Can anyone help me to delete [email protected] Virus and decrypt files. My security application alerted with such a ransomware and I am too much worried as I know it is very risky for my PC. Although, I have tried several method to get rid of it but each time failure knock to me. Please help me anyone by providing an effective guide regarding deletion of [email protected] Virus.

Threat's Profile of [email protected] Virus
| Threat's Name | [email protected] Virus |
| Category | Crypto Malware, Ransomware, File Encrypting Virus |
| Danger Level | Very High |
| File Extension | [email protected] Virus |
| Affected Systems | Very High |
| Description | [email protected] Virus is another aggressive form of ransomware infection that locks user's stored files with strong AES-256 algorithm and asks victim to pay ransom fee. |
| Dispersal Channels | Spam messages, file sharing sources, infected devices, email attachments, torrent files, drive-by-downloads, exploit kits etc. |
| Symptoms |
|
| Removal | Possible, to delete [email protected] Virus download Windows scanner tool. |
Worthy Facts That You Must Know Related To [email protected] Virus
[email protected] Virus is another most devastating and notorious ransomware infection which is capable infect wide range of System executing on Windows based OS including Windows Server, Me, Vista, XP, 7, 8/8.1 and Windows 10. It often penetrates inside PC silently via spam campaigns, bundling method, torrent files, drive-by-downloads, exploit kits etc. Such a ransomware infection is mainly known for locking several types of files including audios or videos files, databases, documents, PDFs and many more. To lock files and makes them inaccessible, it uses combination of strong AES-256 and RSA-2048 algorithm. After locking files and makes them inaccessible, it prevents affected users from accessing their file. Upon the successful encryption procedure, the creators of [email protected] Virus generates a ransom note and displayed on desktop screen.
Ransom note contains all information about the file encryption and procedure through which users can easily decrypt their files. In ransom message, hackers instructs victims to pay ransom fee in exchange for file decryption. As we know that how files are crucial for individual, thus getting them back most of the users easily agreed to pay ransom demanded fee but it is not highly recommended. Team of security analysts are strictly advised victim to not pay ransom demanded fee under any circumstances because there is no any assurances that you will get the unique decryption key even paying ransom fee. Affected users can retrieve their files back using their backup copies but if you really want to keep your all crucial or valuable data safe for long time then you must delete [email protected] Virus immediately.
Free Scan your Windows PC to detect [email protected] Virus
Free Scan your Windows PC to detect [email protected] Virus
A: How To Remove [email protected] Virus From Your PC
Step: 1 How to Reboot Windows in Safe Mode with Networking.
- Click on Restart button to restart your computer
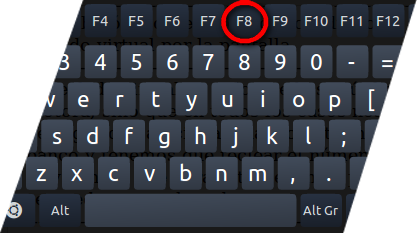
- Press and hold down the F8 key during the restart process.
- From the boot menu, select Safe Mode with Networking using the arrow keys.
Step: 2 How to Kill [email protected] Virus Related Process From Task Manager
- Press Ctrl+Alt+Del together on your keyboard

- It will Open Task manager on Windows
- Go to Process tab, find the [email protected] Virus related Process.
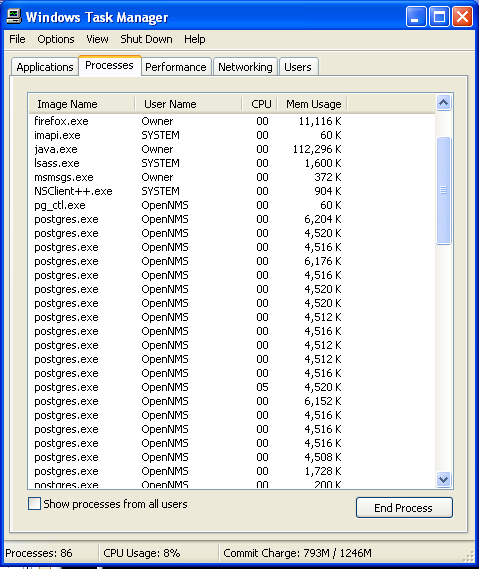
- Now click on on End Process button to close that task.
Step: 3 Uninstall [email protected] Virus From Windows Control Panel
- Visit the Start menu to open the Control Panel.
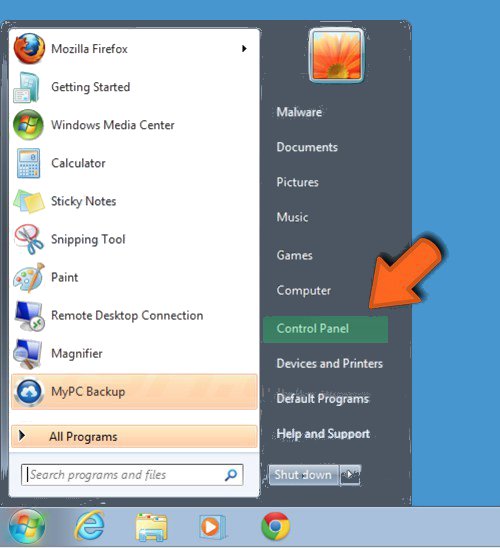
- Select Uninstall a Program option from Program category.
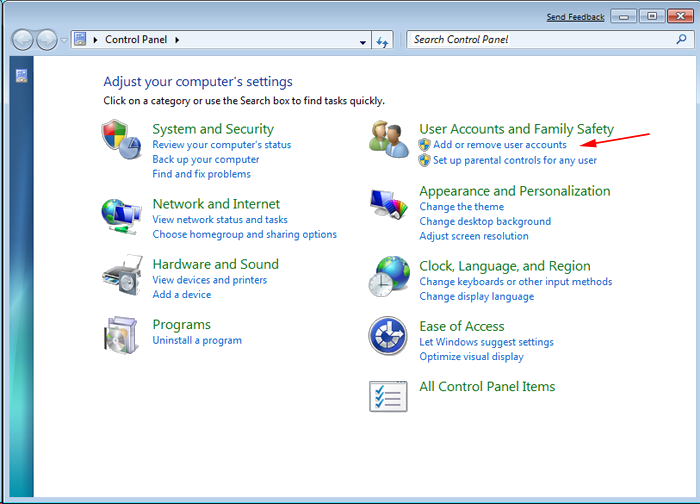
- Choose and remove all [email protected] Virus related items from list.

B: How to Restore [email protected] Virus Encrypted Files
Method: 1 By Using ShadowExplorer
After removing [email protected] Virus from PC, it is important that users should restore encrypted files. Since, ransomware encrypts almost all the stored files except the shadow copies, one should attempt to restore original files and folders using shadow copies. This is where ShadowExplorer can prove to be handy.
Download ShadowExplorer Now
- Once downloaded, install ShadowExplorer in your PC
- Double Click to open it and now select C: drive from left panel
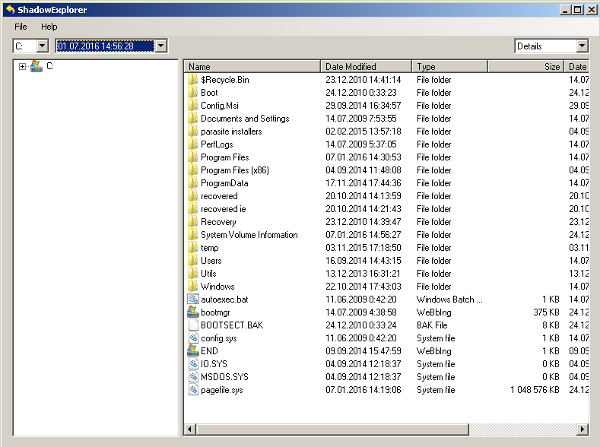
- In the date filed, users are recommended to select time frame of atleast a month ago
- Select and browse to the folder having encrypted data
- Right Click on the encrypted data and files
- Choose Export option and select a specific destination for restoring the original files
Method:2 Restore Windows PC to Default Factory Settings
Following the above mentioned steps will help in removing [email protected] Virus from PC. However, if still infection persists, users are advised to restore their Windows PC to its Default Factory Settings.
System Restore in Windows XP
- Log on to Windows as Administrator.
- Click Start > All Programs > Accessories.

- Find System Tools and click System Restore
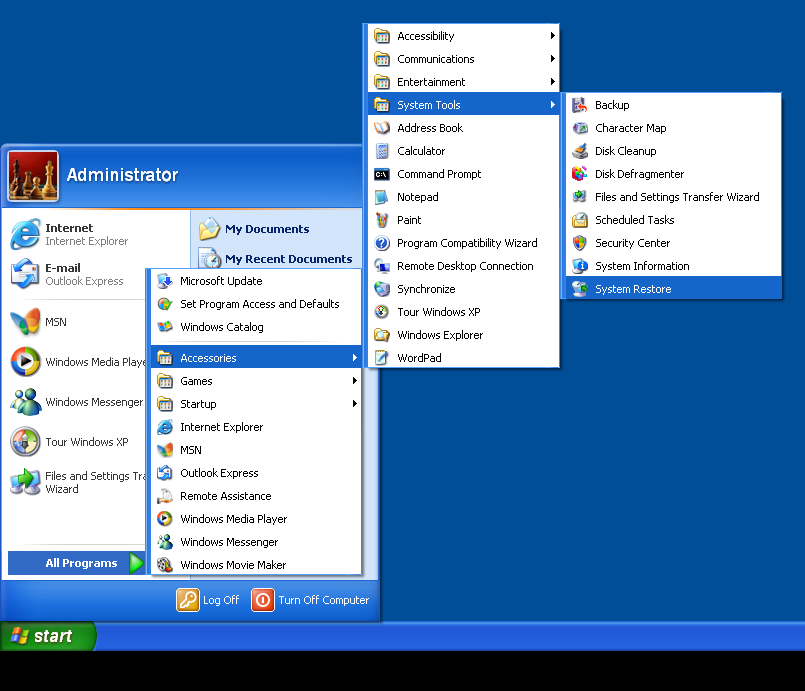
- Select Restore my computer to an earlier time and click Next.
- Choose a restore point when system was not infected and click Next.
System Restore Windows 7/Vista
- Go to Start menu and find Restore in the Search box.

- Now select the System Restore option from search results
- From the System Restore window, click the Next button.

- Now select a restore points when your PC was not infected.

- Click Next and follow the instructions.
System Restore Windows 8
- Go to the search box and type Control Panel

- Select Control Panel and open Recovery Option.

- Now Select Open System Restore option

- Find out any recent restore point when your PC was not infected.

- Click Next and follow the instructions.
System Restore Windows 10
- Right click the Start menu and select Control Panel.

- Open Control Panel and Find out the Recovery option.

- Select Recovery > Open System Restore > Next.

- Choose a restore point before infection Next > Finish.

Method:3 Using Data Recovery Software
Restore your files encrypted by [email protected] Virus with help of Data Recovery Software
We understand how important is data for you. Incase the encrypted data cannot be restored using the above methods, users are advised to restore and recover original data using data recovery software.



