Based on the new investigation report, the security researchers at FireEye reported that the criminal hackers are now using the malicious Neptune Exploit Kit in order to proliferate Monero Miner cryptocurrency through a deceptive malvertising. Neptune Exploit Kit which is also known as Eris, Blaze and Terror exploit kit is exploiting by the cyber offenders that was first reported in the initial phase of year 2017. This exploit kit was regarded as a new variant of Sundown exploit kit, when it was appeared, due to the same malicious codes used by the hackers in these two EK.
Since the Angler Exploit was shut down in previous year, the activity of exploit kit has been on the decline. In addition to that, some famous redirect campaign using ElTest Gate and PseudoDarkleech Rig Exploit kit were also shut down in the mid of this year. Despite all this, the malvertising campaign involving the malicious exploit kits are remain active. Although, the Neptune Exploit Kit has relied heavily onto the malvertising and the website using this exploit to spread cryptocurrency Monero Mine are reported as:
- onlinesalesproaffiliate2[.]us
- onlinesalesproaffiliate5[.]us
- networkmarketingpro3[.]us
- onlinesalesproaffiliate4[.]us
- onlinesalesproaffiliate1[.]us
- onlinesalesproaffiliate6[.]us
- networkmarketingpro2[.]us
- onlinesalesproaffiliate3[.]us
Furthermore, the payloads used by the operators of an infamous Neptune Exploit Kit have since diversified. The security experts of FireEye have seen few changes in the behavior of this exploit kit, like malvertising campaigns, URI patterns and login account information associated with the payloads of cryptocurrency mining application propagates using the exploit kit. Since July 16th 2017, the researchers has observed few changes in the patterns of URI and at the time of writing this security article, the new campaign used by the con artists abuses a legitimate pop-up advertising service with suspicious redirects to adverts about the hiking clubs.

The browser redirects are considered unsafe which caused by the advertisements abused by criminal hackers. However, these ads uses 302 redirects in order to move targeted web surfers to web pages equipped with Neptune Exploit Kit. The websites responsible for this vicious attack may look like as a real and safe domain at first glance. Most of the adverts linked to this phishing campaign have been observed on some high-traffic torrent and the multimedia hosting websites. Such shady websites related with this exploit kit are hosted on IP address reported as 185.82.202.36 and 95.85.62.226. According to the research report, the malvertising portals spreading Neptune Exploit Kit are identified as:
- hxxp://nepalyogatrek[.]club
- hxxp://highspirittrecks[.]club
- hxxp://treknepal[.]club/
- hxxp://flvto[.]download
- hxxp://advnepaltrekking[.]club
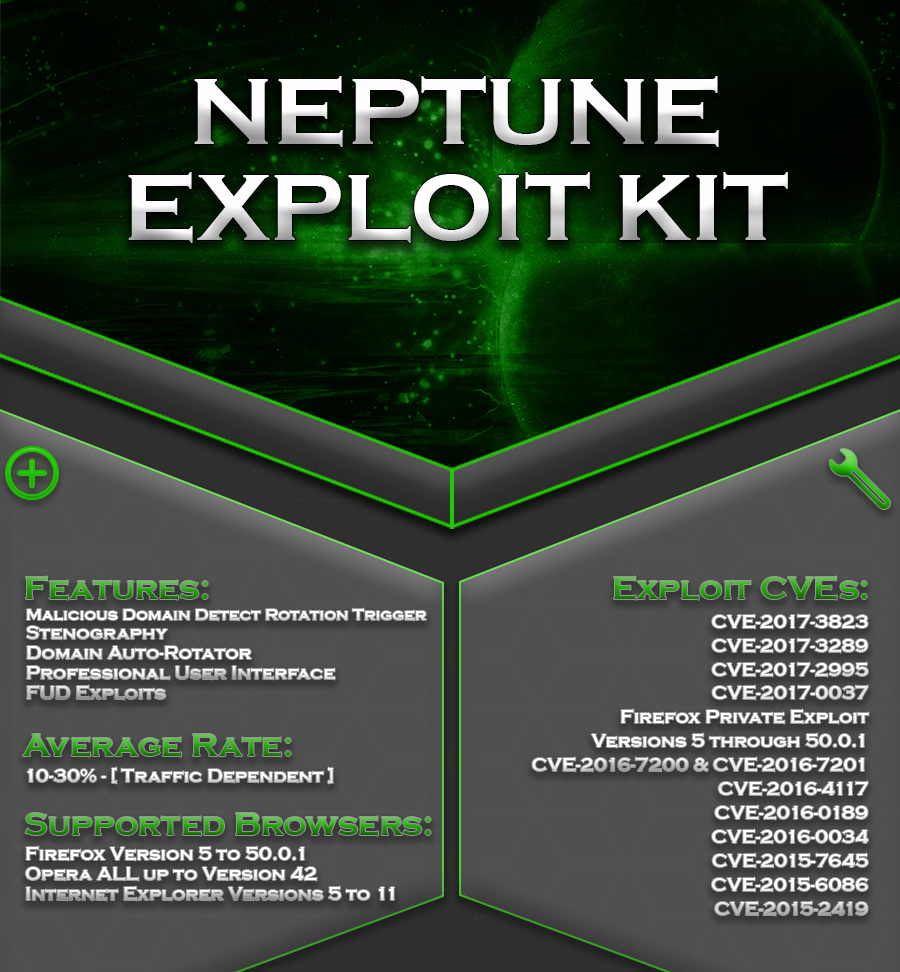
In case, if the Flash versions has been installed onto the targeted user's system, then the web pages responsible for distributing Neptune Exploit Kit redirects them to further Adobe Flash and HTML exploit links. Hence, by using this deceptive trick, the crooks exploits multiple vulnerabilities in just a single run. The exploit kit mainly uses two flash exploits and three exploits into the browser Internet Explorer and that are reported as:
- CVE-2014-6332 – Internet Explorer
- CVE-2015-2419 – Internet Explorer
- CVE-2016-0189 – Internet Explorer
- CVE-2015-7645 – Adobe Flash Player
- CVE-2015-8651 – Adobe Flash Player
