| Warning, many anti-virus scanner have detected H@RM@ Ransomware as threat to your computer | ||
| H@RM@ Ransomware is flagged by these Anti Virus Scanner | ||
| Anti Virus Software | Version | Detection |
| nProtect | 2018.4.5814 | Common |
| F-Prot | 4.3.234443 | Trj.Win32.H@RM@ Ransomware.CA |
| CAT-QuickHeal | 1.303154 | Variant of Win32/Trojan.H@RM@ Ransomware.C |
| VX Vault | 7.0.427 | Windows Custom Settings, Spyware.SafeSurfing |
| Suggestion: Uninstall H@RM@ Ransomware Completely – Free Download | ||
H@RM@ Ransomware may have entered your pc through these software. If you have not installed them , then get rid of them iSnip 1.4 , Doc 2.0.1 , Bark 1.1 , Wondershare MobileGo for Android Pro , Water FX Screen Saver 1.0 , Circus Acts 1.0 , Emagic SoundDiver Updater 3.0.4 , Pocket MBA: Learning Studio 1.0 , Aiseesoft iPod touch Video Converter , SlidePad 1.2.5 , Sight Words 1.1 , JobOrder 2012.5 |
|

Complete Information Of H@RM@ Ransomware
H@RM@ Ransomware is a latest variant of its previous Ransomware that come out recently. First of all team of security analysts discovered it and seems that it is primarily targeted to its domestic users but it doesn’t mean that it cannot affect other language speaking System users. According to the researchers, it attached a suffix to the end of the targeted filenames and delete the Shadow Volume snapshots of original files. It is created by its con artists in such a way that it can compromise System executing on Windows based Operating System and target almost all file types including audio or video files, documents, presentations, PDFs, images, spreadsheets and many more.
Upon performing the successful file encryption procedure, it displays a ransom note in HTA application window that informs victims about the encryption procedure of H@RM@ Ransomware and instructs victims to pay USD in BTC. Once getting ransom note, most of the System users easily decided to pay ransom demanded fee but team of security analysts are not recommended to do because like predecessor variant, it also doesn’t deliver guarantee to decrypt files even paying large sum of ransom demanded fee. Therefore, it is highly advised affected users to get rid of H@RM@ Ransomware.
Distribution Channels Of H@RM@ Ransomware
- Spam campaigns including dubious attachments and malicious link.
- Shareware or freeware downloads including additional component.
- Infected peripheral devices used to transfer or share data.
- Infected or malicious site including several third-party or suspicious ads.
- P2P file sharing network, drive-by-downloads, fake software installers etc.
Free Scan your Windows PC to detect H@RM@ Ransomware
A: How To Remove H@RM@ Ransomware From Your PC
Step: 1 How to Reboot Windows in Safe Mode with Networking.
- Click on Restart button to restart your computer
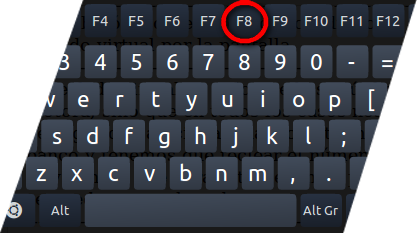
- Press and hold down the F8 key during the restart process.
- From the boot menu, select Safe Mode with Networking using the arrow keys.
Step: 2 How to Kill H@RM@ Ransomware Related Process From Task Manager
- Press Ctrl+Alt+Del together on your keyboard

- It will Open Task manager on Windows
- Go to Process tab, find the H@RM@ Ransomware related Process.
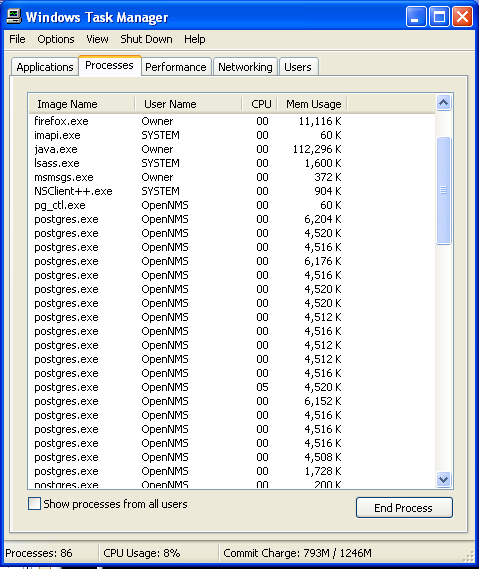
- Now click on on End Process button to close that task.
Step: 3 Uninstall H@RM@ Ransomware From Windows Control Panel
- Visit the Start menu to open the Control Panel.
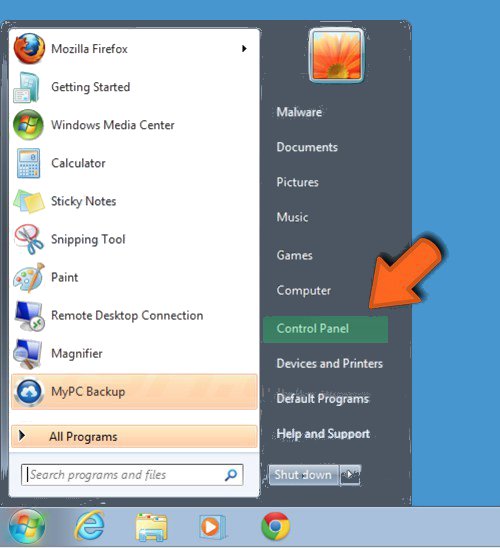
- Select Uninstall a Program option from Program category.
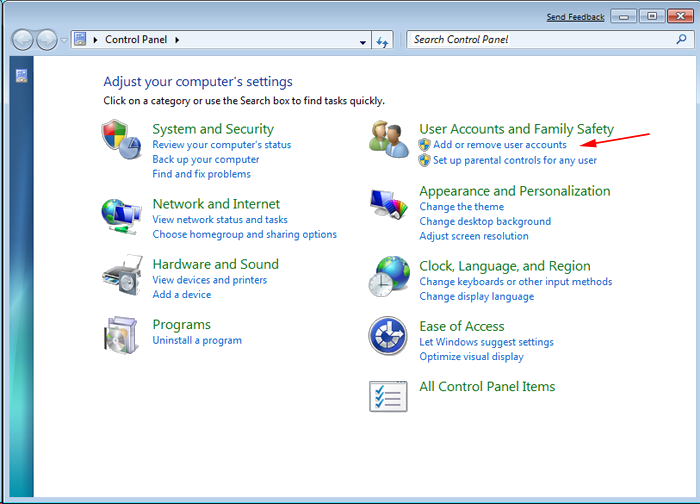
- Choose and remove all H@RM@ Ransomware related items from list.

B: How to Restore H@RM@ Ransomware Encrypted Files
Method: 1 By Using ShadowExplorer
After removing H@RM@ Ransomware from PC, it is important that users should restore encrypted files. Since, ransomware encrypts almost all the stored files except the shadow copies, one should attempt to restore original files and folders using shadow copies. This is where ShadowExplorer can prove to be handy.
Download ShadowExplorer Now
- Once downloaded, install ShadowExplorer in your PC
- Double Click to open it and now select C: drive from left panel
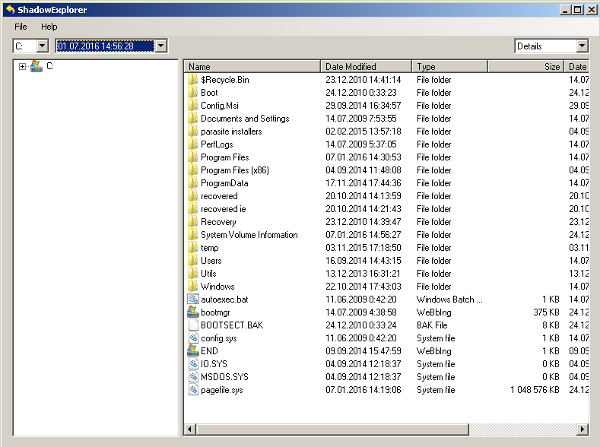
- In the date filed, users are recommended to select time frame of atleast a month ago
- Select and browse to the folder having encrypted data
- Right Click on the encrypted data and files
- Choose Export option and select a specific destination for restoring the original files
Method:2 Restore Windows PC to Default Factory Settings
Following the above mentioned steps will help in removing H@RM@ Ransomware from PC. However, if still infection persists, users are advised to restore their Windows PC to its Default Factory Settings.
System Restore in Windows XP
- Log on to Windows as Administrator.
- Click Start > All Programs > Accessories.

- Find System Tools and click System Restore
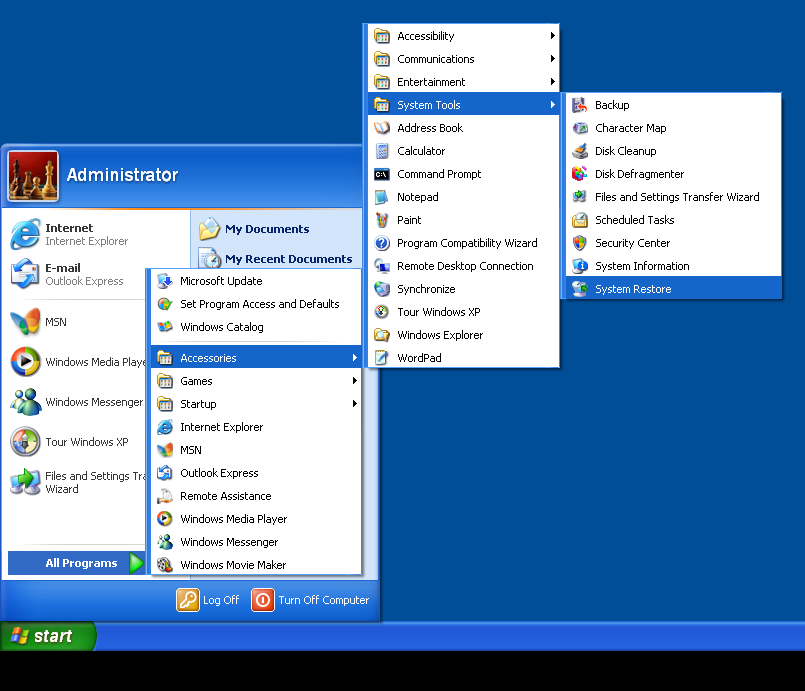
- Select Restore my computer to an earlier time and click Next.
- Choose a restore point when system was not infected and click Next.
System Restore Windows 7/Vista
- Go to Start menu and find Restore in the Search box.

- Now select the System Restore option from search results
- From the System Restore window, click the Next button.

- Now select a restore points when your PC was not infected.

- Click Next and follow the instructions.
System Restore Windows 8
- Go to the search box and type Control Panel

- Select Control Panel and open Recovery Option.

- Now Select Open System Restore option

- Find out any recent restore point when your PC was not infected.

- Click Next and follow the instructions.
System Restore Windows 10
- Right click the Start menu and select Control Panel.

- Open Control Panel and Find out the Recovery option.

- Select Recovery > Open System Restore > Next.

- Choose a restore point before infection Next > Finish.

Method:3 Using Data Recovery Software
Restore your files encrypted by H@RM@ Ransomware with help of Data Recovery Software
We understand how important is data for you. Incase the encrypted data cannot be restored using the above methods, users are advised to restore and recover original data using data recovery software.

