Alma Locker ransomware is a hazardous infection for the PC that is usually propagated among the PC via the RIG Exploit currently. It being discovered by Proofpoint researcher Darien Huss and firstly analyzed by Lawrence Abrams has been labeled as the one of the most advanced ransomware program than any other recent ransomware variants released in the past month. It following complete infiltration in the PC generates a unique ID number for the victim, derived from the serial number of the C:/ hard drive and the Mac address of the compromised PC. After that search all the drives on the targeted PC for files with certain file extensions and encrypts or locks them by making usage of AES-128 encryption algorithm. It while encrypting the files generates an extension made up of five random characters and add them to end of each of the encrypted file.
Alma Locker ransomware has been found capable of encrypting the below mentioned types of files –
.mdb, .mdf, .odb, .odc, .odm, .odp, .ods, .odt, .orf, .p12, .p7b, .p7c, .pdf, .pef, .pem, .pfx, .php, .png, .pps, .ppt, .pptm, .pptx, .psd, .1cd, .3ds, .3gp, .accdb, .ape, .asp, .aspx, .bc6, .bc7, .bmp, .cdr, .cer, .cfg, .cfgx, .cpp, .cr2, .crt, .crw, .csr, .csv, .dbf, .dbx, .dcr, .dfx, .dib, .djvu, .doc, .docm, .docx, .dwg, .dwt, .dxf, .dxg, .eps, .htm, .html, .ibank, .indd, .jfif, .jpe, .jpeg, .jpg, .kdc, .kwm, .max, .pst, .pub, .pwm, .qbb, .qbw, .raw, .rtf, .sln, .sql, .sqlite, .svg, .tif, .tiff, .txt, .vcf, .wallet, .wpd, .xls, .xlsm, .xlsx, .xml.
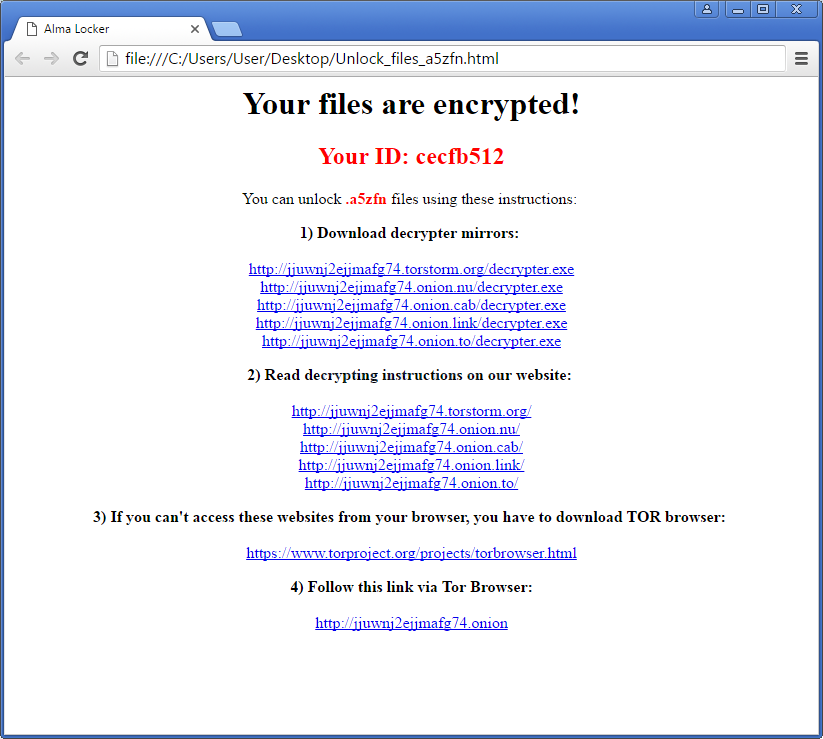
This ransomware after the completion of the encryption procedure, displays a ransom note on the screen containing links to a Tor-based website and downloads the decryption key. It unlike several other perilous ransomware infection, do not provide lots of details in the ransom note. Instead of that it only features links to the decryptor and the Tor browser. Now after this as the users complete the download phase and initializes the Alma Locker decrypter, more information on how to make the payment regarding the decryption is generated. Basically at this time, Bitcoin address i.e., the address where users need to pay the ransom and the total amount of ransom money required is listed.
Though generally it has been noticed that users in this kind of situation starts thinking that making payment is the only option for them to get their lost or encrypted files back and starts paying the asked amount of ransom money but it is strongly recommended not to do so as it has been proven payment will never provide them their files back. Instead it is just a trick played by cyber criminals to earn illegal money from rookie PC users. So, in this situation it is suggested to make usage of an effective antivirus program which can positively remove Alma Locker ransomware from the PC in an easy and efficient manner.
