
tk Ransomware – What is it ?
tk Ransomware is a highly disastrous malware threat crafted by potent cyber offenders with the sole motto of enticing rookie PC users and then earning profit from them. It very identical to various other vicious programs of the same group, intrudes itself very silently in the targeted system without being acknowledged by the users. This threat once done with the successful perforation, contributes numerous harassing issues in the system.
System security researchers have notified tk Ransomware initializing the implementation of several malicious practices via firstly acquiring control over whole system and then re-seizing it's default start up settings. Infection actually intentionally brought this particular alteration for the purpose of making itself capable enough of obtaining automatic activation in the system with each Windows reboot. Threat furthermore, besides from this, scan the entire system deeply in search of the files harmonious with it's corruption. Researchers have notified this infection capable of compromising wide range of file formats including images, MS office documents, PDF files, OpenOffice files, Music, Archives etc. It later then after finding files matching with it's target list, poses encryption operation onto them via making usage of a strong encryption algorithm (i.e., AES encryption method). This encryption usually renders the compromised files complete inaccessible to the users. It while carrying out encryption operation onto the PC's files, appends _'tkinter.pdb.' extension onto their respective ends.
tk Ransomware moreover following the successful accomplishment of the encryption operation, releases a ransom note in English language which simply indicates that the threat mainly targets the English speakers.
Released ransom note reads the following :
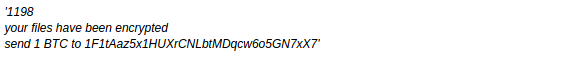
Note released in the case of this ransomware infection likewise those of released by several other threats of the same group, states that the PC's files have been victimized or enciphered and thus for the sake of their respective decryption, victims are required to make payment of certain amount of ransom money in Bitcoins. Now despite the fact that the generated note initially appears 100% genuine in nature, it is yet suggested neither to trust the generated note nor to make any payment and instead only concentrate onto the uninstallation of tk Ransomware from the system as PC experts have clearly proven it the single measure possible to the liberation of system as well as it's crucial files from all the aforementioned negative traits.
Propagation Tactics of tk Ransomware
tk Ransomware usually get distributed among user's PC through unprotected RDP configurations or via utilizing corrupted attachments in spam emails. It besides might get propagated through fraudulent downloads, web injections, exploits, injected installers and fake updates. Paying visit to several pornographic websites on regular basis also plays a very vital role in the dissemination of above mentioned ransomware threat inside system.
Free Scan your Windows PC to detect tk Ransomware
Free Scan your Windows PC to detect tk Ransomware
A: How To Remove tk Ransomware From Your PC
Step: 1 How to Reboot Windows in Safe Mode with Networking.
- Click on Restart button to restart your computer
- Press and hold down the F8 key during the restart process.
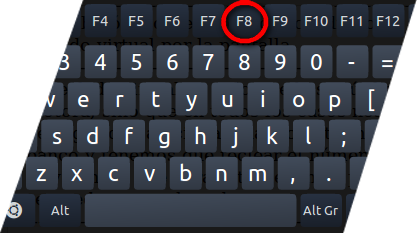
- From the boot menu, select Safe Mode with Networking using the arrow keys.
Step: 2 How to Kill tk Ransomware Related Process From Task Manager
- Press Ctrl+Alt+Del together on your keyboard

- It will Open Task manager on Windows
- Go to Process tab, find the tk Ransomware related Process.
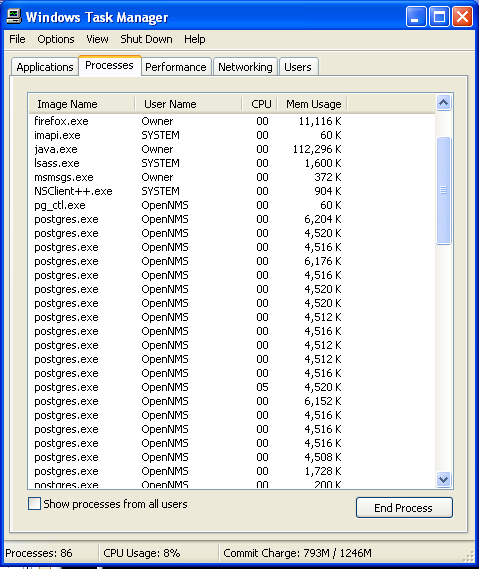
- Now click on on End Process button to close that task.
Step: 3 Uninstall tk Ransomware From Windows Control Panel
- Visit the Start menu to open the Control Panel.
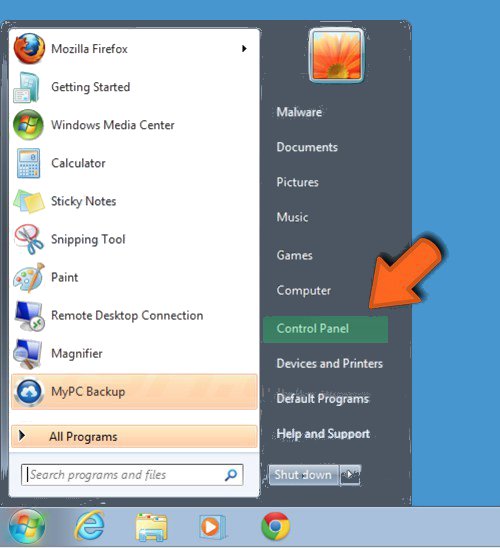
- Select Uninstall a Program option from Program category.
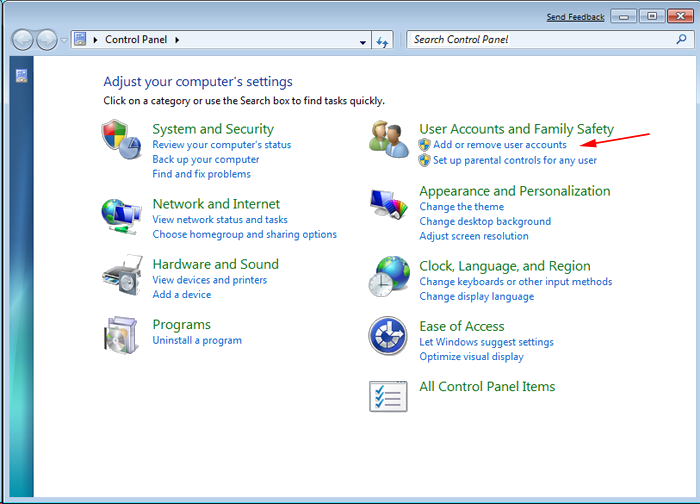
- Choose and remove all tk Ransomware related items from list.

B: How to Restore tk Ransomware Encrypted Files
Method: 1 By Using ShadowExplorer
After removing tk Ransomware from PC, it is important that users should restore encrypted files. Since, ransomware encrypts almost all the stored files except the shadow copies, one should attempt to restore original files and folders using shadow copies. This is where ShadowExplorer can prove to be handy.
Download ShadowExplorer Now
- Once downloaded, install ShadowExplorer in your PC
- Double Click to open it and now select C: drive from left panel
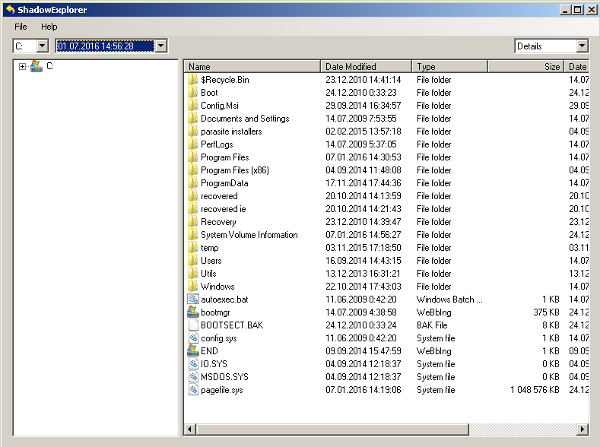
- In the date filed, users are recommended to select time frame of atleast a month ago
- Select and browse to the folder having encrypted data
- Right Click on the encrypted data and files
- Choose Export option and select a specific destination for restoring the original files
Method:2 Restore Windows PC to Default Factory Settings
Following the above mentioned steps will help in removing tk Ransomware from PC. However, if still infection persists, users are advised to restore their Windows PC to its Default Factory Settings.
System Restore in Windows XP
- Log on to Windows as Administrator.
- Click Start > All Programs > Accessories.

- Find System Tools and click System Restore
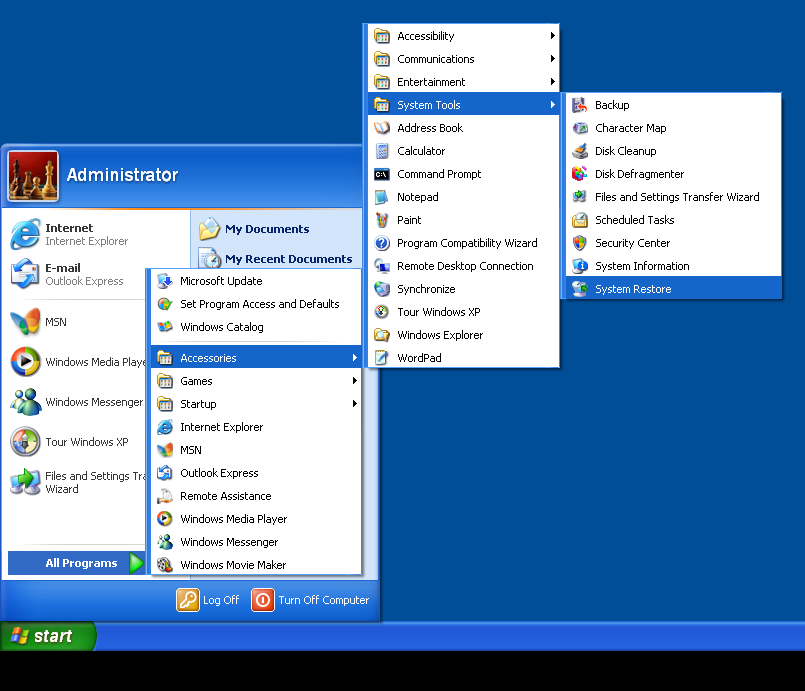
- Select Restore my computer to an earlier time and click Next.
- Choose a restore point when system was not infected and click Next.
System Restore Windows 7/Vista
- Go to Start menu and find Restore in the Search box.

- Now select the System Restore option from search results
- From the System Restore window, click the Next button.

- Now select a restore points when your PC was not infected.

- Click Next and follow the instructions.
System Restore Windows 8
- Go to the search box and type Control Panel

- Select Control Panel and open Recovery Option.

- Now Select Open System Restore option

- Find out any recent restore point when your PC was not infected.

- Click Next and follow the instructions.
System Restore Windows 10
- Right click the Start menu and select Control Panel.

- Open Control Panel and Find out the Recovery option.

- Select Recovery > Open System Restore > Next.

- Choose a restore point before infection Next > Finish.

Method:3 Using Data Recovery Software
Restore your files encrypted by tk Ransomware with help of Data Recovery Software
We understand how important is data for you. Incase the encrypted data cannot be restored using the above methods, users are advised to restore and recover original data using data recovery software.



