Threat Analysis For: Shrug Ransomware
| Name | Shrug Ransomware |
| Category | Ransomware |
| Extension | .SHRUG |
| Ransom Amount | 50 USD |
| Encryption | AES algorithm |
| Detection | Free Download Shrug Ransomware Scanner |
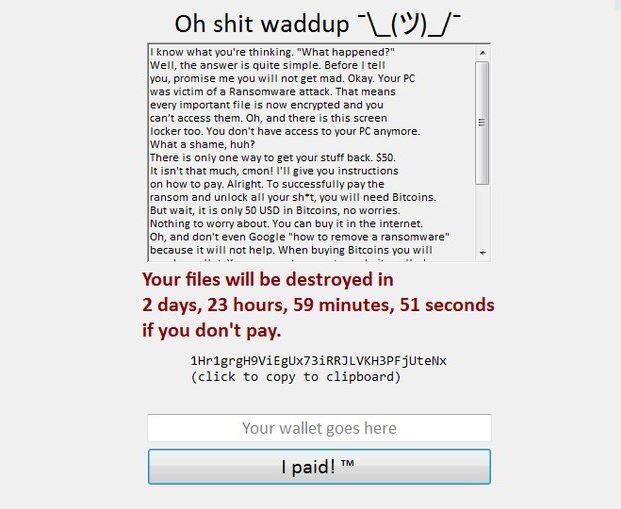
Shrug Ransomware can be deeply distressing for users as it can encrypt crucial files in the system and leave them unusable. It has been recently discovered by security researchers and is assumed to be in test phase. Researchers believe that the ransomware is capable of updating its module in its future versions and hence can be capable of doing even more damage. Shrug Ransomware is unique, as its scripts have not been found to be related to other ransomware families. Researchers have not been able to identify the threat actors behind the ransomware. Though the ransom window does display the name 'Martha' as undersigned, it remains irrelevant with regards to identity.
Shrug Ransomware has been found to be using spam messages as the prime mode to spread itself. It uses legitimate subject details to catch users attention and the contents within are associated with reputed brands and firms. The attachments may contain infected payloads in form of macros embedded within the document or it can be bundled-up with software setup packages. It can even be obtained from malware such as browser hijacker which may already have infected the system.
Shrug Ransomware soon after installing itself in the system carries out an extensive scan to find about the system it look for details like operating system, location, name and address of user that can be used to modify system settings such as Windows Registry entries. It can disable important functions of anti-virus applications such as changing firewall settings that can allow it to protect itself and remain for long period. The ransomware even intimidates users that their system will become useless if ransom is not paid within three days. It can make changes that can enable it to restart itself every time the system reboots. In order to make the encrypted file irretrievable, Shrug Ransomware can delete Shadow Volume Copies and System Restore Data. To counter this a user will require an advanced retrieval software, which can be referred below.
Shrug Ransomware is capable in encrypting files of multiple types such as images, videos, audio, documents, database, archives and backups. As soon as it encrypts these files, it uses '.SHRUG' as an extension to all original file names. Users will be able to notice that the file names have changed and they will show a white background icon which typically implies that they are unusable. The ransom message from Shrug Ransomware gets displayed in 'Shrug.exe' file that executes itself soon after encrypting the files. It mentions an amount of 50USD to be paid, however users can avoid that by following the removal guide below.
Free Scan your Windows PC to detect Shrug Ransomware
Free Scan your Windows PC to detect Shrug Ransomware
A: How To Remove Shrug Ransomware From Your PC
Step: 1 How to Reboot Windows in Safe Mode with Networking.
- Click on Restart button to restart your computer
- Press and hold down the F8 key during the restart process.
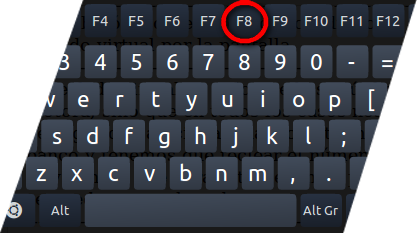
- From the boot menu, select Safe Mode with Networking using the arrow keys.
Step: 2 How to Kill Shrug Ransomware Related Process From Task Manager
- Press Ctrl+Alt+Del together on your keyboard

- It will Open Task manager on Windows
- Go to Process tab, find the Shrug Ransomware related Process.
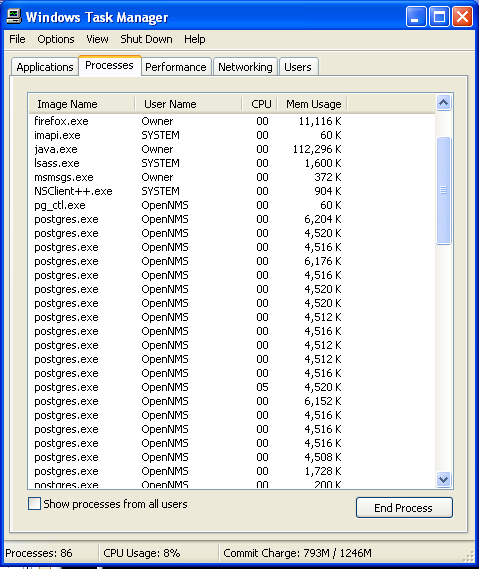
- Now click on on End Process button to close that task.
Step: 3 Uninstall Shrug Ransomware From Windows Control Panel
- Visit the Start menu to open the Control Panel.
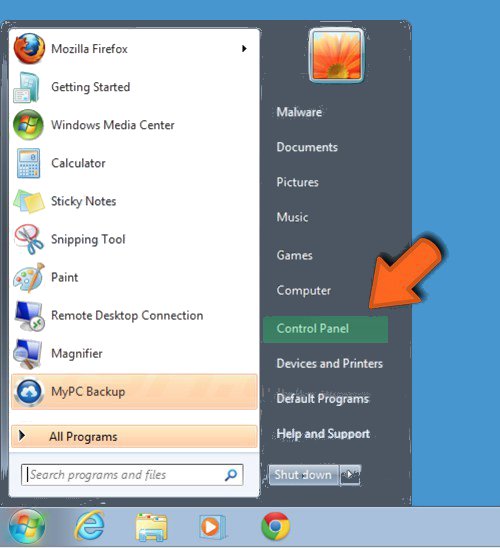
- Select Uninstall a Program option from Program category.
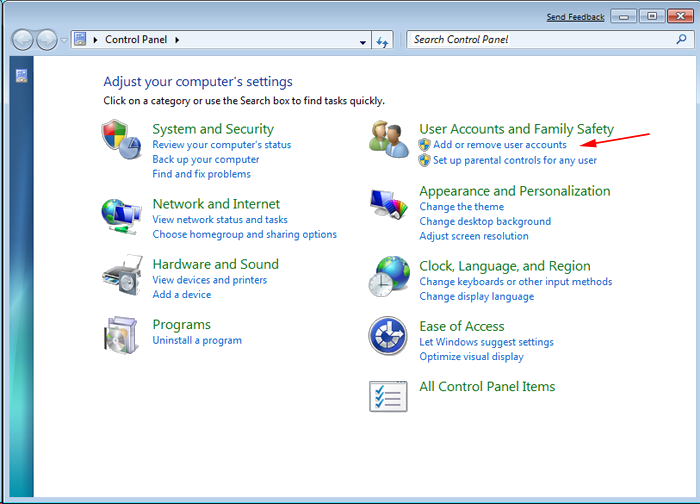
- Choose and remove all Shrug Ransomware related items from list.

B: How to Restore Shrug Ransomware Encrypted Files
Method: 1 By Using ShadowExplorer
After removing Shrug Ransomware from PC, it is important that users should restore encrypted files. Since, ransomware encrypts almost all the stored files except the shadow copies, one should attempt to restore original files and folders using shadow copies. This is where ShadowExplorer can prove to be handy.
Download ShadowExplorer Now
- Once downloaded, install ShadowExplorer in your PC
- Double Click to open it and now select C: drive from left panel
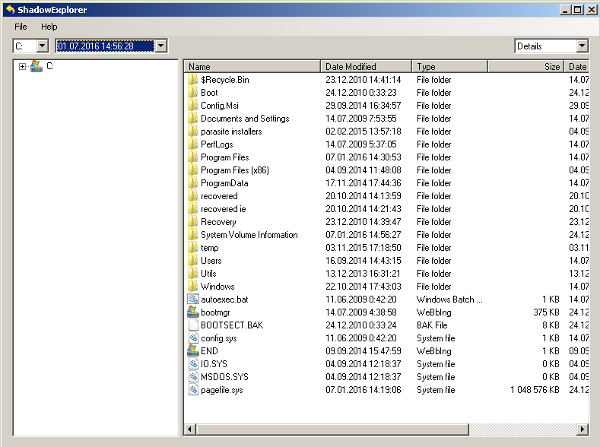
- In the date filed, users are recommended to select time frame of atleast a month ago
- Select and browse to the folder having encrypted data
- Right Click on the encrypted data and files
- Choose Export option and select a specific destination for restoring the original files
Method:2 Restore Windows PC to Default Factory Settings
Following the above mentioned steps will help in removing Shrug Ransomware from PC. However, if still infection persists, users are advised to restore their Windows PC to its Default Factory Settings.
System Restore in Windows XP
- Log on to Windows as Administrator.
- Click Start > All Programs > Accessories.

- Find System Tools and click System Restore
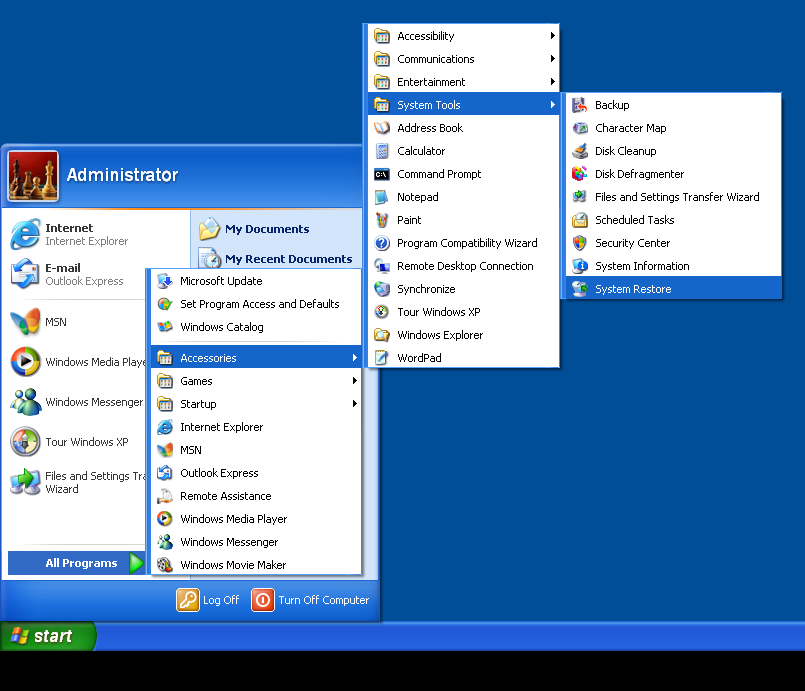
- Select Restore my computer to an earlier time and click Next.
- Choose a restore point when system was not infected and click Next.
System Restore Windows 7/Vista
- Go to Start menu and find Restore in the Search box.

- Now select the System Restore option from search results
- From the System Restore window, click the Next button.

- Now select a restore points when your PC was not infected.

- Click Next and follow the instructions.
System Restore Windows 8
- Go to the search box and type Control Panel

- Select Control Panel and open Recovery Option.

- Now Select Open System Restore option

- Find out any recent restore point when your PC was not infected.

- Click Next and follow the instructions.
System Restore Windows 10
- Right click the Start menu and select Control Panel.

- Open Control Panel and Find out the Recovery option.

- Select Recovery > Open System Restore > Next.

- Choose a restore point before infection Next > Finish.

Method:3 Using Data Recovery Software
Restore your files encrypted by Shrug Ransomware with help of Data Recovery Software
We understand how important is data for you. Incase the encrypted data cannot be restored using the above methods, users are advised to restore and recover original data using data recovery software.



