drops a ransom note in the form of HTML or TXT. When you will try to open your file, you will get this ransom note on your desktop. It contains malicious message and demands a ransom amount. The ransom note can be found within the system. It is very problematic issue that you will become totally unable to open your files and need the decryption key. In such situation you will definitely pay the ransom amount which are demanded by the hackers. They will actually give the deadline to pay the amount. But paying this amount is not a solution because you are not going to get the decryption key to unlock the files. So, you should use the data recovery software to restore your data. You can also follow the instruction and guideline here to remove CURATOR Ransomware quickly from your computer.
Remove CURATOR Ransomware From Your PC
Step 1: Remove CURATOR Ransomware in Safe Mode with Command Prompt
- First of all disconnect your PC with network connection.
- Click restart button and keep pressing F8 key regularly while system restart.

- You will see “Windows Advanced Options Menu” on your computer screen.
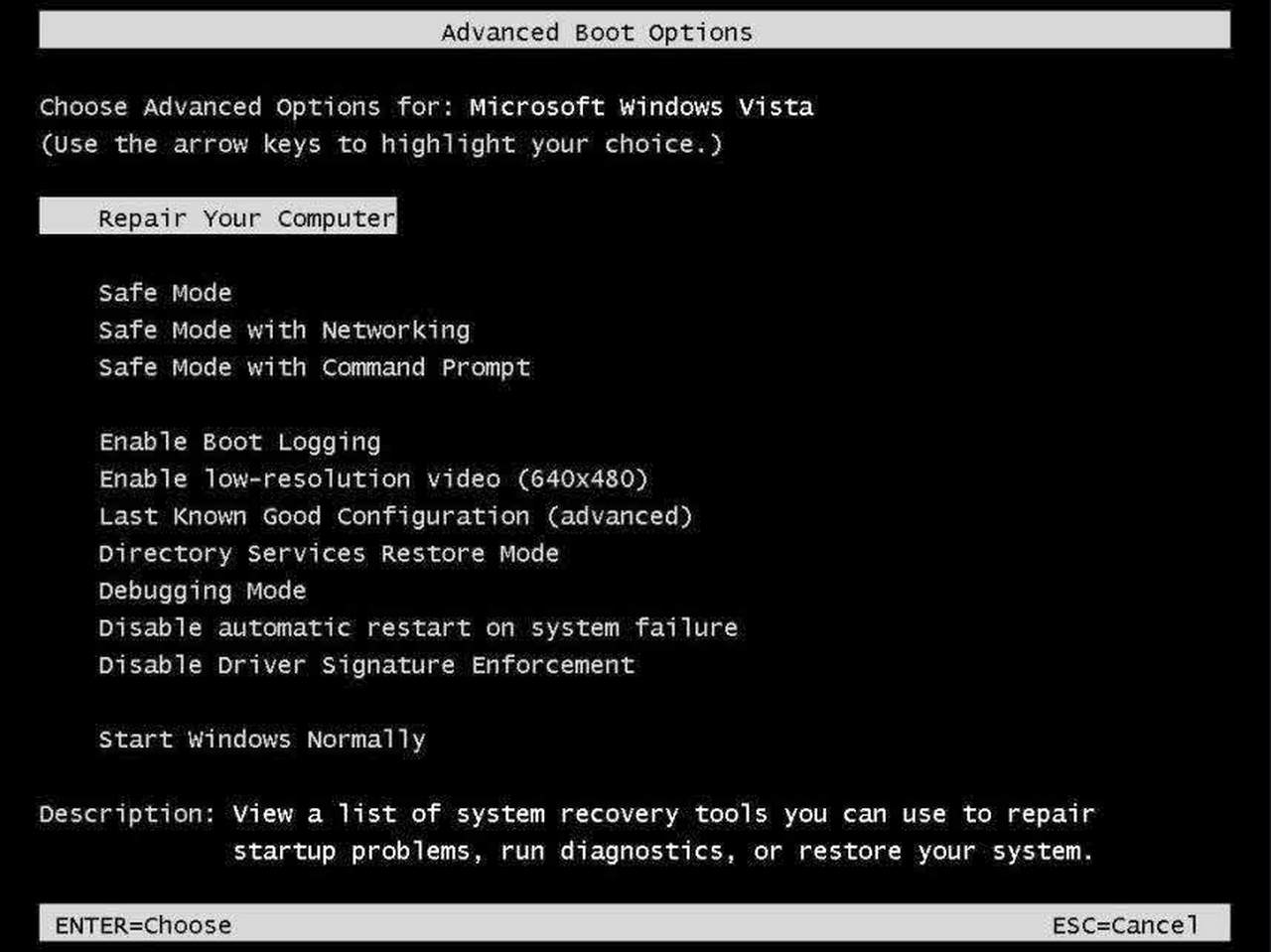
- Select “Safe Mode with Command Prompt” and press Enter key.
- You must login your computer with Administrator account for full privilege.

- Once the Command Prompt appears then type rstrui.exe and press Enter
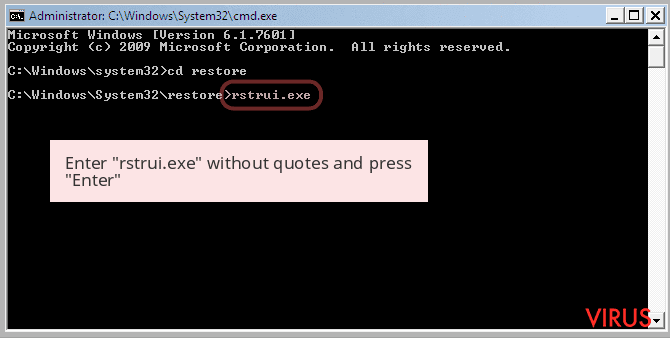
- Now follow the prompts on your screen to complete system restore.
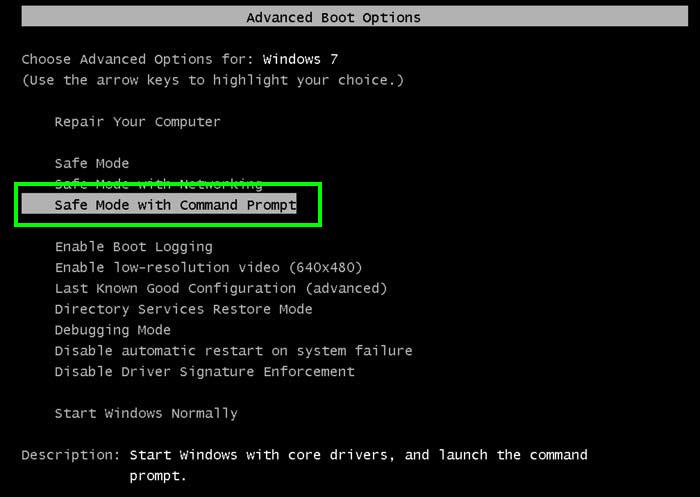
Step 2: Remove CURATOR Ransomware using MSConfig in Safe Mode:
- Power off your computer and restart again.
- While booting press the “F8 key” continuously to open “Windows Advanced Options Menu”.

- Use the arrow keys to select “Safe Mode” option and press Enter key.

- Once system get started go to Start menu. Type “msconfig” in the search box and launch the application.

- Go to the Startup tab and look for files from %AppData% or %Temp% folders using rundll32.exe. See an example below:
C:\Windows\System32\rundll32.exe C:\Users\username\appdata\local\temp\regepqzf.dll,H1N1
- Disable all the malicious entries and save the changes.
- Now restart your computer normally.
Step 3 : Kill Malicious Process Related To CURATOR Ransomware
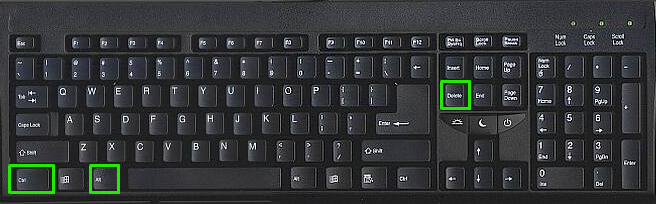
- Press Alt+Ctrl+Del buttons together.
- It will open the Task manager on your screen.
- Go to Process Tab and find CURATOR Ransomware related process.
- Click the End Process Now button to stop the running process.
Step 4 : Remove CURATOR Ransomware Virus From Registry Entry
- Press “Windows + R” key together to open Run Box.

- Type “regedit” and click OK button.

- Find and remove CURATOR Ransomware related entries.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnceEx
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunServices
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunServicesOnce
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Runonce
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunServices
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunServicesOnce
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run
Now hopefully you have completely removed the CURATOR Ransomware virus from your computer. If you are still get ransom message from the threat or unable to access your files, then it means that virus still remain into your computer. In such situation you don’t have any other option except removing this virus using any powerful malware removal tool.
Whereas if you have any backup of your infected or encrypted files, then you can also reinstall your Windows OS. This will erase all your files and data as along with the CURATOR Ransomware infection. You will get a completely empty computer system with no files. Now you can use your backup to get your files. If you don’t have any backup then using malware removal tool is a better option for you.
If you have any query or question regarding your computer, then you can easily ask your problem to our experts. Go to the Ask Any Question page and get the answer for your query directly from out experts.


