Get More Knowledge on CommandLine Ransomware
CommandLine Ransomware is a typical encryption ransomware virus that can be double-clicked into the action. It is packed as an executable file, but the threat can be launched by using Command Line (Command Prompt) utility in the Windows only. Most computer users may not be familiar with the CMD, because it is a program of command line interpreter and most of the system users rely on the graphical interface in order to issue commands to the Windows. The malware researchers suspects that this ransomware threat may be a test version of an upcoming nasty ransomware, because CommandLine Ransomware physical access to the targeted systems and the usage of remote access tool, such as BlackShades and Shady Rat.
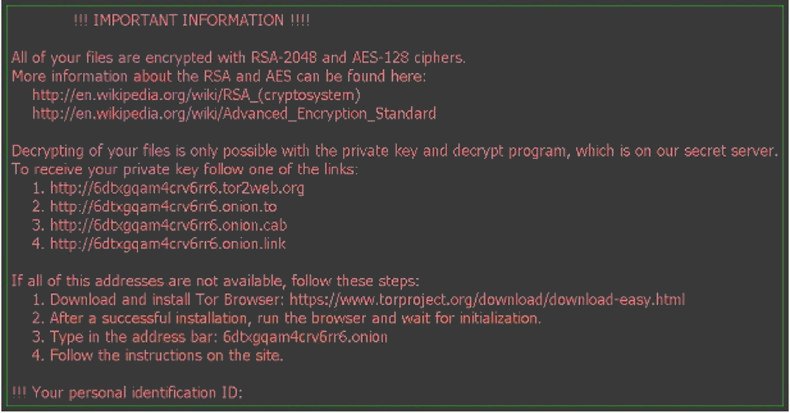
Some PC users suspect that the CommandLine Ransomware threat may be a program which is the subject of the research into how the malware works, as before we have seen with the EduCrypt Ransomware and ShinoLocker ransomware. This ransomware virus can encrypt the system files by using an AES cipher and provides the following options while executed:
- Encrypt Files and Rename File.
- Encrypt Files and Delete File.
- Decrypt System Files
- Decrypt the Files except Header.
Additionally, CommandLine Ransomware threat might be programmed to delete Shadow Volume Copies stored by the Windows and corrupt the Master Boot Record (MBR) file. Consequently, the malware may delete the backups made by the Windows, as well as prevent the computer from booting from the local drives. Users may see a newer version of this ransomware virus that is customized in order to display a lock system screen during the boot up process. The practice was introduced with the malware like the HDD Encrypt Ransomware and the BrLock Ransomware.
Although, a deep analysis on the CommandLine Ransomware confirmed that the threat does not communicate with the 'Command and Control' (C&C) server and work similarly to Bucbi Ransomware virus. That leads the security analysts to believe that the computer users may directed to contact with the email address in order to gain a decryptor. Most variants of Crysis Ransomware threats are known to suggest the PC users to write an email to the accounts hosted on the India.com, yandex.ru, mail2tor.com and protonmail.com.
Most ransomware viruses that uses the encryption method force system into paying a ransom money tend to require from 0.5 Bitcoin to 1 BTC. At the time of writing this article, the 1 BTC is exchanged for the 687 US Dollar and the machine users infected by the variant of CommandLine Ransomware virus may consider paying the ransom fee demanded by the con artists. However, it is a not a good idea for paying ransom money to the attackers, because the crypto malware creators are not the trustworthy fellows. Thus, better to use the backup copies and archive stored on the removable storage which is not connected to your system at the time of this ransomware infection. Hence you will need to clean CommandLine Ransomware from your PC and with a reliable and powerful anti-malware scanner before you continue to recover your computer data.
Free Scan your Windows PC to detect CommandLine Ransomware
Free Scan your Windows PC to detect CommandLine Ransomware
Best Video Removal Guide To Get Rid of CommandLine Ransomware
A: How To Remove CommandLine Ransomware From Your PC
Step: 1 How to Reboot Windows in Safe Mode with Networking.
- Click on Restart button to restart your computer
- Press and hold down the F8 key during the restart process.
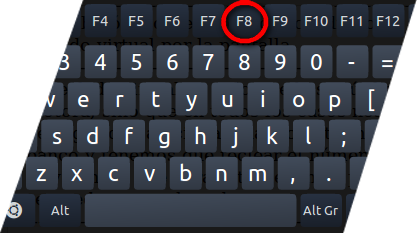
- From the boot menu, select Safe Mode with Networking using the arrow keys.
Step: 2 How to Kill CommandLine Ransomware Related Process From Task Manager
- Press Ctrl+Alt+Del together on your keyboard

- It will Open Task manager on Windows
- Go to Process tab, find the CommandLine Ransomware related Process.
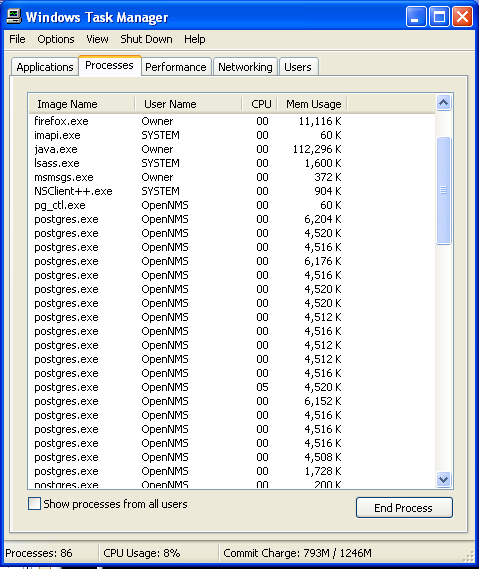
- Now click on on End Process button to close that task.
Step: 3 Uninstall CommandLine Ransomware From Windows Control Panel
- Visit the Start menu to open the Control Panel.
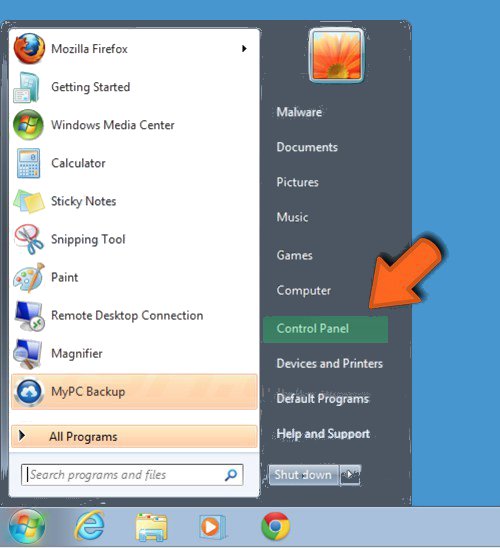
- Select Uninstall a Program option from Program category.
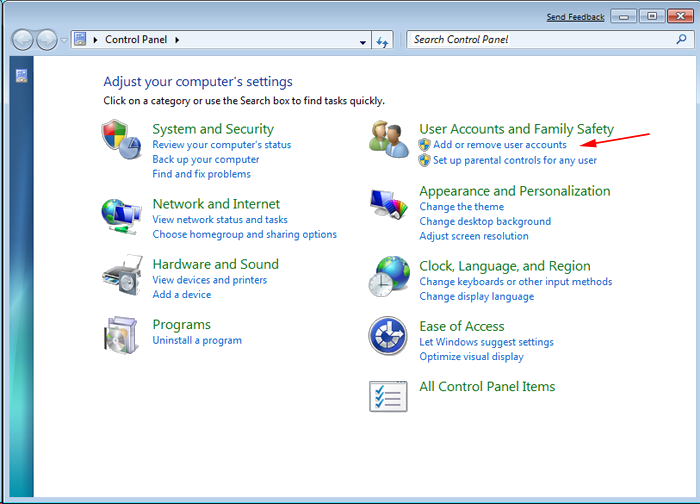
- Choose and remove all CommandLine Ransomware related items from list.

B: How to Restore CommandLine Ransomware Encrypted Files
Method: 1 By Using ShadowExplorer
After removing CommandLine Ransomware from PC, it is important that users should restore encrypted files. Since, ransomware encrypts almost all the stored files except the shadow copies, one should attempt to restore original files and folders using shadow copies. This is where ShadowExplorer can prove to be handy.
Download ShadowExplorer Now
- Once downloaded, install ShadowExplorer in your PC
- Double Click to open it and now select C: drive from left panel
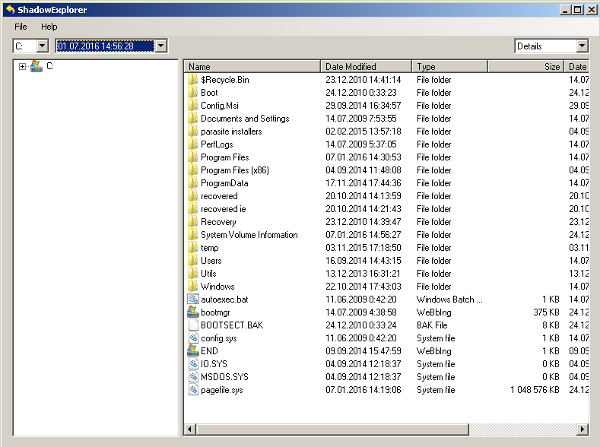
- In the date filed, users are recommended to select time frame of atleast a month ago
- Select and browse to the folder having encrypted data
- Right Click on the encrypted data and files
- Choose Export option and select a specific destination for restoring the original files
Method:2 Restore Windows PC to Default Factory Settings
Following the above mentioned steps will help in removing CommandLine Ransomware from PC. However, if still infection persists, users are advised to restore their Windows PC to its Default Factory Settings.
System Restore in Windows XP
- Log on to Windows as Administrator.
- Click Start > All Programs > Accessories.

- Find System Tools and click System Restore
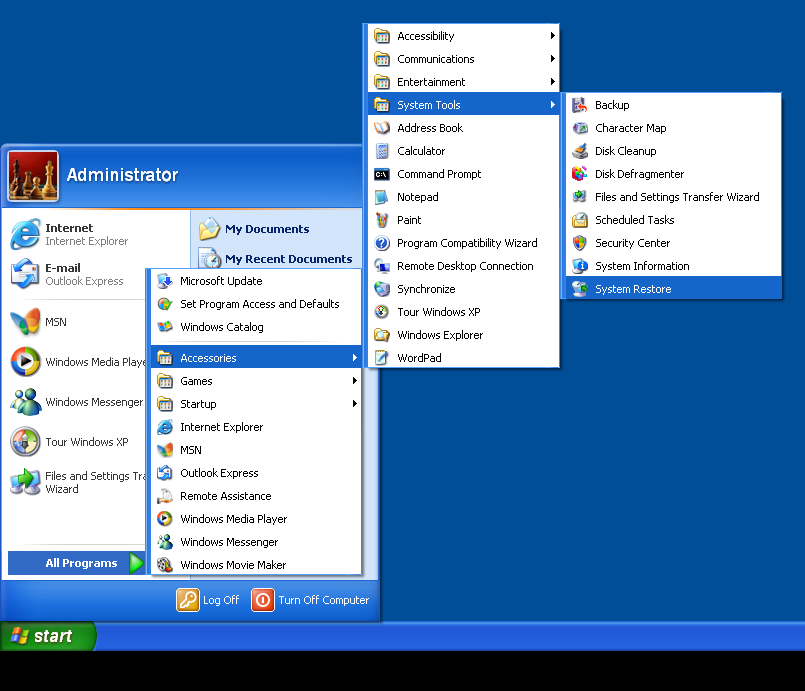
- Select Restore my computer to an earlier time and click Next.
- Choose a restore point when system was not infected and click Next.
System Restore Windows 7/Vista
- Go to Start menu and find Restore in the Search box.

- Now select the System Restore option from search results
- From the System Restore window, click the Next button.

- Now select a restore points when your PC was not infected.

- Click Next and follow the instructions.
System Restore Windows 8
- Go to the search box and type Control Panel

- Select Control Panel and open Recovery Option.

- Now Select Open System Restore option

- Find out any recent restore point when your PC was not infected.

- Click Next and follow the instructions.
System Restore Windows 10
- Right click the Start menu and select Control Panel.

- Open Control Panel and Find out the Recovery option.

- Select Recovery > Open System Restore > Next.

- Choose a restore point before infection Next > Finish.

Method:3 Using Data Recovery Software
Restore your files encrypted by CommandLine Ransomware with help of Data Recovery Software
We understand how important is data for you. Incase the encrypted data cannot be restored using the above methods, users are advised to restore and recover original data using data recovery software.



