Deadly Ransomware Proven Actually Deadly : How Does It Act ?
Deadly Ransomware has been identified as a name of the new crypto-ransomware virus discovered in the middle of October 2016. Now since it is very common for ransomware authors to generate numerous distinct variants of their threatening programs. So, same is the case with the afore stated ransomware program also. It is a threat that seems to be developed to initialize encrypting files in 2017. Researches have revealed that this malicious program has been scripted on the .NET Framework and thus it is comparatively easy to identify it's operations. This threat has been labeled by distinct names via different antimalware vendors same as Trojan/Win32.Agent.N2124761547, Trojan.GenericKD.3586576 (B), Trojan.Win32.Agent.nexptm, Ransom_JANBLEED.F116JA, MSIL/Filecoder.CS, Atros4.ABVF.
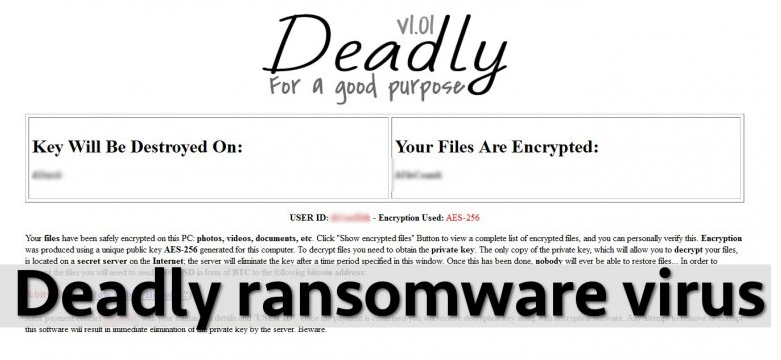
Deadly Ransomware likewise various other ransomware program such as Aga Ransomware sneaks secretly inside the PC via utilizing Trojan horse technique. Then after following that propagates number of vicious files on the compromised computer system, get prepared for the attack and then implement itself. The vicious processes it executes actually scans the entire PC in search of certain file extensions that it can infects and on finding them encrypts them. After this generates a ransom screen on the desktop notifying users about the successful encryption of the data. This ransomware program claims of utilizing the AES-456 cipher to encrypt the data but yet there is no evidence found supporting the claim. It has been proven by malware researchers that the aforementioned threat has been poorly configured and thus do not provide any sort of ID number and payment instructions.
The ransom screen generated by Deadly Ransomware actually appears like a template that might receive updates including a new color scheme, text message and new design. The screen very clearly states the system's files have been successfully encrypted including documents, photos, videos etc. Further the victims are suggested to tap “Show encrypted files” button in order to view the complete lost of encrypted files. Moreover victims are also informed that encryption was produces utilizing a unique public key called AES-256 and so regarding decryption, one need to obtain the private key whose only copy can enable one to decrypt the encrypted or locked files located on the secret server on the Internet. Aside from all this, victims are suggested to access the private key as quick as possible since the key has been programmed in such a way that it will automatically get eradicated by the server after certain time interval specified in the Window. Now to make access to the private key once need to transfer $500 USD in the form of BTC to the given below bitcoin address :
&bitwallet& (link to a guide on how to buy and transfer Bitcoins)
After the payment contact [email contact] with victim's transaction details and [victim's ID]. After the completion of the payment procedure victims are provided with decryption key along with decryption software. Now generally it has been noticed that victims in such sort of situation decides to pay in the hope that after making the payment their issue of accessing the files back will get resolve but it is strongly suggested not do so as it has been proven the after the once the payment gets done, the hackers ignore victims instead of decrypting their files. Thus, regarding complete protection of the system;s files it is literally very important to remove Deadly Ransomware quickly from the PC.
How Deadly Ransomware Invade And It's harmful Impact
Allegedly, Deadly Ransomware mostly distributes itself through a vicious implementable containing an exploit kit or a .js file including JavaScript. Aside from this, it often propagates through a vicious e-mail attachments of fake setups uploaded online. It once loaded, brings modification in the system's default settings and steals the user's private stuff which is then later on revealed to the cyber criminals regarding evil purpose. This malicious threat also invade several other vicious infections in the PC. Hence, to keep the PC as well as stored in it away from such treacherous issues, it is very necessary to uninstall Deadly Ransomware quickly from the PC.
Free Scan your Windows PC to detect Deadly Ransomware
How To Remove Deadly Ransomware Virus Manually
Step 1 : Restart your computer in safe with networking
- Restart your computer and keep pressing F8 key continuously.

- You will find the Advance Boot Option on your computer screen.

- Select Safe Mode With Networking Option by using arrow keys.
- Login your computer with Administrator account.
Step 2 : Step all Deadly Ransomware related process
- Press the Windows+R buttons together to open Run Box.

- Type “taskmgr” and Click OK or Hit Enter button.

- Now go to the Process tab and find out Deadly Ransomware related process.

- Click on End Process button to stop that running process.
Step 3 : Restore Your Windows PC To Factory Settings
System Restore Windows XP
- Log on to Windows as Administrator.
- Click Start > All Programs > Accessories.

- Find System Tools and click System Restore.
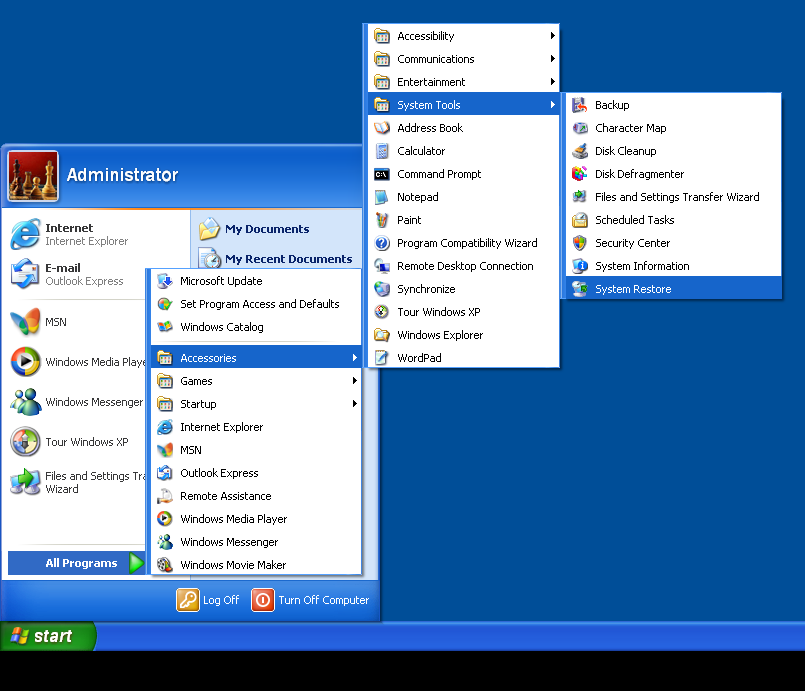
- Select Restore my computer to an earlier time and click Next.
- Choose a restore point when system was not infected and click Next.
System Restore Windows 7/Vista
- Go to Start menu and find Restore in the Search box.

- Now select the System Restore option from search results.
- From the System Restore window, click the Next button.
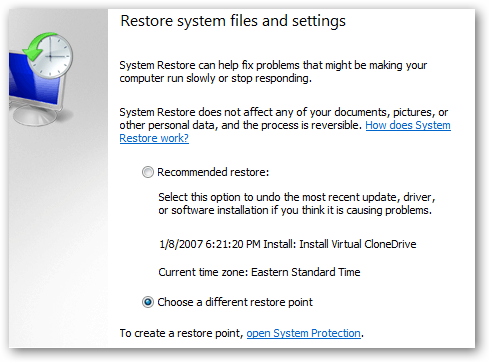
- Now select a restore points when your PC was not infected.
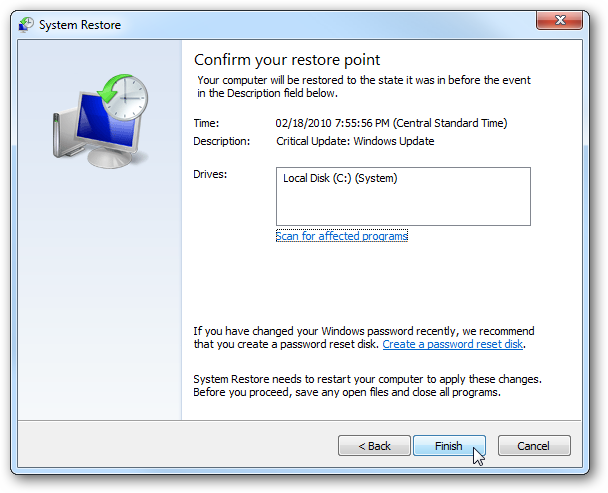
- Click Next and follow the instructions.
System Restore Windows 8
- Go to the search box and type Control Panel.

- Select Control Panel and open Recovery Option.

- Now Select Open System Restore option.

- Find out any recent restore point when your PC was not infected.

- Click Next and follow the instructions.
System Restore Windows 10
- Right click the Start menu and select Control Panel.
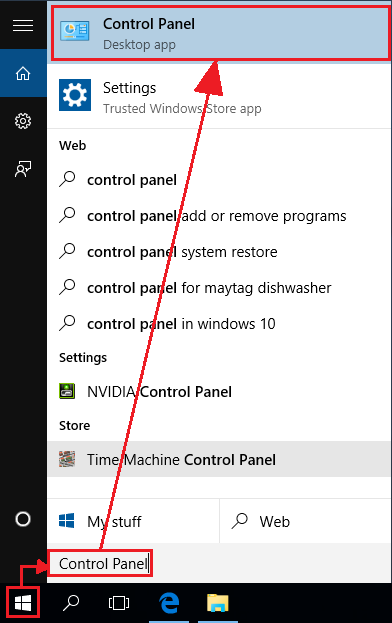
- Open Control Panel and Find out the Recovery option.

- Select Recovery > Open System Restore > Next.

- Choose a restore point before infection Next > Finish.

Hope these manual steps help you successfully remove the Deadly Ransomware infection from your computer. If you have performed all the above manual steps and still can’t access your files or cannot remove this nasty ransomware infection from your computer then you should choose a powerful malware removal tool. You can easily remove this harmful virus from your computer by using third party tool. It is the best and the most easy way to get rid of this infection.
If you have any further question regarding this threat or its removal then you can directly ask your question from our experts. A panel of highly experienced and qualified tech support experts are waiting to help you.




