| Spoiler Vulnerability is a Keylogger | |
| Trojan Dropped by Spoiler Vulnerability are SoftwareBundler:Win32/MPAccess, Trojan-Clicker.Win32.VB.dgz, Troj/ExpJS-IV, Injector.gen!D, Net-Worm.Spybot.C!rem, TROJ_RODECAP.SM, Trojan.Dooxud.A, Trojan.Betabot, Proxy.Koobface.gen!L, Trojan.Downloader.Tonick.gen, Oficla.H!dll, TROJ_KILSRV.EUIQ | |
| Related spyware Sifr, EScorcher, IESearch, Spyware.IEPlugin, Wxdbpfvo Toolbar, Rogue.SpywarePro, Real Antivirus, SniperSpy, Safetyeachday.com, DoctorVaccine, SysSafe, Spyware.Mywebtattoo, Faretoraci | |
| Windows Error caused by Spoiler Vulnerability are – 0x8024E001 WU_E_EE_UNKNOWN_EXPRESSION An expression evaluator operation could not be completed because an expression was unrecognized., 0xf081A CBS_E_INVALID_DRIVER_OPERATION_KEY the driver operations key is corrupt or invalid, 0xf0818 CBS_E_IDENTITY_MISMATCH container package points to a package manifest whose identity doesn’t match the identity specified, 0x8024AFFF WU_E_AU_UNEXPECTED An Automatic Updates error not covered by another WU_E_AU * code. , 0x8024401E WU_E_PT_HTTP_STATUS_GONE Same as HTTP status 410 – requested resource is no longer available at the server., 0x000000A1, Error 0xC0000001, Error 0xC000021A | |
| Spoiler Vulnerability infects these windows .dll files sbscmp20_perfcounter.dll, regwizc.dll, mfc40u.dll, netiohlp.dll, BrSerIf.dll, ocsetapi.dll, BWUnpairElevated.dll, Vsavb7rtUI.dll, ehiExtens.dll, CPFilters.dll, nmmkcert.dll, inseng.dll, koc.dll, dpnet.dll |
Spoiler Vulnerability may have entered your pc through these software. If you have not installed them , then get rid of them X11 Extension 0.99u , Pirts 1.0.4 , NewzHog 1.0rc2 , Lost Photos 2.0 , JanusNode 2.12 , Investors Toolbox 1.1 , Keystrokes Pronouncer 5.1 , Helicon Remote v3.3.0 , AppZapp 3.7.1 , Delineate 0.5 , Mirror HD 1.0 , MyABCD , PicShare 1.0 , DOCtor 1.1.1 , Amadeus Pro v2.1.6 , EasyCloud Reader 1.22 , UPCEncoder 1.5 , Comic Collector 12.5.4.2413 , Tab Launcher |
|

Uninstall Spoiler Vulnerability From My Computer
Is your computer infected with Spoiler Vulnerability? Are you unable to do any task on your PC? If your answer is yes, get the quick guide that will help you to block this annoying malware infection fully from your system.
What Is Spoiler Vulnerability?
Spoiler Vulnerability is a severe malware which infects the PC by malicious activities. It spreads into the different versions of Windows based system and try to degrade the performance. It find its own way to sneak into the system and disable the antivirus program and firewall security. It modify the registry entries through the payloads. It has already damaged millions of PC in the world. It is also able to attach itself with removal device to invade from one computer to other.
How Spoiler Vulnerability Penetrates Into The System?
Spoiler Vulnerability intrude into your system through malicious websites which you surf online. Generally it contains the nasty code behind itself which get active when you surf or click on the link of the site. Spoiler Vulnerability easily invade into the system through this method. The other ways are unsafe network file transfer, fake software updates, misleading ads, spam mail attachments and etc.
Common Symptoms Of Spoiler Vulnerability
- Spoiler Vulnerability control the internet connection and modify DNS settings.
- It download other threats and viruses through the remote server without your authorization.
- It freeze the system and screen get blank.
- Most of the system programs fail to work and display unexpected error.
- It redirects the web searches to phishing or advertising websites.
- Malicious activities of Spoiler Vulnerability
- Spoiler Vulnerability help hackers to steal your private information. Your financial information also hacked by the hackers. They make profit by this procedure and your privacy will get disturb. This is very notorious threat which give malicious work environment on your PC.
Preventive Measures Of Spoiler Vulnerability
When you are installing the freeware, you should read the terms and condition at first. You should also use the advance or custom option before installing it. You can easily discard the installation process if there is no need to keep the freeware program on your desktop. Do not click the malicious link. Avoid to open the spam mail attachment which is generally send by the unknown senders. Regularly update the antivirus program and scan your computer. You can follow the guideline here to delete Spoiler Vulnerability completely from your computer.
Manual Spoiler Vulnerability Removal Guide
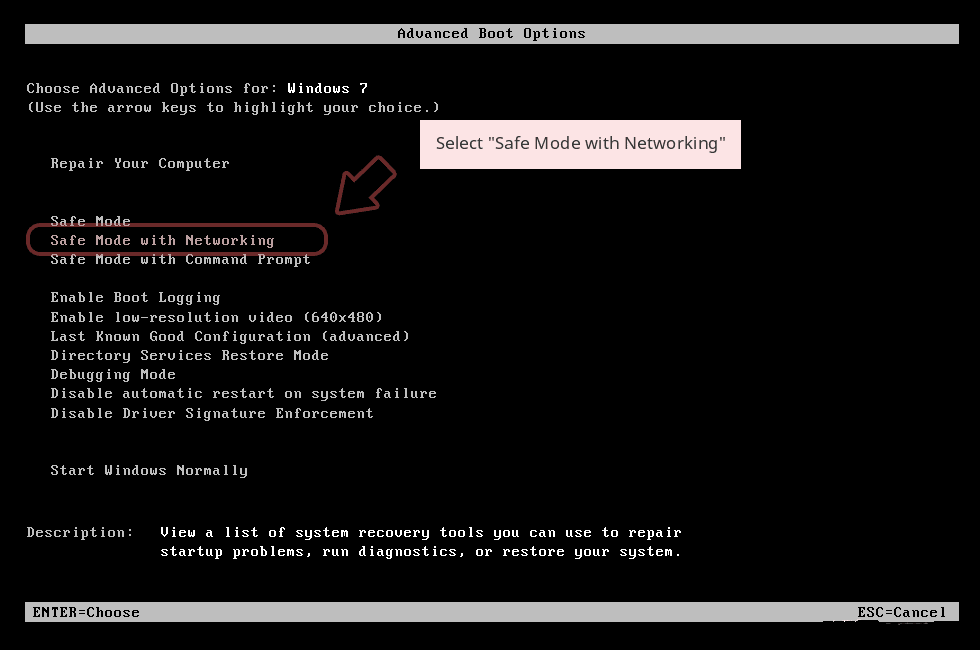
Step 1: How to Start your PC in Safe Mode with Networking to Get Rid of Spoiler Vulnerability
(For Win 7 | XP | Vista Users)
- first of all PC is to be rebooted in Safe Mode with Networking
- Select on Start Button and Click on Shutdown | Restart option and select OK
- when the PC restarts, keep tapping on F8 until you don’t get Advanced Boot Options.
- Safe Mode with Networking Option is to be selected from the list.
(For Win 8 | 8.1 | Win 10 Users)
- Click on Power Button near Windows Login Screen
- Keep Shift Button on the keyboard pressed and select Restart Option
- Now Select on Enable Safe Mode with Networking Option

In case Spoiler Vulnerability, is not letting your PC to Start in Safe Mode, then following Step is to followed
Step 2: Remove Spoiler Vulnerability Using System Restore Process
- PC need to be rebooted to Safe Mode with Command Prompt
- As soon as Command Prompt Window appear on the screen, select on cd restore and press on Enter option
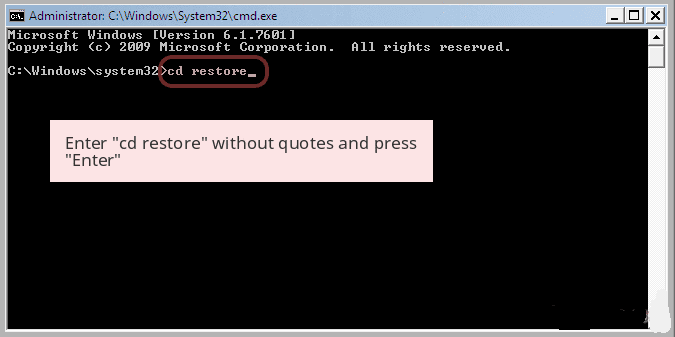
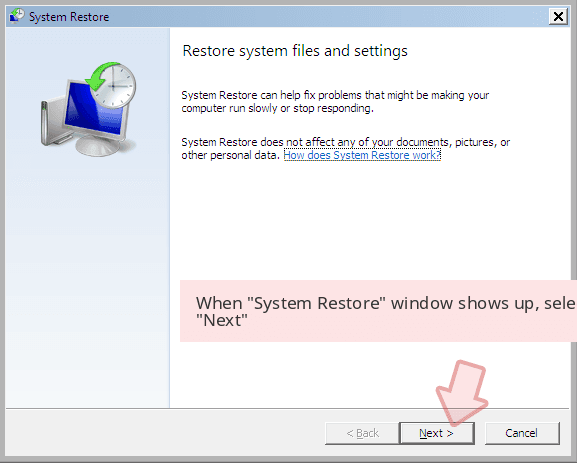
Type rstrui.exe and Click on Enter again.

Now users need to Click on Next option and Choose restore point that was the last time Windows was working fine prior to Spoiler Vulnerability infection. Once done, Click on Next button.
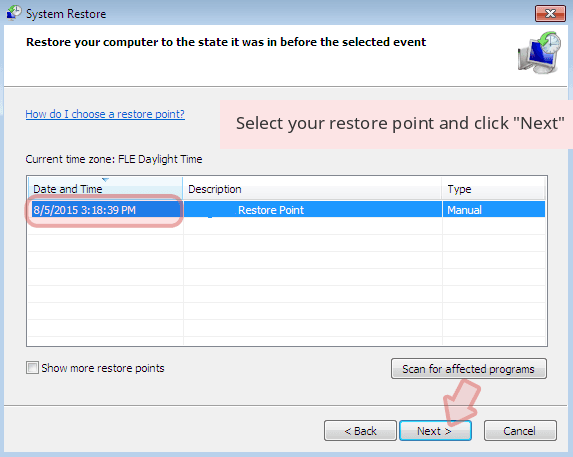
Select Yes to Restore your System and get rid of Spoiler Vulnerability infection.

However, if the above steps does not work to remove Spoiler Vulnerability, follow the below mentioned steps
Step:3 Unhide All Hidden Files and Folders to Delete Spoiler Vulnerability
How to View Spoiler Vulnerability Hidden Folders on Windows XP
- In order to show the hidden files and folders, you need to follow the given instructions:-
- Close all the Windows or minimize the opened application to go to desktop.
- Open “My Computer” by double-clicking on its icon.
- Click on Tools menu and select Folder options.
- Click on the View tab from the new Window.
- Check the Display contents of the system folders options.
- In the Hidden files and folders section, you need to put a check mark on Show hidden files and folders option.
- Click on Apply and then OK button. Now, close the Window.
- Now, you can see all the Spoiler Vulnerability related hidden files and folders on the system.

How to Access Spoiler Vulnerability Hidden folders on Windows Vista
- Minimize or close all opened tabs and go to Desktop.
- Go to the lower left of your screen, you will see Windows logo there, click on Start button.
- Go to Control Panel menu and click on it.
- After Control Panel got opened, there will two options, either “Classic View” or “Control Panel Home View”.
- Do the following when you are in “Classic View”.
- Double click on the icon and open Folder Options.
- Choose View tab.
- Again move to step 5.
- Do the following if you are “Control Panel Home View”.
- Hit button on Appearance and Personalization link.
- Chose Show Hidden Files or Folders.
- Under the Hidden File or Folder section, click on the button which is right next to the Show Hidden Files or Folders.
- Click on Apply button and then hit OK. Now, close the window.
- Now, to show you all hidden files or folders created by Spoiler Vulnerability, you have successfully considered Windows Vista.

How to Unhide Spoiler Vulnerability Created Folders on Windows 7
1. Go to the desktop and tap on the small rectangle which is located in the lower-right part of the system screen.
2. Now, just open the “Start” menu by clicking on the Windows start button which is located in the lower-left side of the PC screen that carries the windows logo.
3. Then after, look for the “Control Panel” menu option in the right-most row and open it.
4. When the Control Panel menu opens, then look for the “Folder Options” link.
5. Tap over the “View tab”.
6. Under the “Advanced Settings” category, double click on the “Hidden Files or Folders” associated with Spoiler Vulnerability.
7. Next, just select the check-box in order to Show hidden files, folders, or drives.
8. After this, click on “Apply” >> “OK” and then close the menu.
9. Now, the Windows 7 should be configured to show you all hidden files, folders or drives.

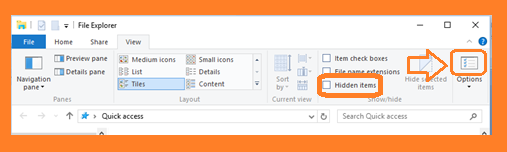
Steps to Unhide Spoiler Vulnerability related Files and Folders on Windows 8
- First of all, power on your Windows PC and click on start logo button that is found in left side of the system screen.
- Now, move to program lists and select control panel app.
- When Control panel is open completely, click on more settings option.
- After, you will see a Control panel Window and then you choose “Appearance and Personalization” tab.
- In Advance settings dialogue box, you need to tick mark on Show hidden files and folders and clear the check box for Hide protected system files.
- Click on Apply and Ok button. This apply option helps you to detect and eradicate all types of Spoiler Vulnerability related suspicious files.
- Finally, navigate your mouse cursor on close option to exit this panel.
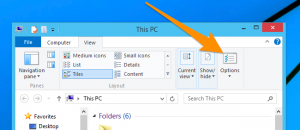
How to View Spoiler Vulnerability associated folders on Windows 10
1. Open the folder if you wish to unhide files.
2. Search and Click on View in Menu bar
3. In Menu click on to view folder options.
4. Again click on View and Enable Radio Button associated with Show hidden files created by Spoiler Vulnerability, folder and drive.
5. Press apply and OK.
Step 4: Press Start Key along with R- copy + paste the below stated command and Click on OK
notepad %windir%/system32/Drivers/etc/hosts
- This will open up a new file, in case if your system has been hacked, some IP’s will be shown at the bottom of the screen

Click on the Start Menu, Input “Control Panel” in the search box —> Select. Network and Internet —> Network and Sharing Center —> Next Change Adapter Settings. Right-click your Internet connection —> Select on Properties.
- In case if you find Suspicious IP in the local host –or if you are finding it difficult and have any problem then submit question to us and we will be happy to help you.


