
Brief Note on Shutdown57 Ransomware
These days, ransom demanding ransomware are on a rise. Among all, Shutdown57 Ransomware is one of the most popular and another untraditional ransomware that based on the the open source AwesomeWare virus which has been emerged more than 1 year ago. The appearance of this ransomware was reported by malware researchers and compromised companies that it introduced inside the System secretly through compromised Remote Desktop Protocol connections. Similar to the other variant of ransomware, it aims to make all files unreadable and extort money from victims.
Propagation Techniques of Shutdown57 Ransomware
The con artists of Shutdown57 Ransomware uses several deceptive or tricky ways to lurk inside the Computer. Some of the most common distribution channels are listed below :
- Infected emails or attachments – The scammers usually create the legitimate looking files and inject the suspicious scripts to confuse user. Opening of those attachment can automatically download Shutdown57 Ransomware.
- Malvertising and exploit kits – Clicking on any suspicious ads or links may also lead you to this infection.
- Freeware or shareware packages – Downloading and installing of any cost free application from untrusted sites are another sources of ransomware transmission.
- Infected Removal Devices – Use of any infected external device to share or transfer data may also victimized you through this infection.
- Others – Apart from these, its developers uses several other tricky or deceptive ways to attack Windows PC including torrent files, P2P file sharing network, illegal software packs etc.
Infection Flow of Shutdown57 Ransomware
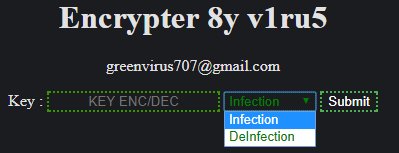
It mainly targets the web servers and locks entire stored files with strong AES-128 block cipher algorithm. The locked files of the ransomware can be easily identified because it adds “.shutdown57” file extensions at the end of the file name. As a result, stored files become inaccessible. On the completion of successful file encryption procedure, it leaves a ransom note and display a short message which looks like as follow :
File Decryption Method of Shutdown57 Ransomware
In the above image, you can see that the creator of this ransomware provided an email address for victim to get in contact with her/him. However, security analysts are strictly advised you to avoid contact with given email address because through this way cyber hacker is going to ask you to pay the ransom fee. By paying ransom fee you only encourage them to promote their evil intention because there is no any assurances given by its con artists to deliver the decryption key even paying off the ransom fee. Data or file decryption is possible using a data backup but if you have not then at that case, you need to take an action immediately regarding the deletion of Shutdown57 Ransomware.
Free Scan your Windows PC to detect Shutdown57 Ransomware
Free Scan your Windows PC to detect Shutdown57 Ransomware
A: How To Remove Shutdown57 Ransomware From Your PC
Step: 1 How to Reboot Windows in Safe Mode with Networking.
- Click on Restart button to restart your computer
- Press and hold down the F8 key during the restart process.
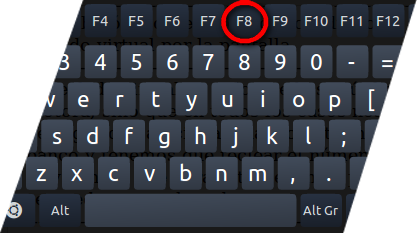
- From the boot menu, select Safe Mode with Networking using the arrow keys.
Step: 2 How to Kill Shutdown57 Ransomware Related Process From Task Manager
- Press Ctrl+Alt+Del together on your keyboard

- It will Open Task manager on Windows
- Go to Process tab, find the Shutdown57 Ransomware related Process.
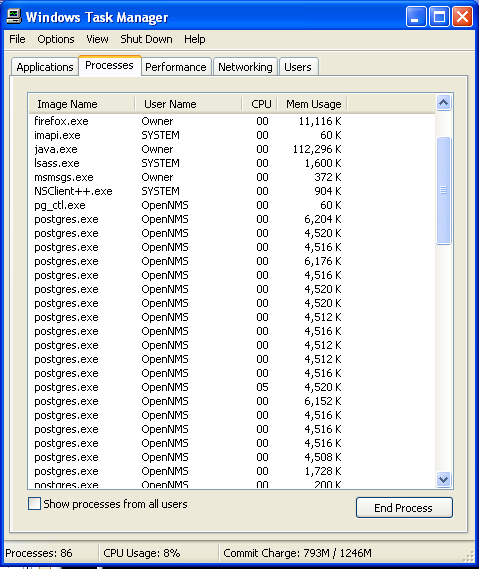
- Now click on on End Process button to close that task.
Step: 3 Uninstall Shutdown57 Ransomware From Windows Control Panel
- Visit the Start menu to open the Control Panel.
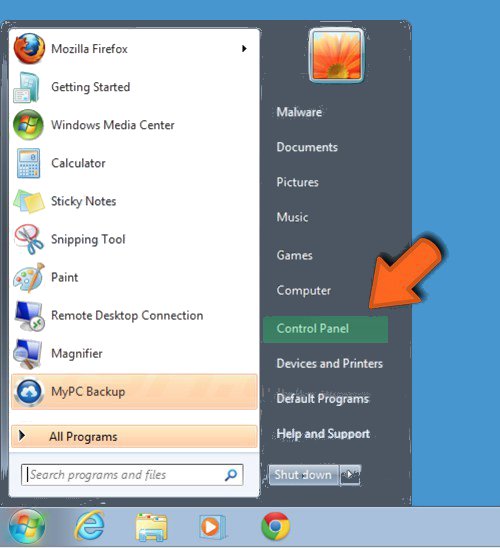
- Select Uninstall a Program option from Program category.
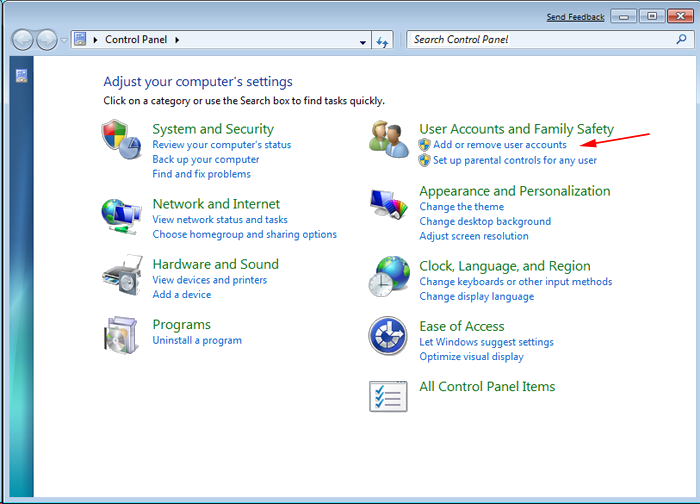
- Choose and remove all Shutdown57 Ransomware related items from list.

B: How to Restore Shutdown57 Ransomware Encrypted Files
Method: 1 By Using ShadowExplorer
After removing Shutdown57 Ransomware from PC, it is important that users should restore encrypted files. Since, ransomware encrypts almost all the stored files except the shadow copies, one should attempt to restore original files and folders using shadow copies. This is where ShadowExplorer can prove to be handy.
Download ShadowExplorer Now
- Once downloaded, install ShadowExplorer in your PC
- Double Click to open it and now select C: drive from left panel
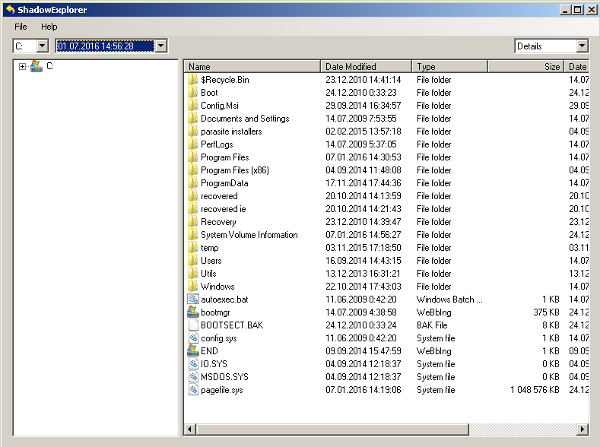
- In the date filed, users are recommended to select time frame of atleast a month ago
- Select and browse to the folder having encrypted data
- Right Click on the encrypted data and files
- Choose Export option and select a specific destination for restoring the original files
Method:2 Restore Windows PC to Default Factory Settings
Following the above mentioned steps will help in removing Shutdown57 Ransomware from PC. However, if still infection persists, users are advised to restore their Windows PC to its Default Factory Settings.
System Restore in Windows XP
- Log on to Windows as Administrator.
- Click Start > All Programs > Accessories.

- Find System Tools and click System Restore
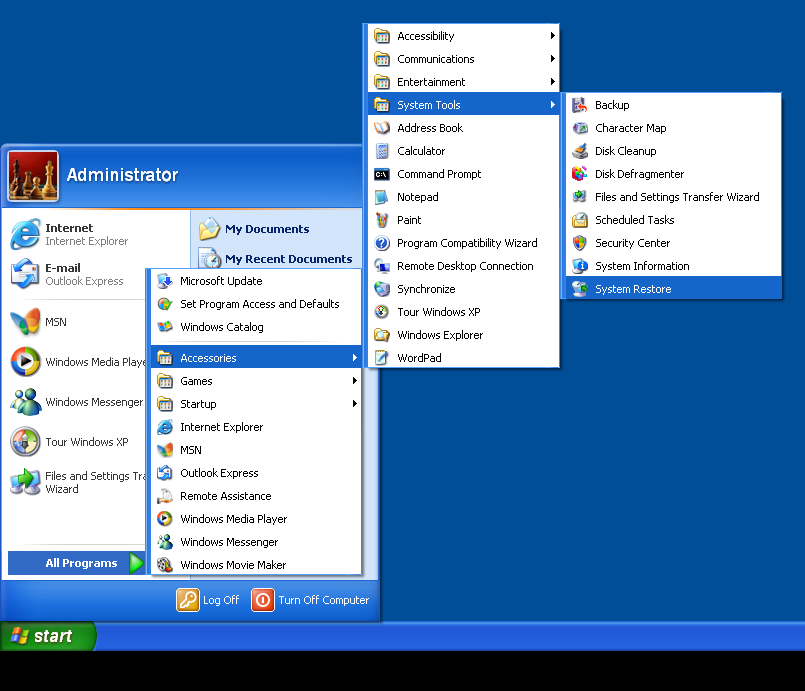
- Select Restore my computer to an earlier time and click Next.
- Choose a restore point when system was not infected and click Next.
System Restore Windows 7/Vista
- Go to Start menu and find Restore in the Search box.

- Now select the System Restore option from search results
- From the System Restore window, click the Next button.

- Now select a restore points when your PC was not infected.

- Click Next and follow the instructions.
System Restore Windows 8
- Go to the search box and type Control Panel

- Select Control Panel and open Recovery Option.

- Now Select Open System Restore option

- Find out any recent restore point when your PC was not infected.

- Click Next and follow the instructions.
System Restore Windows 10
- Right click the Start menu and select Control Panel.

- Open Control Panel and Find out the Recovery option.

- Select Recovery > Open System Restore > Next.

- Choose a restore point before infection Next > Finish.

Method:3 Using Data Recovery Software
Restore your files encrypted by Shutdown57 Ransomware with help of Data Recovery Software
We understand how important is data for you. Incase the encrypted data cannot be restored using the above methods, users are advised to restore and recover original data using data recovery software.



