Files encrypted by [email protected] Virus? Don't want to pay ransom demanded fee? Searching for best removal guide to delete it? If yes, keep reading this post and follow the below mentioned ransomware removal instruction carefully.

[email protected] Virus : It's Analysis Report
| Threat's Name | [email protected] Virus |
| Threat's Type | Crypto-Malware virus, File encrypting Virus |
| Category | Ransomware |
| Affected Systems | Windows OS |
| Description | [email protected] Virus is another variant of ransomware virus created by cyber crooks to rob money from victims. |
| Distribution Channels | Shareware or freeware packages, torrent downloads, spam mail attachments, illegal software update links, malicious links or porn sites etc. |
| Harmful Effects |
|
| Removal | Possible, to delete [email protected] Virus easily and completely you must download free windows scanner tool. |
Detailed Information of [email protected] Virus
[email protected] Virus is one of the high risk System infection belongs to the ransomware family. Being a ransomware, it proliferate inside the Windows PC silently and after that it allow remote hackers to access the affected machine in order to execute malicious codes that lock user's all stored files with notorious and nasty extension. It will not only take control of your Computer but also indicate it to perform what actually it wants.
Intrusion Method of [email protected] Virus
According to the security analysts, the developers of [email protected] Virus uses numerous channels to infect Windows System but most of the cases, it inserts its payload into the spam mail attachments containing dubious attachments and malicious links. When System users download or open any attachments then there is high chance that their System is victimized by this infection. Besides spam campaigns, it uses other tricky channels to victimized PC including torrent downloads, bundling method, gambling or hacked domain, pirated software, file sharing sources etc.
Working Tactics of [email protected] Virus
Once invading inside the Windows PC successfully, first of all it disables functionalities of security software and tools and after that it immediately start to perform encryption procedure. It scans Windows PC and target user's mostly used files types such as images, audio or video files, PDFs, documents, databases etc. After making files inaccessible, it asks victim to purchase the unique decryption key to decrypt files. But according to security analysts, the services provided by it's developers are unsecured and they don't give you any decryption key even paying huge amount of ransom fee. Therefore, it is highly advised to get rid of [email protected] Virus immediately after getting it's any harmful symptoms.
Free Scan your Windows PC to detect [email protected] Virus
Free Scan your Windows PC to detect [email protected] Virus
A: How To Remove [email protected] Virus From Your PC
Step: 1 How to Reboot Windows in Safe Mode with Networking.
- Click on Restart button to restart your computer
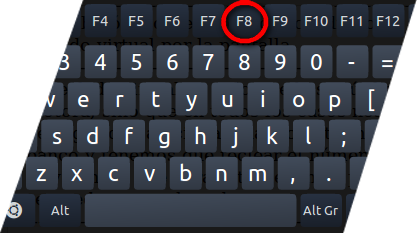
- Press and hold down the F8 key during the restart process.
- From the boot menu, select Safe Mode with Networking using the arrow keys.
Step: 2 How to Kill [email protected] Virus Related Process From Task Manager
- Press Ctrl+Alt+Del together on your keyboard

- It will Open Task manager on Windows
- Go to Process tab, find the [email protected] Virus related Process.
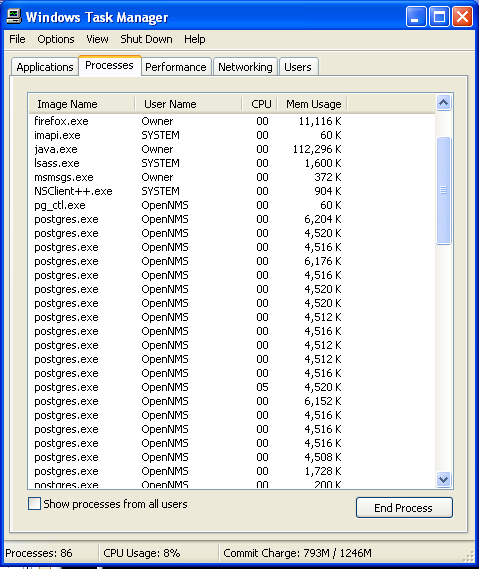
- Now click on on End Process button to close that task.
Step: 3 Uninstall [email protected] Virus From Windows Control Panel
- Visit the Start menu to open the Control Panel.
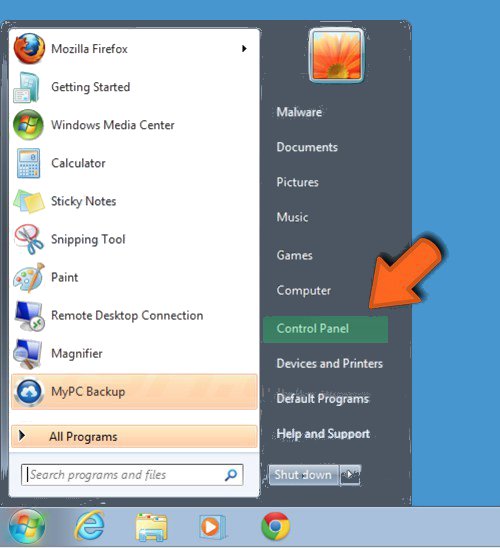
- Select Uninstall a Program option from Program category.
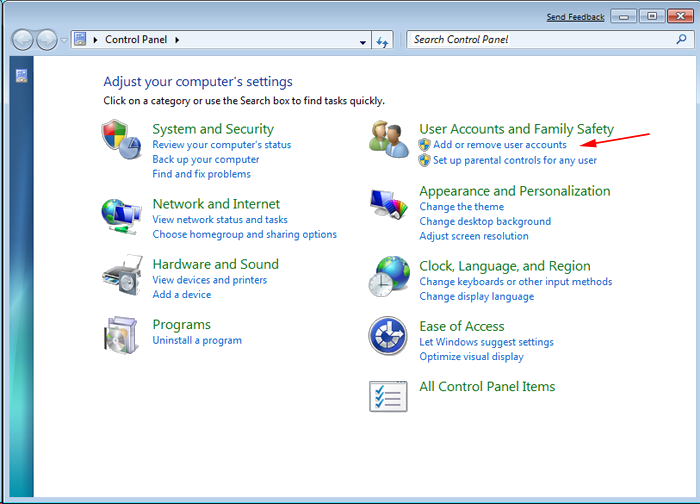
- Choose and remove all [email protected] Virus related items from list.

B: How to Restore [email protected] Virus Encrypted Files
Method: 1 By Using ShadowExplorer
After removing [email protected] Virus from PC, it is important that users should restore encrypted files. Since, ransomware encrypts almost all the stored files except the shadow copies, one should attempt to restore original files and folders using shadow copies. This is where ShadowExplorer can prove to be handy.
Download ShadowExplorer Now
- Once downloaded, install ShadowExplorer in your PC
- Double Click to open it and now select C: drive from left panel
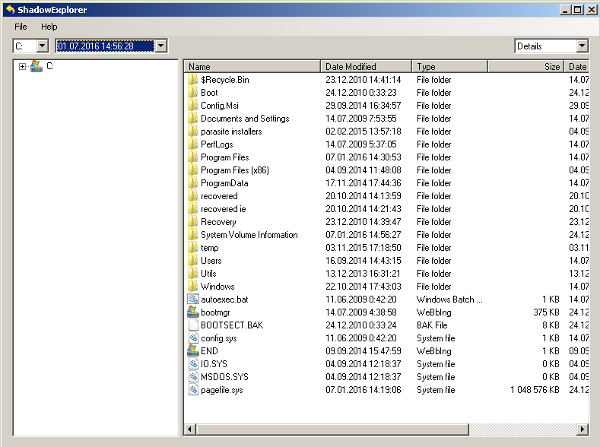
- In the date filed, users are recommended to select time frame of atleast a month ago
- Select and browse to the folder having encrypted data
- Right Click on the encrypted data and files
- Choose Export option and select a specific destination for restoring the original files
Method:2 Restore Windows PC to Default Factory Settings
Following the above mentioned steps will help in removing [email protected] Virus from PC. However, if still infection persists, users are advised to restore their Windows PC to its Default Factory Settings.
System Restore in Windows XP
- Log on to Windows as Administrator.
- Click Start > All Programs > Accessories.

- Find System Tools and click System Restore
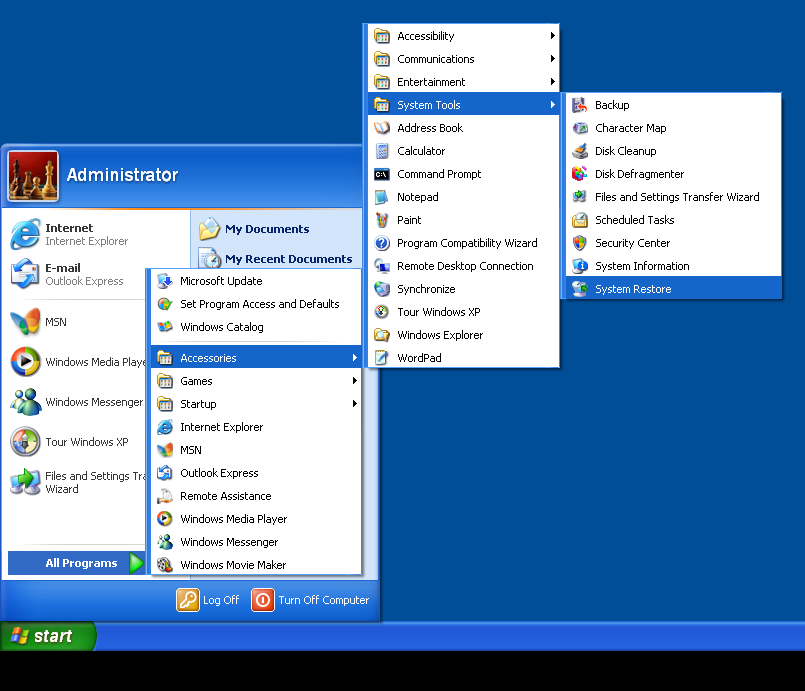
- Select Restore my computer to an earlier time and click Next.
- Choose a restore point when system was not infected and click Next.
System Restore Windows 7/Vista
- Go to Start menu and find Restore in the Search box.

- Now select the System Restore option from search results
- From the System Restore window, click the Next button.

- Now select a restore points when your PC was not infected.

- Click Next and follow the instructions.
System Restore Windows 8
- Go to the search box and type Control Panel

- Select Control Panel and open Recovery Option.

- Now Select Open System Restore option

- Find out any recent restore point when your PC was not infected.

- Click Next and follow the instructions.
System Restore Windows 10
- Right click the Start menu and select Control Panel.

- Open Control Panel and Find out the Recovery option.

- Select Recovery > Open System Restore > Next.

- Choose a restore point before infection Next > Finish.

Method:3 Using Data Recovery Software
Restore your files encrypted by [email protected] Virus with help of Data Recovery Software
We understand how important is data for you. Incase the encrypted data cannot be restored using the above methods, users are advised to restore and recover original data using data recovery software.



