| Warning, many anti-virus scanner have detected Wesker Ransomware as threat to your computer | ||
| Wesker Ransomware is flagged by these Anti Virus Scanner | ||
| Anti Virus Software | Version | Detection |
| eScan | 2018.3.4845 | Generic |
| Kingsoft | 7.3.622513 | Trj.Win64.Wesker Ransomware.BA |
| AutoShun | 5.657221 | Variant of Win64/Trojan.Wesker Ransomware.A |
| ZDB Zeus | 8.1.651 | Mdelk.exe, MalwareMonitor |
| Suggestion: Uninstall Wesker Ransomware Completely – Free Download | ||
Wesker Ransomware may have entered your pc through these software. If you have not installed them , then get rid of them TotalFX v3.0 , Mr. Tides 4.3.0 , Picture Collage Maker 3.1.2 , EiffelStudio 6.6.8.2636 , Wine Cellar 1.4 , Smileys Challenge X 1.0 , iServices Trojan Removal Tool 1.1 , Wild West Quest 1.0 , TuneExplorer 1.0b100 , XPert Print 2.1.3 , Speedster 1.0 , Tattoo X 1.2 , weaverFM 1.5.0 , Studio Organizer 10.3 , Rogue Touch 1.6 , IPSecuritas 4.0rc1 , Shutter Bug 1.0 , The Journeyman Project: Pegasus Prime 1.6.0 , Laryngitis 1.0 |
|

All Important Facts of Wesker Ransomware That You Must Know
Wesker Ransomware is an updated or latest variant of its Ransomware family that uses the family file extension to lock almost all users content such as PDFs, images, audios, videos, documents, databases, PDFs and many more. Like its predecessor, it is designed in such a way that it can compromise almost all version of System based on Windows OS. It locks users all files using strong AES cipher algorithm and then it convince the affected users or victims to pay USD in BitCoin in about few days time. The primary objective of this ransomware is to set a deadline in order to pay ransom and if victims doesn’t complies, its creators threaten victims to destroy the file decryption key.
Transmission Preferences of Wesker Ransomware
Wesker Ransomware is too much identical to original threat except for new C&C server configuration and the new extension added to System file names. Being a part of the ransomware family, its developers uses lots of tricky and deceptive ways but mainly the payload is distributed via corrupted MS Word files and spam emails. Spam emails contains dubious attachment and malicious scripts. Opening of any spam message may lead you to this infection. Its developers uses lots of distribution channels to compromise Windows machine but mainly spread via Internet. Therefore, System users must be attentive while performing the online operation.
Actions Performed By Wesker Ransomware
- Enters inside the PC silently.
- Scans Windows PC in deep.
- Wesker Ransomware target almost all file types.
- Uses family file extension to lock almost all content.
- Renames original file name.
- Produces a program window.
- Degrades System working speed.
- Wesker Ransomware throws several fake security alerts, notifications or messages.
- Disables all firewall settings etc.
Free Scan your Windows PC to detect Wesker Ransomware
A: How To Remove Wesker Ransomware From Your PC
Step: 1 How to Reboot Windows in Safe Mode with Networking.
- Click on Restart button to restart your computer
- Press and hold down the F8 key during the restart process.
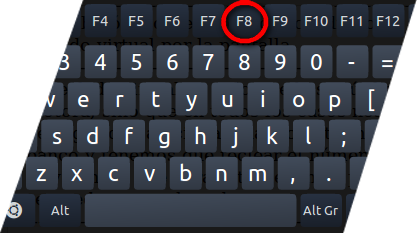
- From the boot menu, select Safe Mode with Networking using the arrow keys.
Step: 2 How to Kill Wesker Ransomware Related Process From Task Manager
- Press Ctrl+Alt+Del together on your keyboard

- It will Open Task manager on Windows
- Go to Process tab, find the Wesker Ransomware related Process.
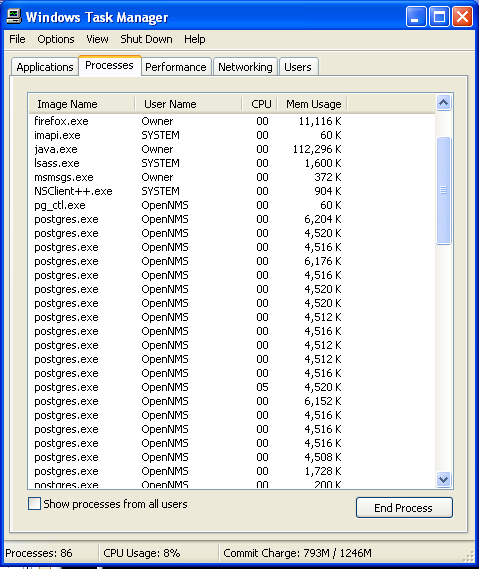
- Now click on on End Process button to close that task.
Step: 3 Uninstall Wesker Ransomware From Windows Control Panel
- Visit the Start menu to open the Control Panel.
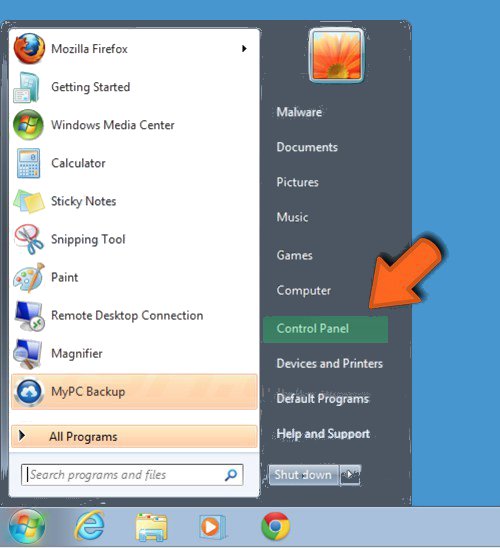
- Select Uninstall a Program option from Program category.
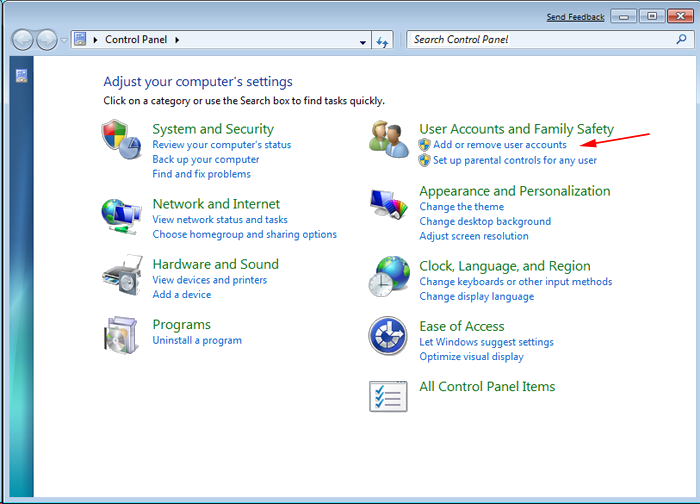
- Choose and remove all Wesker Ransomware related items from list.

B: How to Restore Wesker Ransomware Encrypted Files
Method: 1 By Using ShadowExplorer
After removing Wesker Ransomware from PC, it is important that users should restore encrypted files. Since, ransomware encrypts almost all the stored files except the shadow copies, one should attempt to restore original files and folders using shadow copies. This is where ShadowExplorer can prove to be handy.
Download ShadowExplorer Now
- Once downloaded, install ShadowExplorer in your PC
- Double Click to open it and now select C: drive from left panel
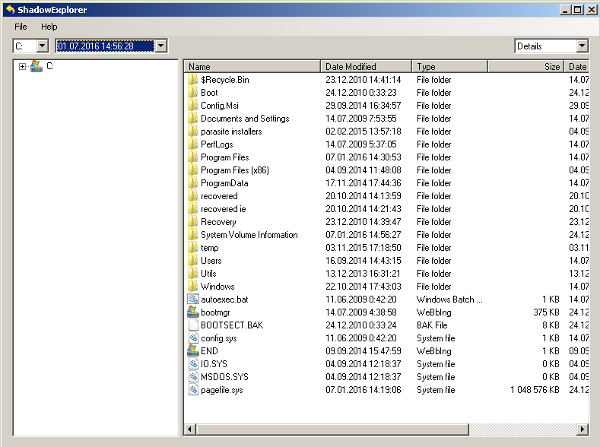
- In the date filed, users are recommended to select time frame of atleast a month ago
- Select and browse to the folder having encrypted data
- Right Click on the encrypted data and files
- Choose Export option and select a specific destination for restoring the original files
Method:2 Restore Windows PC to Default Factory Settings
Following the above mentioned steps will help in removing Wesker Ransomware from PC. However, if still infection persists, users are advised to restore their Windows PC to its Default Factory Settings.
System Restore in Windows XP
- Log on to Windows as Administrator.
- Click Start > All Programs > Accessories.

- Find System Tools and click System Restore
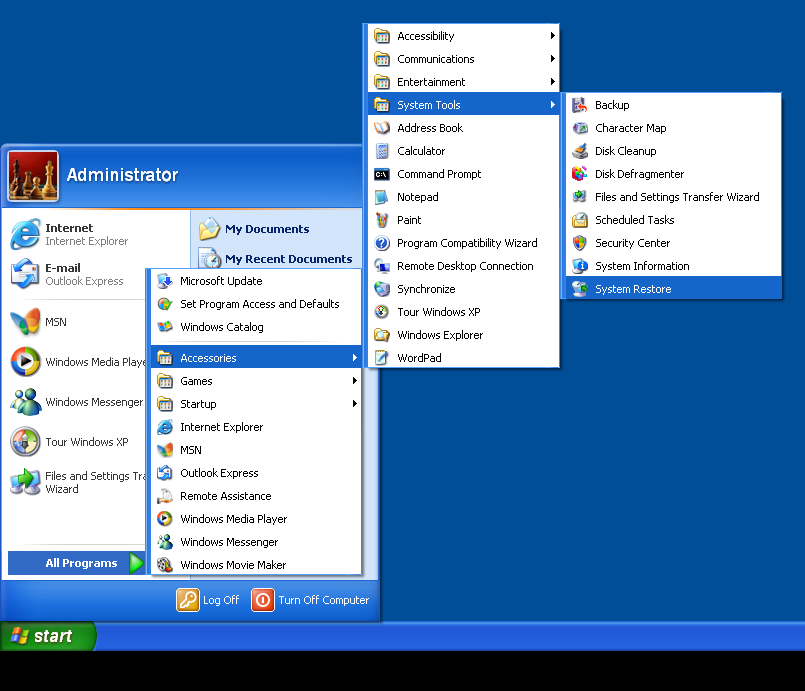
- Select Restore my computer to an earlier time and click Next.
- Choose a restore point when system was not infected and click Next.
System Restore Windows 7/Vista
- Go to Start menu and find Restore in the Search box.

- Now select the System Restore option from search results
- From the System Restore window, click the Next button.

- Now select a restore points when your PC was not infected.

- Click Next and follow the instructions.
System Restore Windows 8
- Go to the search box and type Control Panel

- Select Control Panel and open Recovery Option.

- Now Select Open System Restore option

- Find out any recent restore point when your PC was not infected.

- Click Next and follow the instructions.
System Restore Windows 10
- Right click the Start menu and select Control Panel.

- Open Control Panel and Find out the Recovery option.

- Select Recovery > Open System Restore > Next.

- Choose a restore point before infection Next > Finish.

Method:3 Using Data Recovery Software
Restore your files encrypted by Wesker Ransomware with help of Data Recovery Software
We understand how important is data for you. Incase the encrypted data cannot be restored using the above methods, users are advised to restore and recover original data using data recovery software.

