| Warning, many anti-virus scanner have detected [email protected] Ransomware as threat to your computer | ||
| [email protected] Ransomware is flagged by these Anti Virus Scanner | ||
| Anti Virus Software | Version | Detection |
| TrendMicro | 2018.4.7101 | Generic |
| Malwarebytes | 3.1.647429 | [email protected] Ransomware.AC |
| AutoShun | 4.129135 | Variant of Win64/[email protected] Ransomware.C |
| ZeusTracker | 6.4.603 | Vnbptxlf Toolbar, Internet Spy |
| Suggestion: Uninstall [email protected] Ransomware Completely – Free Download | ||
[email protected] Ransomware may have entered your pc through these software. If you have not installed them , then get rid of them Bitdefender Antivirus 3.0.7135 , CatHide 0.9.7 , 4Easysoft Pocket PC Video Converter , MiniStumble Safari Extension 2.0 , TeamDrive , fizz 1.0 , Change Printer 4.0.6.1 , ideaSpiral 1.5.4 , Graphviz , TubeTwist 1.0 , Tick 1.10 , Slick3D Maintenance , MyTunesControllerPlus 1.14 , Mac-O-Lantern 1.3.1 , FileMaker Go for iPad 1.0.3 |
|
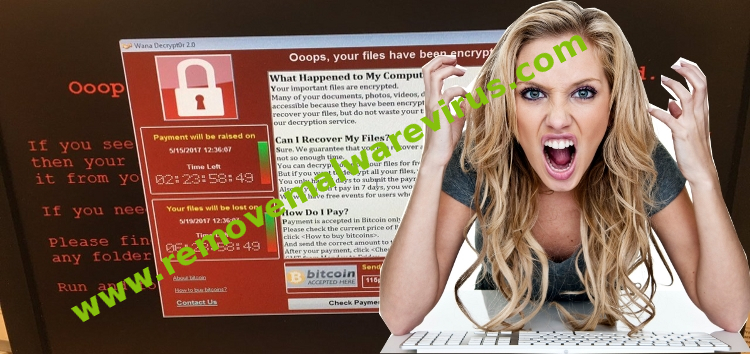
Threat Analysis Of [email protected] Ransomware
[email protected] Ransomware is a malicious program that has file encrypting capabilities and is used to receive ransom money from affected users. The ransomware was discovered recently and is believed to be a variant of its predecessor Ransomware. It has been found to be widely spreading through spam mails that are successful in deceiving users and making them believe that the contents within the mail are genuine. The ransomware immediately downloads its payload files from remote servers that are initiated through the scripts within the spam mails. [email protected] Ransomware can encrypt files of various kinds and has been observed to add an extension which seems valid to those infected files. This makes it different from other ransomware who are typically known to make the encrypted files prominent by adding their own names. The malware uses AES-128 and RSA-2048 encryption algorithm to successfully encrypt the files. Immediately after this process it sends the private decryption key to command and control center server of cyber-criminals. The files encrypted by [email protected] Ransomware cannot be used by users to read or make changes within. They can only be copied, moved or deleted by users. The ransomware leaves a ransom note named as ‘READ_ME.txt’ that informs users about the attack. The contents of the ransom note do not specify the ransom amount that needs to be paid by users in exchange of the decryption key that is promised to help them in recovering their file. However it does specify few email contacts that users may use to reach out for striking a negotiation. Affected users may think that this is the only alternative available to them to restore their encrypted data and should contact [email protected] Ransomware developers. But this is not true as they will find in the instructions given below.
[email protected] Ransomware can infect a system when users receive a spam mail that has been specially designed to deceive them. The mails that are circulated carrying the ransomware have documents that are embedded with macros. The subject line of these messages are used to catch receiver’s attention by using words such as product invoice, account details, ticket information and use design templates of reputed firms. When users click on these documents they are asked for permission to enable complete reading of the text which hides the macros within. Soon after users click on these the payload is downloaded and executed within the system to carryout the encryption process. [email protected] Ransomware can also delete shadow volume but users can still recover their files by following these instructions.
Remove [email protected] Ransomware From Your PC
Step 1: Remove [email protected] Ransomware in Safe Mode with Command Prompt
- First of all disconnect your PC with network connection.
- Click restart button and keep pressing F8 key regularly while system restart.

- You will see “Windows Advanced Options Menu” on your computer screen.
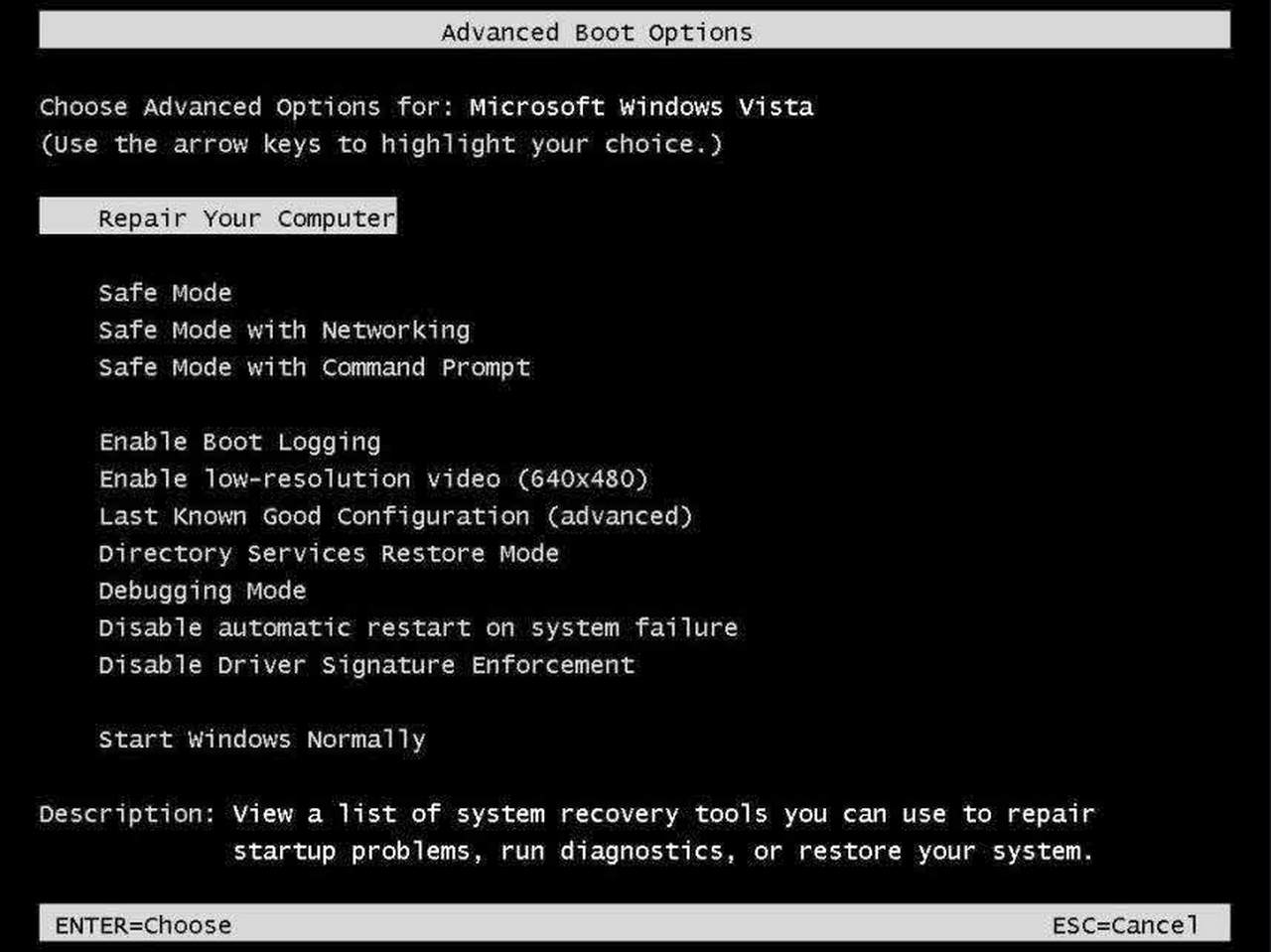
- Select “Safe Mode with Command Prompt” and press Enter key.
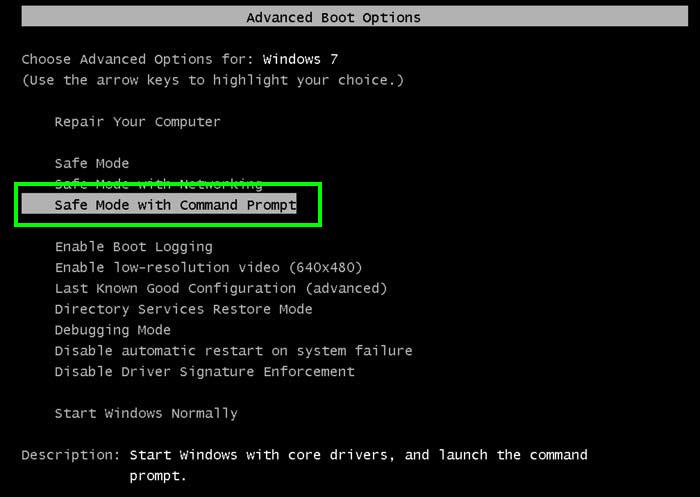
- You must login your computer with Administrator account for full privilege.

- Once the Command Prompt appears then type rstrui.exe and press Enter
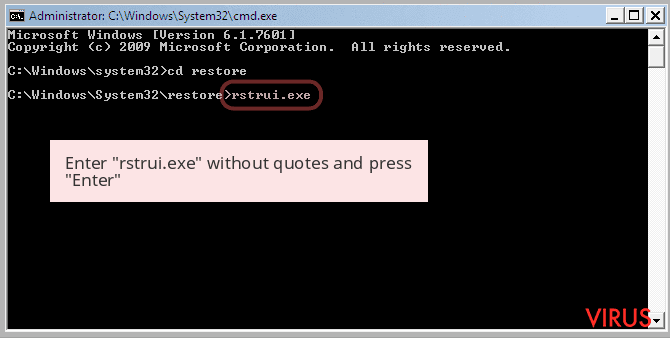
- Now follow the prompts on your screen to complete system restore.
Step 2: Remove [email protected] Ransomware using MSConfig in Safe Mode:
- Power off your computer and restart again.
- While booting press the “F8 key” continuously to open “Windows Advanced Options Menu”.

- Use the arrow keys to select “Safe Mode” option and press Enter key.

- Once system get started go to Start menu. Type “msconfig” in the search box and launch the application.

- Go to the Startup tab and look for files from %AppData% or %Temp% folders using rundll32.exe. See an example below:
C:\Windows\System32\rundll32.exe C:\Users\username\appdata\local\temp\regepqzf.dll,H1N1
- Disable all the malicious entries and save the changes.
- Now restart your computer normally.
Step 3 : Kill Malicious Process Related To [email protected] Ransomware
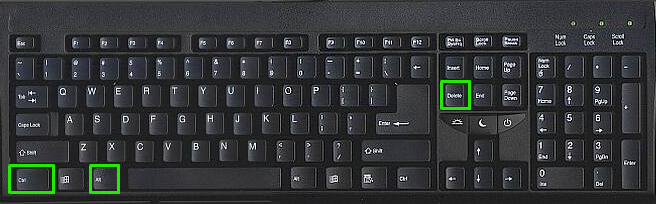
- Press Alt+Ctrl+Del buttons together.
- It will open the Task manager on your screen.
- Go to Process Tab and find [email protected] Ransomware related process.
- Click the End Process Now button to stop the running process.
Step 4 : Remove [email protected] Ransomware Virus From Registry Entry
- Press “Windows + R” key together to open Run Box.

- Type “regedit” and click OK button.

- Find and remove [email protected] Ransomware related entries.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnceEx
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunServices
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunServicesOnce
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Runonce
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunServices
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunServicesOnce
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run
Now hopefully you have completely removed the [email protected] Ransomware virus from your computer. If you are still get ransom message from the threat or unable to access your files, then it means that virus still remain into your computer. In such situation you don’t have any other option except removing this virus using any powerful malware removal tool.
Whereas if you have any backup of your infected or encrypted files, then you can also reinstall your Windows OS. This will erase all your files and data as along with the [email protected] Ransomware infection. You will get a completely empty computer system with no files. Now you can use your backup to get your files. If you don’t have any backup then using malware removal tool is a better option for you.
If you have any query or question regarding your computer, then you can easily ask your problem to our experts. Go to the Ask Any Question page and get the answer for your query directly from out experts.


