Research Report on LockeR Ransomware
LockeR Ransomware is a newly detected file-encrypting virus which infiltrates the targeted Windows machine with the help of compromised remote desktop accounts, rogue or freeware programs, malicious payload attached to spam emails and the cracked copies of various shareware. Based on the recent research report, the security investigators of RMV have found that the malware is still under development phase. Besides, the criminal hackers responsible for this vicious attack are suspected of targeting the mid and small-sized businesses. Server admins that are working on the WordPress platform should also expect the attack of LockeR Ransomware. Therefore, it is strongly recommended to maintain reliable backup of their valuable data and default settings. In order to maintain its structure and the functionality, the malware uses encoded connections and the channels over the TOR network.
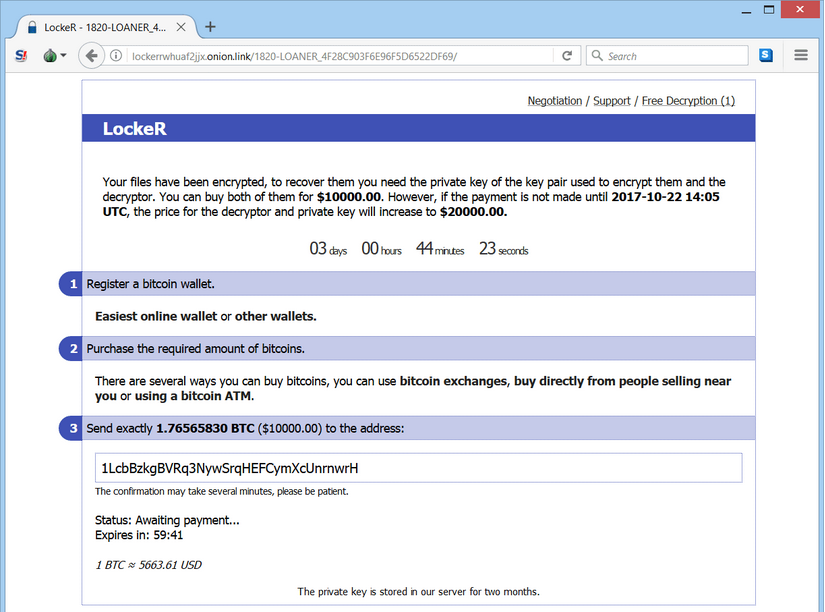
Meanwhile, this ransomware is known to demand 10,000 to 20,000 USD from the affected companies in the form of bitcoin. LockeR Ransomware is also known to encrypt multimedia content, MS Office documents, and important project files. After encoding the targeted file system, the malware is reported to deploy a ransom notification named [How_To_Decrypt_Files].txt in a simple text file which is dropped onto the computer's desktop. The team of cyber criminals behind this ransomware is reported to operate hxxp://i56bvhjey5gzakmd.onion and hxxp://lockerrwhuaf2jjx.onion over the TOR network. However, there web domains are not likely to be the only ones that are managed by the developers of this dangerous file-encoder virus. Previously reported file-encrypting threat, such as Cerber 6 ransomware uses dozens of web pages in order to process the ransom payments from the victimized machine users.
How To Deal with LockeR Ransomware Virus?
Cyber security analysts alert that the ransomware is specifically programmed by the team of criminal hackers in order to support an offline encryption of the targeted system files and it does not rely on the constant client-server communication to be the most hazardous and effective infection. Based on the research report, the LockeR Ransomware is identified to drop a file named as '.KEY' onto every contaminated machines and the affected system users are instructed to deliver the '.KEY' file to the virus operators if they are interested to pay the asked ransom money to get their PC files back in normal stage. However, the researchers advised computer users to refrain paying ransom money and use a credible anti-malware shield for its complete removal.
Free Scan your Windows PC to detect LockeR Ransomware
Free Scan your Windows PC to detect LockeR Ransomware
A: How To Remove LockeR Ransomware From Your PC
Step: 1 How to Reboot Windows in Safe Mode with Networking.
- Click on Restart button to restart your computer
- Press and hold down the F8 key during the restart process.
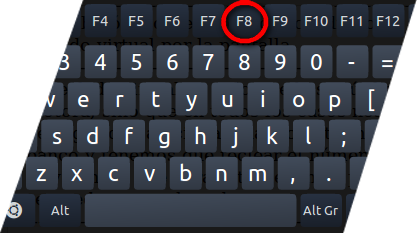
- From the boot menu, select Safe Mode with Networking using the arrow keys.
Step: 2 How to Kill LockeR Ransomware Related Process From Task Manager
- Press Ctrl+Alt+Del together on your keyboard

- It will Open Task manager on Windows
- Go to Process tab, find the LockeR Ransomware related Process.
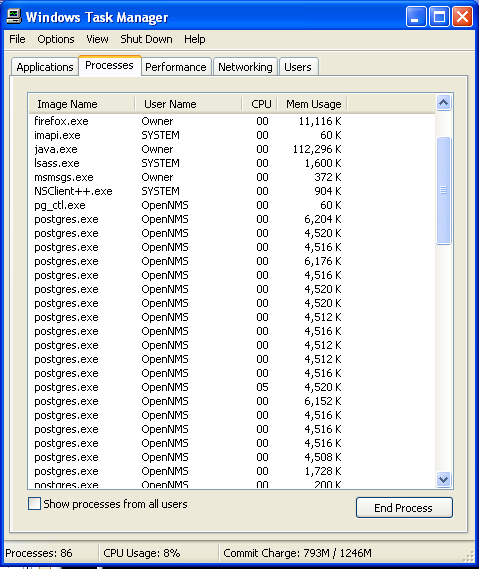
- Now click on on End Process button to close that task.
Step: 3 Uninstall LockeR Ransomware From Windows Control Panel
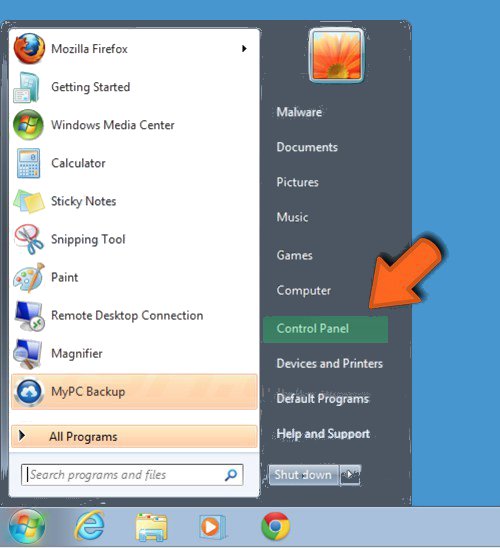
- Visit the Start menu to open the Control Panel.
- Select Uninstall a Program option from Program category.
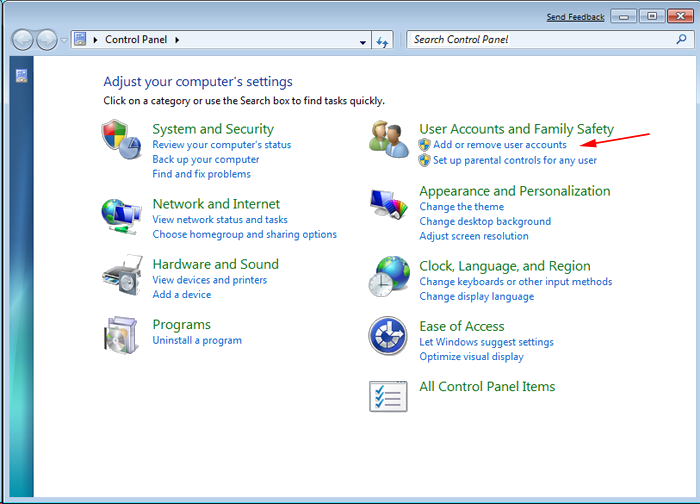
- Choose and remove all LockeR Ransomware related items from list.

B: How to Restore LockeR Ransomware Encrypted Files
Method: 1 By Using ShadowExplorer
After removing LockeR Ransomware from PC, it is important that users should restore encrypted files. Since, ransomware encrypts almost all the stored files except the shadow copies, one should attempt to restore original files and folders using shadow copies. This is where ShadowExplorer can prove to be handy.
Download ShadowExplorer Now
- Once downloaded, install ShadowExplorer in your PC
- Double Click to open it and now select C: drive from left panel
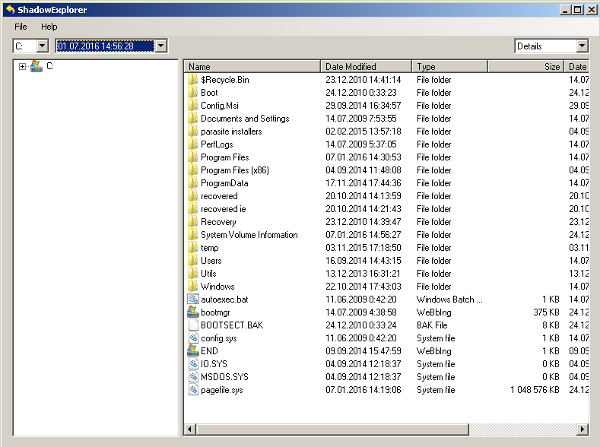
- In the date filed, users are recommended to select time frame of atleast a month ago
- Select and browse to the folder having encrypted data
- Right Click on the encrypted data and files
- Choose Export option and select a specific destination for restoring the original files
Method:2 Restore Windows PC to Default Factory Settings
Following the above mentioned steps will help in removing LockeR Ransomware from PC. However, if still infection persists, users are advised to restore their Windows PC to its Default Factory Settings.
System Restore in Windows XP
- Log on to Windows as Administrator.
- Click Start > All Programs > Accessories.

- Find System Tools and click System Restore
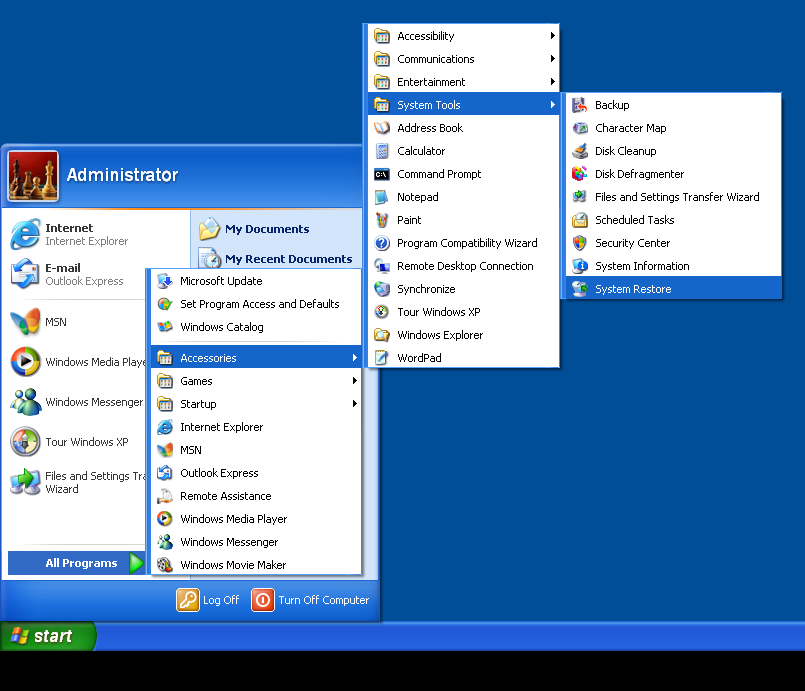
- Select Restore my computer to an earlier time and click Next.
- Choose a restore point when system was not infected and click Next.
System Restore Windows 7/Vista
- Go to Start menu and find Restore in the Search box.

- Now select the System Restore option from search results
- From the System Restore window, click the Next button.

- Now select a restore points when your PC was not infected.

- Click Next and follow the instructions.
System Restore Windows 8
- Go to the search box and type Control Panel

- Select Control Panel and open Recovery Option.

- Now Select Open System Restore option

- Find out any recent restore point when your PC was not infected.

- Click Next and follow the instructions.
System Restore Windows 10
- Right click the Start menu and select Control Panel.

- Open Control Panel and Find out the Recovery option.

- Select Recovery > Open System Restore > Next.

- Choose a restore point before infection Next > Finish.

Method:3 Using Data Recovery Software
Restore your files encrypted by LockeR Ransomware with help of Data Recovery Software
We understand how important is data for you. Incase the encrypted data cannot be restored using the above methods, users are advised to restore and recover original data using data recovery software.



