Get More Knowledge on RotorCrypt Ransomware
RotorCrypt Ransomware is a new name of previously known Rotor Cryptovirus. The threat is also a ransomware virus as its past iteration. After it encrypts your files, the extension .c400 will be added to them along with the one of two email addresses. These email ID are [email protected] and [email protected]. Moreover, the ransomware threat could be delivered to your system by using different tactics. Its payload file could be distributed with along with junk email attachments, just because its full contents can not be conveyed in email body. If you open those files, your PC become easily infected. The attached file can be heavily obfuscated and in most cases it is an executable file.
Brief Description on RotorCrypt Ransomware
This ransomware threat is discovered to be a new variant of Rotor Virus (Cocoslim98). The malware uses new executable in order to spread its harmful files. In the Payload Security website, the detection of one such malicious executable file is identified as GWWABPFL.exe. Although, when the payload file of RotorCrypt Ransomware virus is executed on the system, it spawns plenty of malicious processes, according to the security analysts of Payload Security. The threat is still mainly orientated around the targeting servers and many Windows system has been infected as well.

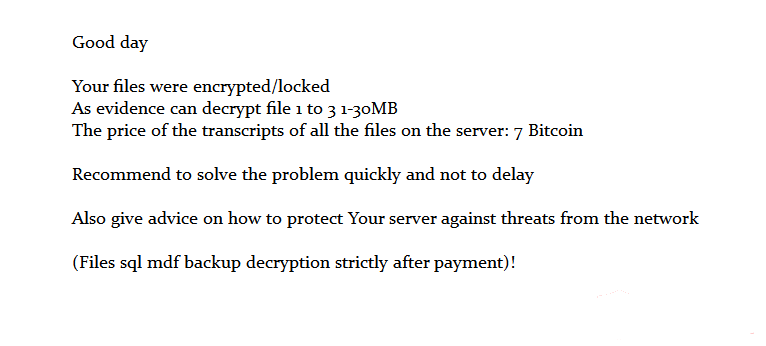
After gets activated on your PC, this ransomware could set up the values in Windows registry, whereupon the malware gains persistence. The values are set inside the entries of that registry which make the RotorCrypt Ransomware launch automatically with each and every boot of Windows operating system. When the system files gets encrypted, a tiny ransom ransom message with the payment instructions will be created. Furthermore, the ransomware doesn’t give you any specific deadline for paying ransom money to the cyber hackers for the file decryption process.
Besides, the malware also makes an offer of free decryption for a couple of system files as a testing procedure. Its demands are high with ransom money which is demanded and the decryption of few files will be only available after the payment. The ransom fee which is asked by RotorCrypt Ransomware is 7 Bitcoins which is equal to 4928.56 USD at the time of writing this article. However, you should not think of paying these hackers, because no one can guarantee that you will get your vital files back to what they were after payment. Additionally, you should try to decrypt your files by using the test decryption service which is provided below in this post or wait to see if there is a decryption key available.
Free Scan your Windows PC to detect RotorCrypt Ransomware
What To Do If Your PC Get Infected By RotorCrypt Ransomware
The ransomware infection has been mainly designed with the purpose to scare users and trick their money. It take your files on hostage and demand ransom to return your important data. But now the question is what you can do when your system got infected by RotorCrypt Ransomware virus? Here are some option that you can use to get rid of this nasty infection.
Don’t Panic – Well the first thing is Don’t panic and then completely check out your system for any working files. If you got any working files then copy it to USB drive.
Pay Ransom – Other option is you can pay the ransom and wait to get your files back. (really a bad option)
Use Backup – Clean you entire system files, remove the infection completely from your PC and restore your files with any backup.
Remove Infection – You can also delete RotorCrypt Ransomware virus using malware removal tool and remove all the infected files. You can later recover all your data by using any data recovery tool. (In case you don’t have backup of your files.) – Recommended Method.
Reinstall Windows – The last option is reinstall your Windows OS. It will completely remove all your data as well as infection. You will get a completely new infection free PC.
How To Remove RotorCrypt Ransomware Virus From Your PC
Step 1 – Boot your computer in Safe mode.
Step 2 – Remove the infected registry entry files.
- Click Windows Flag and R button together.

- Type “regedit” and click OK button

- Find and delete following entries.
HKEY_LOCAL_MACHINESOFTWAREsupWPM
HKEY_LOCAL_MACHINESYSTEMCurrentControlSetServicesWpm
HKEY_CURRENT_USERSoftwareMicrosoftInternet ExplorerMain “Default_Page_URL”
HKEY_LOCAL_Machine\Software\Classes\[RotorCrypt Ransomware]
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\[RotorCrypt Ransomware]
Step-By-Step Video Removal Guide To Decrypt RotorCrypt Ransomware
Step 3 – Remove From msconfig
- Click Windows + R buttons simultaneously.

- Type msconfig and press Enter

- Go to Startup tab and uncheck all entries from unknown manufacturer.

Step 4 – Restart your computer normally.
Check your computer now. If the virus has gone then you can start using your computer. If the infection still remains then head to the next step.
Step 5 – System Restore
- Insert Windows installation disk to CD drive and restart your PC.
- While system startup, keep pressing F8 or F12 key to get boot options.
- Now select the boot from CD drive option to start your computer.
- Then after you will get the System Recovery Option on your screen.
- Select the System Restore option from the list.
- Choose a nearest system restore point when your PC was not infected.
- Now follow the option on your screen to Restore your computer.
If the above manual methods didn’t removed RotorCrypt Ransomware virus then you have only option to remove infection using a malware removal tool. It is last and the only option that can easily and safely remove this nasty threat from your computer.
Having some alarming questions in your mind? Get your doubt cleared from our experienced tech support experts. Just go to the Ask Your Question section, fill in the details and your question. Our expert team will give you detailed reply about your query.




